Practice Free SY0-601 Exam Online Questions
Which of the following utilizes public and private keys to secure data?
- A . Password hash
- B . Block cipher
- C . Asymmetric encryption
- D . Steganography
A web architect would like to move a company’s website presence to the cloud. One of the management team’s key concerns is resiliency in case a cloud provider’s data center or network connection goes down.
Which of the following should the web architect consider to address this concern?
- A . Containers
- B . Virtual private cloud
- C . Segmentation
- D . Availability zones
D
Explanation:
Availability zones are the most appropriate cloud feature to address the concern of resiliency in case a cloud provider’s data center or network connection goes down. Availability zones are physically separate locations within an Azure region that have independent power, cooling, and networking. Each availability zone is made up of one or more data centers and houses infrastructure to support highly available, mission-critical applications. Availability zones are connected with high-speed, private fiber-optic networks. Azure services that support availability zones fall into two categories: Zonal services C you pin the resource to a specific zone (for example, virtual machines, managed disks, IP addresses), or Zone-redundant services C platform replicates automatically across zones (for example, zone-redundant storage, SQL Database). To achieve comprehensive business continuity on Azure, build your application architecture using the combination of availability zones with Azure region pairs. You can synchronously replicate your applications and data using availability zones within an Azure region for high-availability and asynchronously replicate across Azure regions for disaster recovery protection.
A company is implementing a new SIEM to log and send alerts whenever malicious activity is blocked by its antivirus and web content filters.
Which of the following is the primary use case for this scenario?
- A . Implementation of preventive controls
- B . Implementation of detective controls
- C . Implementation of deterrent controls
- D . Implementation of corrective controls
B
Explanation:
A Security Information and Event Management (SIEM) system is a tool that collects and analyzes security-related data from various sources to detect and respond to security incidents.
Reference: CompTIA Security+ Study Guide 601, Chapter 5
A security analyst is currently addressing an active cyber incident. The analyst has been able to identify affected devices that are running a malicious application with a unique hash.
Which of the following is the next step according to the incident response process?
- A . Recovery
- B . Lessons learned
- C . Containment
- D . Preparation
C
Explanation:
Containment is the next step according to the incident response process after identifying affected devices that are running a malicious application with a unique hash. Containment involves isolating the compromised devices or systems from the rest of the network to prevent the spread of the attack and limit its impact. Containment can be done by disconnecting the devices from the network, blocking network traffic to or from them, or applying firewall rules or access control lists. Containment is a critical step in incident response because it helps to preserve evidence for further analysis and remediation, and reduces the risk of data loss or exfiltration
https://www.fortinet.com/resources/cyberglossary/incident-response
https://www.ibm.com/topics/incident-response
A security practitioner is performing due diligence on a vendor that is being considered for cloud services.
Which of the following should the practitioner consult for the best insight into the current security posture of the vendor?
- A . PCI DSS standards
- B . SLA contract
- C . CSF framework
- D . SOC 2 report
D
Explanation:
A SOC 2 report is a document that provides an independent assessment of a service organization’s controls related to the Trust Services Criteria of Security, Availability, Processing Integrity, Confidentiality, or Privacy. A SOC 2 report can help a security practitioner evaluate the current security posture of a vendor that provides cloud services1.
A company is looking to move completely to a remote work environment. The Chief Information Security Officer is concerned about the improper use of company-owned devices when employees are working from home.
Which of the following could be implemented to ensure that devices are on the company-owned network?
- A . Internet proxy
- B . Always-on VPN
- C . Split tunneling
- D . OS firewall
B
Explanation:
Always-on VPN is a feature that enables the active VPN profile to connect automatically on certain triggers, such as user sign-in, network change, or device screen on. This ensures that the devices are always on the company-owned network and protected by the company’s security policies. Always-on VPN also prevents the devices from accessing the internet if the VPN connection is lost or interrupted
Several employees received a fraudulent text message from someone claiming to be the Chief Executive Officer (CEO).
The message stated:
‘Tm in an airport right now with no access to email. I need you to buy gift cards for employee recognition awards. Please send the gift cards to following email address.".
Which of the following are the best responses to this situation? (Select two).
- A . Cancel current employee recognition gift cards.
- B . Add a smishing exercise to the annual company training.
- C . Issue a general email warning to the company.
- D . Have the CEO change phone numbers.
- E . Conduct a forensic investigation on the CEO’s phone.
- F . Implement mobile device management.
A security administrator needs to add fault tolerance and load balancing to the connection from the file server to the backup storage.
Which of the following is the best choice to achieve this objective?
- A . Multipathing
- B . RAID
- C . Segmentation
- D . 8021.1
A
Explanation:
to achieve the objective of adding fault tolerance and load balancing to the connection from the file server to the backup storage is multipathing1. Multipathing is a technique that allows a system to use more than one path to access a storage device1. This can improve performance by distributing the workload across multiple paths, and also provide fault tolerance by switching to an alternative path if one path fails1. Multipathing can be implemented using software or hardware solutions1.
An information security officer at a credit card transaction company is conducting a framework-mapping exercise with the internal controls. The company recently established a new office in Europe.
To which of the following frameworks should the security officer map the existing controls’ (Select two).
- A . ISO
- B . PCI DSS
- C . SOC
- D . GDPR
- E . CSA
- F . NIST
B, D
Explanation:
PCI DSS (Payment Card Industry Data Security Standard) is a set of security standards and requirements for organizations that store, process, or transmit payment card data. It aims to protect cardholder data and prevent fraud and data breaches. GDPR (General Data Protection Regulation) is a regulation that governs the collection, processing, and transfer of personal data of individuals in the European Union. It aims to protect the privacy and rights of data subjects and impose obligations and penalties on data controllers and processors. These are the frameworks that the security officer should map the existing controls to, as they are relevant for a credit card transaction company that has a new office in Europe
While performing a threat-hunting exercise, a security analyst sees some unusual behavior occurring in an application when a user changes the display name.
The security analyst decides to perform a static code analysis and receives the following pseudocode:
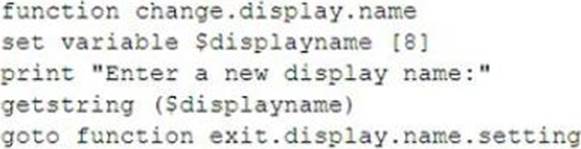
Which of the following attack types best describes the root cause of the unusual behavior?
- A . Server-side request forgery
- B . Improper error handling
- C . Buffer overflow
- D . SQL injection
D
Explanation:
SQL injection is one of the most common web hacking techniques. SQL injection is the placement of malicious code in SQL statements, via web page input12. A SQL injection attack consists of insertion or “injection” of a SQL query via the input data from the client to the application. A successful SQL injection exploit can read sensitive data from the database, modify database data (Insert/Update/Delete), execute administration operations on the database (such as shutdown the DBMS), recover the content of a given file present on the DBMS file system and in some cases issue commands to the operating system3.
According to the pseudocode given in the question, the application takes a user input for display name and concatenates it with a SQL query to update the user’s profile. This is a vulnerable practice that allows an attacker to inject malicious SQL code into the query and execute it on the database. For example, an attacker could enter something like this as their display name: John’; DROP TABLE users; —
This would result in the following SQL query being executed:
UPDATE profile SET displayname = ‘John’; DROP TABLE users; –‘ WHERE userid = 1;
The semicolon (;) terminates the original update statement and starts a new one that drops the users table. The double dash (C) comments out the rest of the query. This would cause a catastrophic loss of data for the application.
