Practice Free SY0-601 Exam Online Questions
An IT security team is concerned about the confidentiality of documents left unattended in MFPs.
Which of the following should the security team do to mitigate the situation?
- A . Educate users about the importance of paper shredder devices.
- B . Deploy an authentication factor that requires in-person action before printing.
- C . Install a software client in every computer authorized to use the MFPs.
- D . Update the management software to utilize encryption.
Which of the following BEST describes a technique that compensates researchers for finding vulnerabilities?
- A . Penetration testing
- B . Code review
- C . Wardriving
- D . Bug bounty
D
Explanation:
A bug bounty is a technique that compensates researchers for finding vulnerabilities in software or systems. A bug bounty program is an initiative that offers rewards, usually monetary, to ethical hackers who report security flaws to the owners or developers of the software or system. Bug bounty programs are often used by companies such as Meta (formerly Facebook), Google, Microsoft, and others to improve the security of their products and services
Bug bounty programs compensate researchers, often financially, for finding vulnerabilities in software, websites, or other technology. These programs provide an additional layer of security testing and incentivize researchers to report vulnerabilities instead of exploiting them.
A network engineer receives a call regarding multiple LAN-connected devices that are on the same switch. The devices have suddenly been experiencing speed and latency issues while connecting to network resources.
The engineer enters the command show mac address-table and reviews the following output
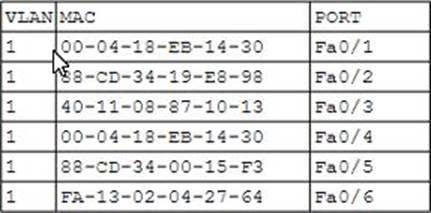
Which of the following best describes the attack that is currently in progress?
- A . MAC flooding
- B . Evil twin
- C . ARP poisoning
- D . DHCP spoofing
C
Explanation:
This is an attempt to redirect traffic to an attacking host by sending an ARP packet that contains the forged address of the next hop router. The attacker tricks the victim into believing that it is the legitimate router by sending a spoofed ARP reply with its own MAC address. This causes the victim to send all its traffic to the attacker instead of the router. The attacker can then intercept, modify, or drop the packets as they please.
Which of the following strategies shifts risks that are not covered in an organization’s risk strategy?
- A . Risk transference
- B . Risk avoidance
- C . Risk mitigation
- D . Risk acceptance
A cybersecurity administrator needs to implement a Layer 7 security control on a network and block potential attacks.
Which of the following can block an attack at Layer 7? (Select TWO).
- A . HIDS
- B . NIPS
- C . HSM
- D . WAF
- E . NAC
- F . NIDS
- G . Stateless firewall
DF
Explanation:
A WAF (Web Application Firewall) and NIDS (Network Intrusion Detection System) are both examples of Layer 7 security controls. A WAF can block attacks at the application layer (Layer 7) of the OSI model by filtering traffic to and from a web server. NIDS can also detect attacks at Layer 7 by monitoring network traffic for suspicious patterns and behaviors.
Reference: CompTIA Security+ Study Guide, pages 94-95, 116-118
Which of the following is constantly scanned by internet bots and has the highest risk of attack in the case of the default configurations?
- A . Wearable sensors
- B . Raspberry Pi
- C . Surveillance systems
- D . Real-time operating systems
C
Explanation:
Surveillance systems are constantly scanned by internet bots and have the highest risk of attack in the case of the default configurations because they are often connected to the internet and use weak or default passwords that can be easily guessed or cracked by malicious bots. Internet bots are software applications that run automated tasks over the internet, usually with the intent to imitate human activity or exploit vulnerabilities. Some bots are used for legitimate purposes, such as web crawling or indexing, but others are used for malicious purposes, such as spamming, phishing, denial-of-service attacks, or credential stuffing. Security misconfigurations are one of the most common gaps that criminal hackers look to exploit. Therefore, it is important to secure the configuration of surveillance systems by changing the default passwords, updating the firmware, disabling unnecessary services, and enabling encryption and authentication.
https://www.cctvcameraworld.com/setup-ip-camera-system-on-network/
An organization recently acquired an ISO 27001 certification.
Which of the following would MOST likely be considered a benefit of this certification?
- A . It allows for the sharing of digital forensics data across organizations
- B . It provides insurance in case of a data breach
- C . It provides complimentary training and certification resources to IT security staff.
- D . It certifies the organization can work with foreign entities that require a security clearance
- E . It assures customers that the organization meets security standards
E
Explanation:
ISO 27001 is an international standard that outlines the requirements for an Information Security Management System (ISMS). It provides a framework for managing and protecting sensitive information using risk management processes. Acquiring an ISO 27001 certification assures customers that the organization meets security standards and follows best practices for information security management. It helps to build customer trust and confidence in the organization’s ability to protect their sensitive information.
Reference: CompTIA Security+ Certification Exam Objectives, Exam Domain 1.0: Attacks, Threats, and Vulnerabilities, 1.2 Given a scenario, analyze indicators of compromise and determine the type of malware, p. 7
A systems administrator is working on a solution with the following requirements:
• Provide a secure zone.
• Enforce a company-wide access control policy.
• Reduce the scope of threats.
Which of the following is the systems administrator setting up?
- A . Zero Trust
- B . AAA
- C . Non-repudiation
- D . CIA
An endpoint protection application contains critical elements that are used to protect a system from infection.
Which of the following must be updated before completing a weekly endpoint check?
- A . Policy engine
- B . Policy updates
- C . Policy definitions
- D . Policy signatures
The Chief Information Security Officer wants to put security measures in place to protect Pll. The organization needs to use its existing labeling and classification system to accomplish this goal.
Which of the following would most likely be configured to meet the requirements?
- A . Tokenization
- B . S/MIME
- C . DLP
- D . MFA
