Practice Free SY0-601 Exam Online Questions
An analyst in the human resources organization is responsible for the quality of the company’s personnel data. The analyst maintains a data dictionary and ensures it is correct and up to date.
Which of the following best describes the role of the analyst?
- A . Data steward
- B . Data owner
- C . Data processor
- D . Data protection officer
To reduce and limit software and infrastructure costs the Chief Information Officer has requested to move email services to the cloud. The cloud provider and the organization must have secunty controls to protect sensitive data.
Which of the following cloud services would best accommodate the request?
- A . laaS
- B . PaaS
- C . DaaS
- D . SaaS
D
Explanation:
SaaS (Software as a Service) is a cloud model that provides clients with applications and software that are hosted and managed by a cloud provider over the internet. It can move email services to the cloud by allowing clients to access and use email applications without installing or maintaining them on their own devices or servers
A company wants to modify its current backup strategy to modify its current backup strategy to minimize the number of backups that would need to be restored in case of data loss.
Which of the following would be the BEST backup strategy
- A . Incremental backups followed by differential backups
- B . Full backups followed by incremental backups
- C . Delta backups followed by differential backups
- D . Incremental backups followed by delta backups
- E . Full backup followed by different backups
B
Explanation:
The best backup strategy for minimizing the number of backups that need to be restored in case of data loss is full backups followed by incremental backups. This strategy allows for a complete restoration of data by restoring the most recent full backup followed by the most recent incremental backup.
Reference: CompTIA Security+ Certification Guide, Third Edition (Exam SY0-601) page 126
A security operations technician is searching the log named /vax/messages for any events that were associated with a workstation with the IP address 10.1.1.1.
Which of the following would provide this information?
- A . cat /var/messages | grep 10.1.1.1
- B . grep 10.1.1.1 | cat /var/messages
- C . grep /var/messages | cat 10.1.1.1
- D . cat 10.1.1.1 | grep /var/messages
A
Explanation:
the cat command reads the file and streams its content to standard output. The | symbol connects the output of the left command with the input of the right command. The grep command returns all lines that match the regex. The cut command splits each line into fields based on a delimiter and extracts a specific field.
An organization wants to ensure the integrity of compiled binaries in the production environment.
Which of the following security measures would best support this objective?
- A . Input validation
- B . Code signing
- C . SQL injection
- D . Static analysis
An organization is concerned that ils hosted web servers are not running the most updated version of the software.
Which of the following would work best to help identify potential vulnerabilities?
- A . hping3 -S compcia.org -p 80
- B . nc -1 -v comptia.crg -p 80
- C . nmap comptia.org -p 80 -sv
- D . nslookup -port«80 comptia.org
C
Explanation:
nmap is a network scanning tool that can perform various tasks such as port scanning, service detection, version detection, OS detection, vulnerability scanning, etc… nmap comptia.org -p 80 -sv is a command that scans port 80 (the default port for HTTP) on comptia.org domain name and tries to identify the service name and version running on that port. This can help identify potential vulnerabilities in the web server software by comparing the version with known exploits or patches.
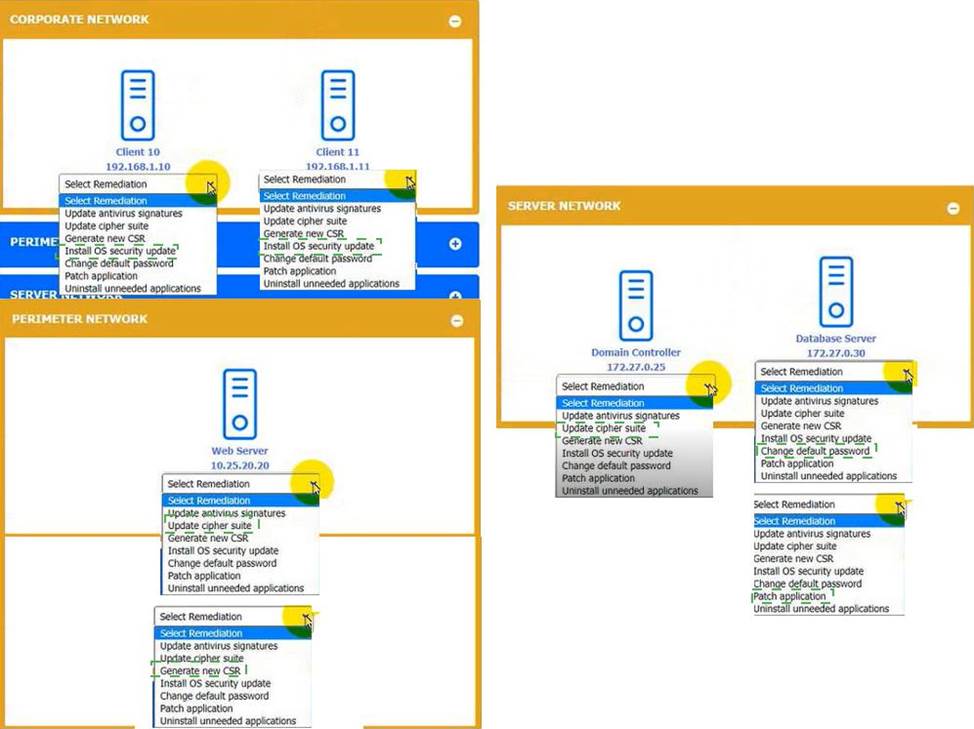
HOTSPOT
You received the output of a recent vulnerability assessment.
Review the assessment and scan output and determine the appropriate remedialion(s} ‘or «ach dewce.
Remediation options may be selected multiple times, and some devices may require more than one remediation.
If at any time you would like to biing bade the initial state ot the simulation, please dick me Reset All button.

Explanation:



Per company security policy, IT staff members are required to have separate credentials to perform administrative functions using just-in-time permissions.
Which of the following solutions is the company Implementing?
- A . Privileged access management
- B . SSO
- C . RADIUS
- D . Attribute-based access control
A
Explanation:
The company is implementing privileged access management, which provides just-in-time permissions for administrative functions.
A company was recently breached Pan of the company’s new cybersecurity strategy is to centralize? the togs horn all security devices.
Which of the following components forwards the logs to a central source?
- A . Log enrichment
- B . Log queue
- C . Log parser
- D . Log collector
D
Explanation:
A log collector is a component that forwards the logs from all security devices to a central source. A log collector can be a software tool or a hardware appliance that collects logs from various sources, such as firewalls, routers, servers, applications, or endpoints. A log collector can also perform functions such as log filtering, parsing, aggregation, normalization, and enrichment. A log collector can help centralize logging by sending the collected logs to a central log server or a security information and event management (SIEM) system for further analysis and correlation.
Reference:
https://www.comptia.org/certifications/security#examdetails
https://www.comptia.org/content/guides/comptia-security-sy0-601-exam-objectives
https://geekflare.com/open-source-centralized-logging/
A manufacturing company has several one-off legacy information systems that cannot be migrated to a newer OS due to software compatibility issues. The OSs are still supported by the vendor but the industrial software is no longer supported The Chief Information Security Officer has created a resiliency plan for these systems that will allow OS patches to be installed in a non-production environment, white also creating backups of the systems for recovery.
Which of the following resiliency techniques will provide these capabilities?
- A . Redundancy
- B . RAID 1+5
- C . Virtual machines
- D . Full backups
D
Explanation:
Virtual machines are software-based simulations of physical computers that run on a host system and share its resources. They can provide resiliency for legacy information systems that cannot be migrated to a newer OS due to software compatibility issues by allowing OS patches to be installed in a non-production environment without affecting the production environment. They can also create backups of the systems for recovery by taking snapshots or copies of the virtual machine files.
