Practice Free SY0-601 Exam Online Questions
A security analyst wants to verify that a client-server (non-web) application is sending encrypted traffic.
Which of the following should the analyst use?
- A . openssl
- B . hping
- C . netcat
- D . tcpdump
A
Explanation:
To verify that a client-server (non-web) application is sending encrypted traffic, a security analyst can use OpenSSL. OpenSSL is a software library that provides cryptographic functions, including encryption and decryption, in support of various security protocols, including SSL/TLS. It can be used to check whether a client-server application is using encryption to protect traffic.
Reference: CompTIA Security+ Certification Exam Objectives – Exam SY0-601
A security engineer is reviewing the logs from a SAML application that is configured to use MFA, during this review the engineer notices a high volume of successful logins that did not require MFA from users who were traveling internationally. The application, which can be accessed without a VPB, has a policy that allows time-based tokens to be generated. Users who changed locations should be required to reauthenticate but have been.
Which of the following statements BEST explains the issue?
- A . OpenID is mandatory to make the MFA requirements work
- B . An incorrect browser has been detected by the SAML application
- C . The access device has a trusted certificate installed that is overwriting the session token
- D . The user’s IP address is changing between logins, bur the application is not invalidating the token
A company is moving its retail website to a public cloud provider. The company wants to tokenize audit card data but not allow the cloud provider to see the stored credit card information.
Which of the following would BEST meet these objectives?
- A . WAF
- B . CASB
- C . VPN
- D . TLS
B
Explanation:
CASB stands for cloud access security broker, which is a software tool or service that acts as an intermediary between users and cloud service providers. CASB can help protect data stored in cloud services by enforcing security policies and controls such as encryption, tokenization, authentication, authorization, logging, auditing, and threat detection. Tokenization is a process that replaces sensitive data with non-sensitive substitutes called tokens that have no intrinsic value. Tokenization can help prevent data leakage by ensuring that only authorized users can access the original data using a tokenization system.
Reference:
https://www.comptia.org/certifications/security#examdetails
https://www.comptia.org/content/guides/comptia-security-sy0-601-exam-objectives
https://www.cisco.com/c/en/us/products/security/what
Which of the following would satisfy three-factor authentication requirements?
- A . Password, PIN, and physical token
- B . PIN, fingerprint scan, and ins scan
- C . Password, fingerprint scan, and physical token
- D . PIN, physical token, and ID card
C
Explanation:
Three-factor authentication combines three types of authentication methods: something you know (password), something you have (physical token), and something you are (fingerprint scan).
Option C satisfies these requirements, as it uses a password (something you know), a physical token (something you have), and a fingerprint scan (something you are) for authentication.
Reference: CompTIA Security+ Study Guide (SY0-601) 7th Edition by Emmett Dulaney, Chuck Easttom
Note: There could be other options as well that could satisfy the three-factor authentication requirements as per the organization’s security policies.
A security administrator checks the security logs of a Linux server and sees a lot of the following lines:

Which of the following is most likely being attempted?
- A . SQL injection attack
- B . Rainbow table attack
- C . Rootkit attack
- D . Brute-force attack
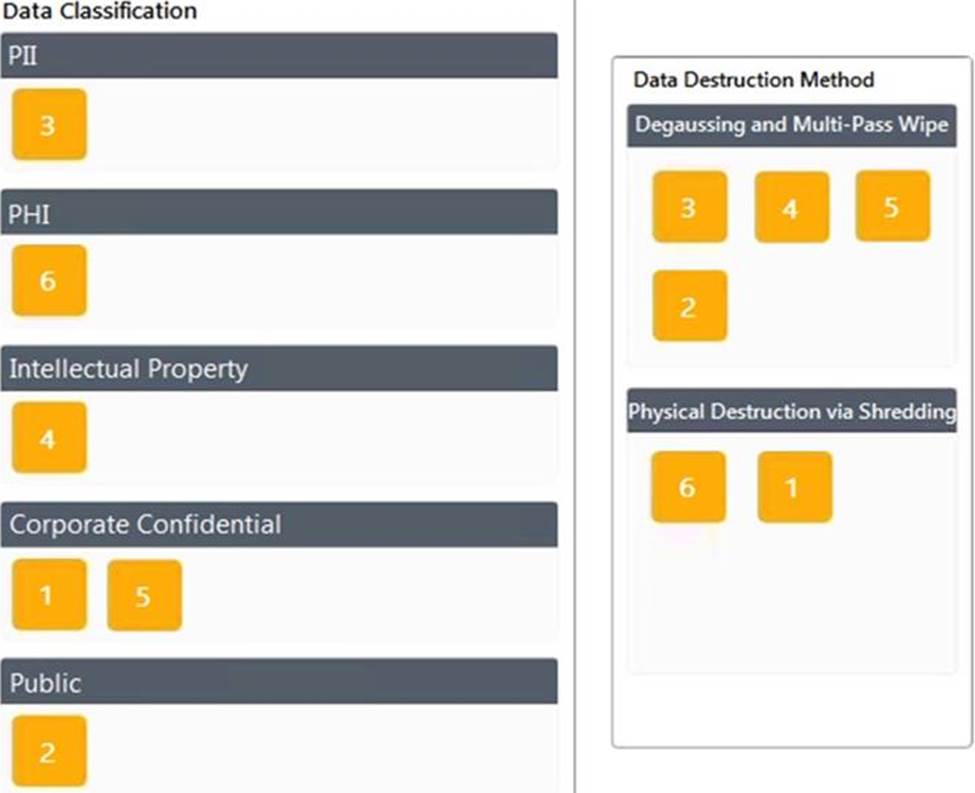
DRAG DROP
A data owner has been tasked with assigning proper data classifications and destruction methods for various types of data contained within the environment.

During an incident, a company’s CIRT determines it is necessary to observe the continued network-based transactions between a callback domain and the malware running on an enterprise PC.
Which of the following techniques would be BEST to enable this activity while reducing the nsk of lateral spread and the risk that the adversary would notice any changes?
- A . Physically move the PC to a separate Internet point of presence.
- B . Create and apply microsegmentation rules,
- C . Emulate the malware in a heavily monitored DMZ segment
- D . Apply network blacklisting rules for the adversary domain
C
Explanation:
Emulating the malware in a heavily monitored DMZ segment is the best option for observing network-based transactions between a callback domain and the malware running on an enterprise PC. This approach provides an isolated environment for the malware to run, reducing the risk of lateral spread and detection by the adversary. Additionally, the DMZ can be monitored closely to gather intelligence on the adversary’s tactics and techniques.
Reference: CompTIA Security+ Study Guide, page 129
A host was infected with malware. During the incident response. Joe, a user, reported that he did not receive any emails with links, but he had been browsing the internet all day.
Which of the following would most likely show where the malware originated?
- A . The DNS logs
- B . The web server logs
- C . The SIP traffic logs
- D . The SNMP logs
A
Explanation:
The web server logs are records of the requests and responses that occur between a web server and a web client, such as a browser. The web server logs can show where the malware originated by indicating the source IP address, the destination URL, the date and time, the HTTP status code, the user agent, etc., of each request and response. The web server logs can help the incident response team to trace back the malicious website that infected the host with malware.
Which of the following describes business units that purchase and implement scripting software without approval from an organization’s technology Support staff?
- A . Shadow IT
- B . Hacktivist
- C . Insider threat
- D . script kiddie
A
Explanation:
shadow IT is the use of IT-related hardware or software by a department or individual without the knowledge or approval of the IT or security group within the organization12. Shadow IT can encompass cloud services, software, and hardware. The main area of concern today is the rapid adoption of cloud-based services1.
According to one source3, shadow IT helps you know and identify which apps are being used and what your risk level is. 80% of employees use non-sanctioned apps that no one has reviewed, and may not be compliant with your security and compliance policies.
Which of the following incident response phases should the proper collection of the detected ‘ocs and establishment of a chain of custody be performed before?
- A . Containment
- B . Identification
- C . Preparation
- D . Recovery
A
Explanation:
Containment is the phase where the incident response team tries to isolate and stop the spread of the incident12. Before containing the incident, the team should collect and preserve any evidence that may be useful for analysis and investigation12. This includes documenting the incident details, such as date, time, location, source, and impact12. It also includes establishing a chain of custody, which is a record of who handled the evidence, when, where, how, and why3. A chain of custody ensures the integrity and admissibility of the evidence in court or other legal proceedings3.
