Practice Free SY0-601 Exam Online Questions
A company a "right to forgotten" request To legally comply, the company must remove data related to the requester from its systems.
Which Of the following Company most likely complying with?
- A . NIST CSF
- B . GDPR
- C . PCI OSS
- D . ISO 27001
B
Explanation:
GDPR stands for General Data Protection Regulation, which is a law that regulates data protection and privacy in the European Union (EU) and the European Economic Area (EEA). GDPR also applies to the transfer of personal data outside the EU and EEA areas. GDPR grants individuals the right to request the deletion or removal of their personal data from an organization’s systems under certain circumstances. This right is also known as the “right to be forgotten” or the “right to erasure”. An organization that receives such a request must comply with it within a specified time frame, unless there are legitimate grounds for retaining the data.
Reference:
https://www.comptia.org/certifications/security#examdetails
https://www.comptia.org/content/guides/comptia-security-sy0-601-exam-objectives
https://gdpr-info.eu/issues/right-to-be-forgotten/
A company is working with a vendor to perform a penetration test.
Which of the following includes an estimate about the number of hours required to complete the engagement?
- A . SOW
- B . BPA
- C . SLA
- D . NDA
A security analyst receives a SIEM alert that someone logged in to the app admin test account, which is only used for the early detection of attacks.
The security analyst then reviews the following application log:

Which of the following can the security analyst conclude?
- A . A replay attack is being conducted against the application.
- B . An injection attack is being conducted against a user authentication system.
- C . A service account password may have been changed, resulting in continuous failed logins within the application.
- D . A credentialed vulnerability scanner attack is testing several CVEs against the application.
A
Explanation:
A replay attack is a type of network attack where an attacker captures and retransmits a valid data transmission, such as a login request, to gain unauthorized access or impersonate a legitimate user. In this case, the attacker may have captured the credentials of the app admin test account and used them to log in to the application. The application log shows multiple failed login attempts from different IP addresses, which indicates a replay attack.
Security analysts are conducting an investigation of an attack that occurred inside the organization’s network. An attacker was able to coiled network traffic between workstations throughout the network.
The analysts review the following logs:

The Layer 2 address table has hundreds of entries similar to the ones above.
Which of the following attacks has most likely occurred?
- A . SQL injection
- B . DNS spoofing
- C . MAC flooding
- D . ARP poisoning
A systems administrator wants to add a second factor to the single sign-on portal that the organization uses. Currently, only a username and password are required.
Which of the following should the administrator implement to best meet this requirement?
- A . Personal verification questions
- B . Software-based TOTP
- C . Log-in image checks
- D . Secondary PIN code
A security team suspects that the cause of recent power consumption overloads is the unauthorized use of empty power outlets in the network rack.
Which of the following options will mitigate this issue without compromising the number of outlets available?
- A . Adding a new UPS dedicated to the rack
- B . Installing a managed PDU
- C . Using only a dual power supplies unit
- D . Increasing power generator capacity
B
Explanation:
Installing a managed PDU is the most appropriate option to mitigate the issue without compromising the number of outlets available. A managed Power Distribution Unit (PDU) helps monitor, manage, and control power consumption at the rack level. By installing a managed PDU, the security team will have greater visibility into power usage in the network rack, and they can identify and eliminate unauthorized devices that consume excessive power from empty outlets. https://www.comptia.org/training/books/security-sy0-601-study-guide
A security administrator is hardening corporate systems and applying appropriate mitigations by consulting a real-world knowledge base for adversary behavior.
Which of the following would be best for the administrator to reference?
- A . MITRE ATT&CK
- B . CSIRT
- C . CVSS
- D . SOAR
A security analyst inspects the following log:
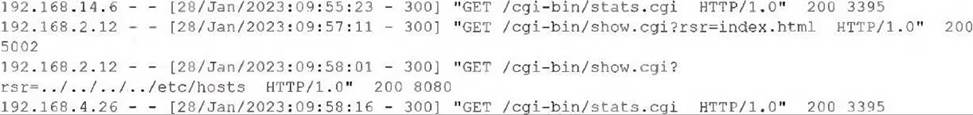
Which of the following was attempted?
- A . Command injection
- B . Buffer overflow
- C . Privilege escalation
- D . Directory traversal
An administrator reviewed the log files after a recent ransomware attack on a company’s system and discovered vulnerabilities that resulted in the loss of a database server. The administrator applied a patch to the server to resolve the CVE score.
Which of the following controls did the administrator use?
- A . Corrective
- B . Deterrent
- C . Compensating
- D . Directive
Which of the following best describes when an organization Utilizes a read-to-use application from a cloud provider?
- A . IaaS
- B . SaaS
- C . PaaS
- D . XaaS
B
Explanation:
SaaS stands for software as a service, which is a cloud computing model that provides ready-to-use applications over the internet. SaaS applications are hosted and managed by a cloud provider who also handles software updates, maintenance, security, and scalability. SaaS users can access the applications through a web browser or a mobile app without installing any software on their devices. SaaS applications are typically offered on a subscription or pay-per-use basis. Examples of SaaS applications include email services, online office suites, customer relationship management (CRM) systems, and video conferencing platforms.
Reference:
https://www.comptia.org/certifications/security#examdetails
https://www.comptia.org/content/guides/comptia-security-sy0-601-exam-objectives
https://www.ibm.com/cloud/learn/software-as-a-service
