Practice Free SC-300 Exam Online Questions
Topic 1, Litware, Inc
Overview
Litware, Inc. is a pharmaceutical company that has a subsidiary named fabrikam, inc Litware has offices in Boston and Seattle, but has employees located across the United States. Employees connect remotely to either office by using a VPN connection.
Identity Environment
The network contains an Active Directory forest named litware.com that is linked to an Azure Active Directory (Azure AD) tenant named litware.com. Azure AD Connect uses pass-through authentication and has password hash synchronization disabled. Litware.com contains a user named User1 who oversees all application development.
Litware implements Azure AD Application Proxy.
Fabrikam has an Azure AD tenant named fabrikam.com. The users at Fabrikam access the resources in litware.com by using guest accounts in the litware.com tenant.
Cloud Environment
All the users at Litware have Microsoft 365 Enterprise E5 licenses. All the built-in anomaly detection polices in Microsoft Cloud App Security are enabled.
Litware has an Azure subscription associated to the litware.com Azure AD tenant. The subscription contains an Azure Sentinel instance that uses the Azure Active Directory connector and the Office 365 connector. Azure Sentinel currently collects the Azure AD sign-ins logs and audit logs.
On-premises Environment
The on-premises network contains the severs shown in the following table.
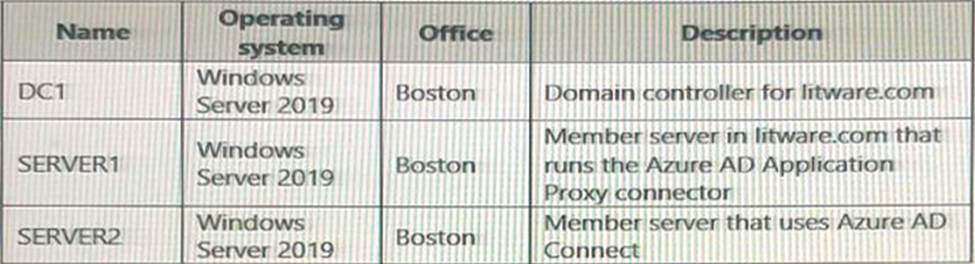
Both Litware offices connect directly to the internet. Both offices connect to virtual networks in the Azure subscription by using a site-to-site VPN connection. All on-premises domain controllers are prevented from accessing the internet.
Delegation Requirements
Litware identifies the following delegation requirements:
* Delegate the management of privileged roles by using Azure AD Privileged Identity Management (PIM).
* Prevent nonprivileged users from registering applications in the litware.com Azure AD tenant-
* Use custom catalogs and custom programs for Identity Governance.
* Ensure that User1 can create enterprise applications in Azure AD. Use the principle of least privilege.
Licensing Requirements
Litware recently added a custom user attribute named LWLicenses to the litware.com Active Directory forest. Litware wants to manage the assignment of Azure AD licenses by
modifying the value of the LWLicenses attribute. Users who have the appropriate value for LWLicenses must be added automatically to Microsoft 365 group that he appropriate license assigned.
Management Requirement
Litware wants to create a group named LWGroup1 will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Authentication Requirements
Litware identifies the following authentication requirements:
• Implement multi-factor authentication (MFA) for all Litware users.
• Exempt users from using MFA to authenticate to Azure AD from the Boston office of Litware.
• Implement a banned password list for the litware.com forest.
• Enforce MFA when accessing on-premises applications.
• Automatically detect and remediate externally leaked credentials
Access Requirements
Litware wants to create a group named LWGroup1 that will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Monitoring Requirements
Litware wants to use the Fusion rule in Azure Sentinel to detect multi-staged that include a combination of suspicious Azure AD sign-ins followed by anomalous Microsoft Office 365 activity.
You need to meet the authentication requirements for leaked credentials.
What should you do?
- A . Enable federation with PingFederate in Azure AD Connect.
- B . Configure Azure AD Password Protection.
- C . Enable password hash synchronization in Azure AD Connect.
- D . Configure an authentication method policy in Azure AD.
C
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/security/fundamentals/steps-secure-identity
You need to resolve the issue of the sales department users.
What should you configure for the Azure AD tenant?
- A . the User settings
- B . the Device settings
- C . the Access reviews settings
- D . Security defaults
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that has an Azure Active Directory Premium Plan 2 license.
The tenant contains the users shown in the following table.
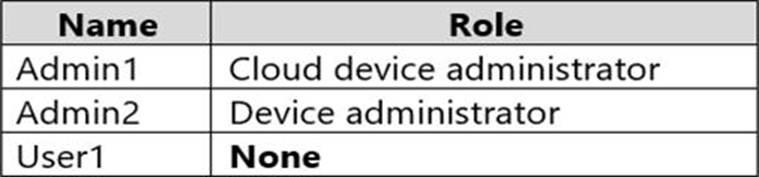
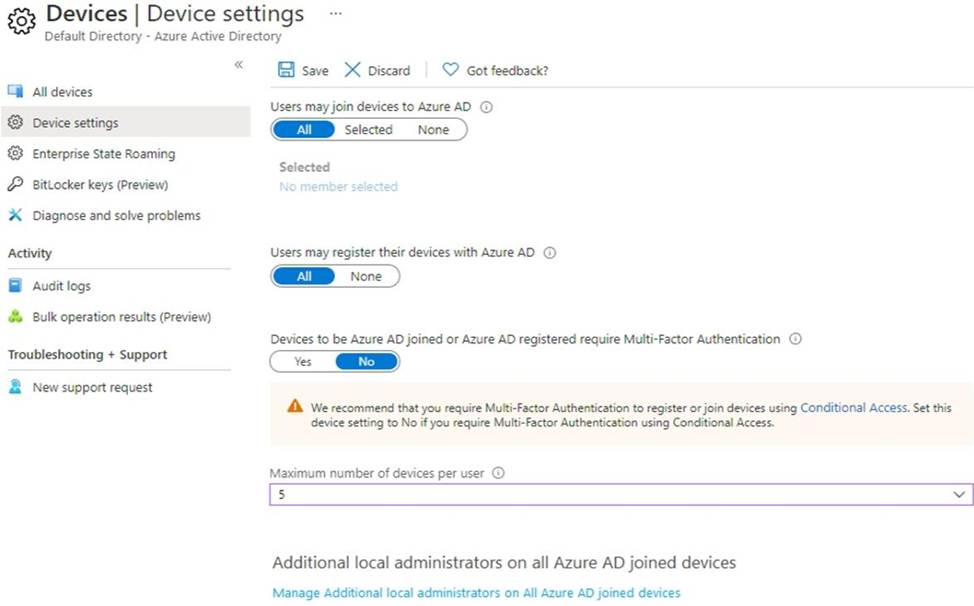
You have the Device Settings shown in the following exhibit.
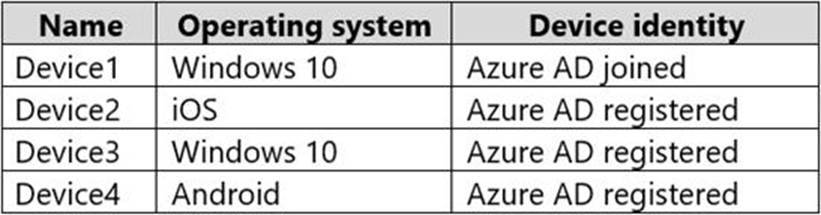
User1 has the devices shown in the following table.
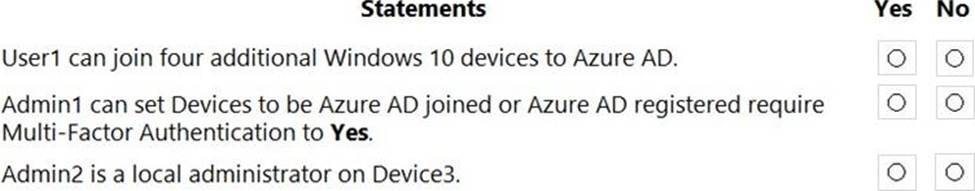
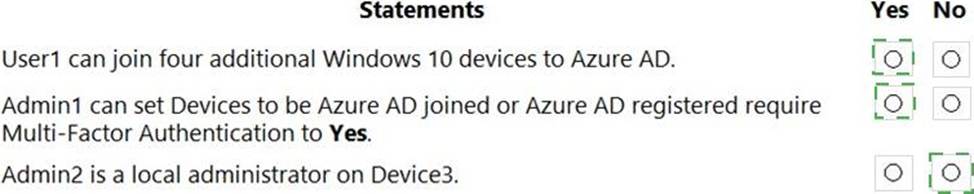
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Explanation:
Box 1: Yes
Users may join 5 devices to Azure AD.
Box 2: Yes
Box 3: No
An additional local device administrator has not been applied
Reference: https://docs.microsoft.com/en-us/azure/active-directory/devices/device-management-azure-portal
SIMULATION
Task 3
You need to add the Linkedln application as a resource to the Sales and Marketing access package.
The solution must NOT remove any other resources from the access package.
Sign in to the Microsoft Entra admin center:
Ensure you have the role of Global Administrator or Identity Governance Administrator.
Navigate to Entitlement Management:
Go to Identity governance > Entitlement management > Access packages1.
Select the Sales and Marketing access package:
Find and select the Sales and Marketing access package to modify it.
Add a new resource:
Within the access package details, select Resources.
Click on + Add resource.
Search for and select the LinkedIn application from the list of available resources.
Configure the resource role:
Assign the appropriate role for the LinkedIn application that users in the Sales and Marketing access package will have.
Review and update the access package:
Ensure that the LinkedIn application has been added as a resource.
Confirm that no other resources have been removed from the access package.
Save the changes:
After reviewing, save the changes to the access package.
Communicate the update:
Notify the relevant users about the addition of the LinkedIn application to their access package.
By following these steps, you will successfully add the LinkedIn application to the Sales and Marketing access package without affecting the other resources.
SIMULATION
Task 6
You need to implement additional security checks before the members of the Sg-Executive can access any company apps.
The members must meet one of the following conditions:
• Connect by using a device that is marked as compliant by Microsoft Intune.
• Connect by using client apps that are protected by app protection policies.
Here’s a step-by-step guide:
Sign in to the Microsoft Entra admin center:
Ensure you have the role of Global Administrator or Security Administrator.
Navigate to Conditional Access:
Go to Security > Conditional Access.
Create a new policy:
Select + New policy.
Name the policy appropriately, such as “Sg-Executive Security Checks”.
Assign the policy to the Sg-Executive group:
Under Assignments, select Users and groups.
Choose Select users and groups and then Groups.
Search for and select the Sg-Executive group.
Define the application control conditions:
Under Cloud apps or actions, select All cloud apps to apply the policy to any company app.
Set the device compliance requirement:
Under Conditions > Device state, configure the policy to include devices marked as compliant by Microsoft Intune.
Set the app protection policy requirement:
Under Conditions > Client apps, configure the policy to include client apps that are protected by app protection policies.
Configure the access controls:
Under Access controls > Grant, select Grant access.
Choose Require device to be marked as compliant and Require approved client app.
Ensure that the option Require one of the selected controls is enabled.
Enable the policy:
Set Enable policy to On.
Review and save the policy:
Review all settings to ensure they meet the requirements.
Click Create to save and implement the policy.
By following these steps, you will ensure that the Sg-Executive group members can only access company apps if they meet one of the specified conditions, either by using a compliant device or a protected client app. This enhances the security posture of your organization by enforcing stricter access controls for executive-level users.
You plan to deploy a new Azure AD tenant.
Which multifactor authentication (MFA) method will be enabled by default for the tenant?
- A . Microsoft Authenticator
- B . SMS
- C . voice call
- D . email OTP
HOTSPOT
You have a Microsoft 365 E5 subscription.
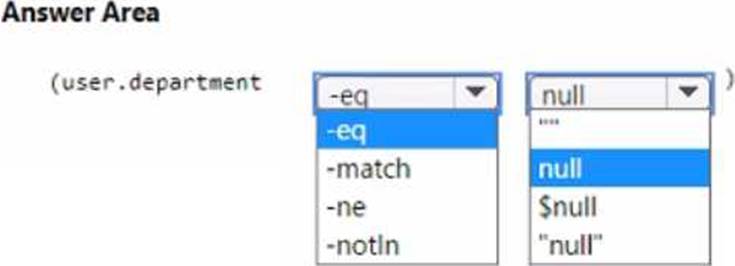
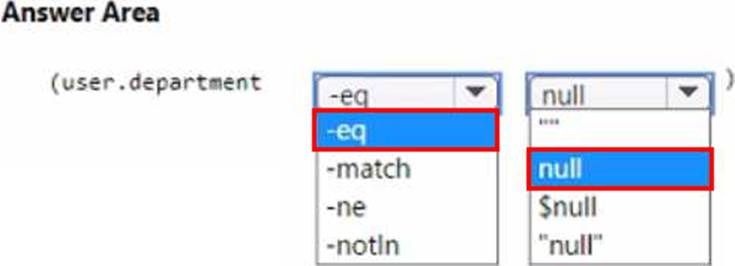
You need to create a dynamic user group that will include all the users that do NOT have a department defined in their user profile.
How should you complete the membership rule? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains an Azure SQL database named db1.
You deploy an Azure App Service web app named App1 that provide product information to users that connect to App1 anonymously.
You need to provide App1 with Access to db1.
The solution must meet the following requirements:
* Credentials must only be available to App1.
* Administrative effort must be minimized.
Which type of credentials should you use?
- A . a user-assigned managed identity
- B . an Azure AD user account
- C . A SQL Server account
- D . a system-assigned managed identity
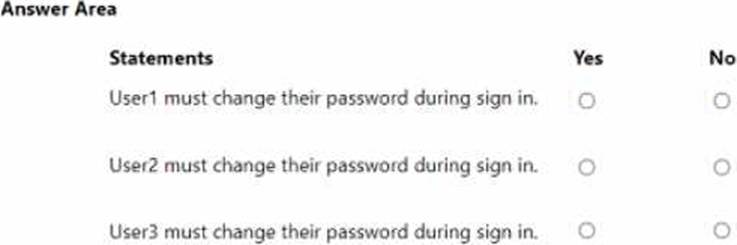
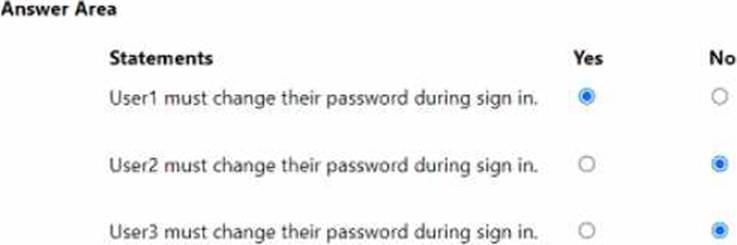
HOTSPOT
You have a Microsoft Entra tenant that contains the users shown in the following table.
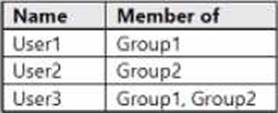
You have a user risk policy that has the following settings:
• Assignments:
o Include: Group1
o Exclude: Group2
• Sign-in risk Medium and above
• Access controls:
o Grant access: Require password change
When the users attempt to sign in. user risk levels are detected as shown in the following table.
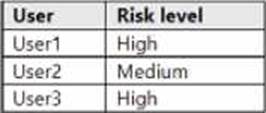
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
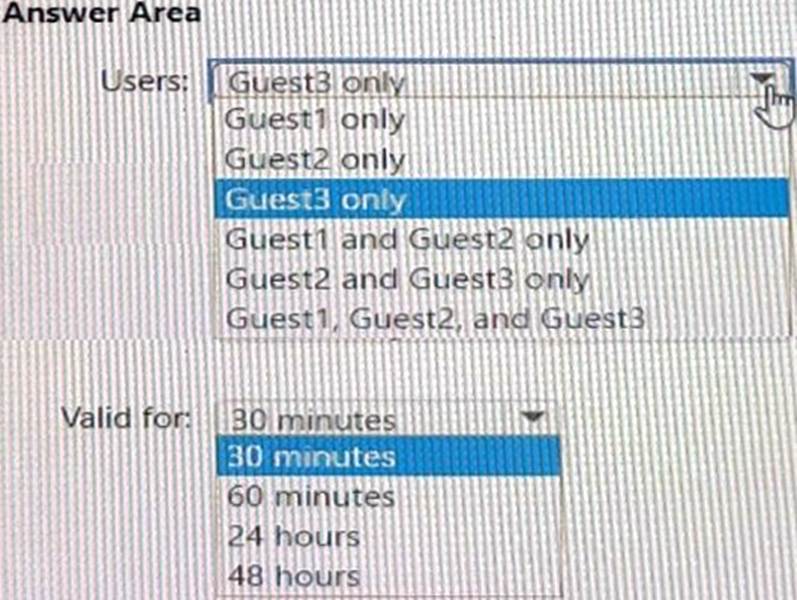
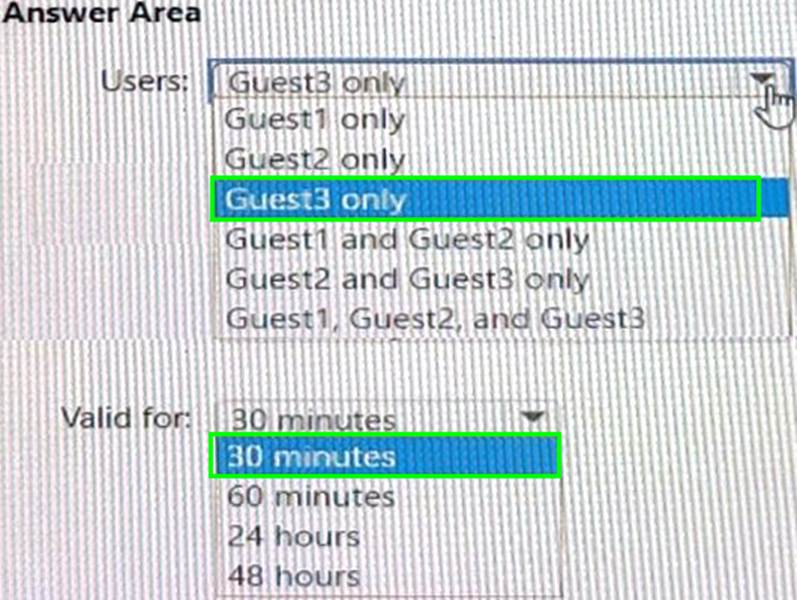
HOTSPOT
You have an Azure AD tenant named contoso.com that has Email one-time passcode for guests set to Yes.
You invite the guest users shown in the following table.
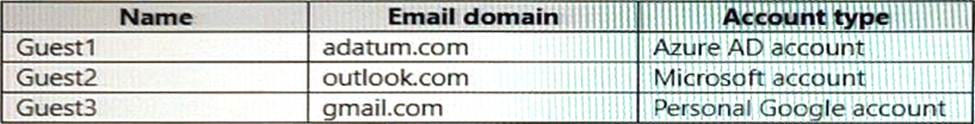
Which users will receive a one-time passcode, and how long will the passcode be valid? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.