Practice Free PCCSE Exam Online Questions
Which resource and policy type are used to calculate AWS Net Effective Permissions? (Choose two.)
- A . Service Linked Roles
- B . Lambda Function
- C . Amazon Resource Names (ARNs) using Wild Cards
- D . AWS Service Control Policies (SCPs)
Prisma Cloud supports sending audit event records to which three targets? (Choose three.)
- A . SNMP Traps
- B . Stdout
- C . Netflow
- D . Prometheus
- E . Syslog
Given this information:
The Console is located at https://prisma-console.mydomain.local The username is: cluster
The password is: password123
The image to scan is: myimage:latest
Which twistcli command should be used to scan a Container for vulnerabilities and display the details about each vulnerability?
- A . twistcli images scan –console-address https://prisma-console.mydomain.local -u cluster -p password123 — details myimage:latest
- B . twistcli images scan –console-address prisma-console.mydomain.local -u cluster -p password123 – – vulnerability-details myimage:latest
- C . twistcli images scan –address prisma-console.mydomain.local -u cluster -p password123 — vulnerability- details myimage:latest
- D . twistcli images scan –address https://prisma-console.mydomain.local -u cluster -p password123 — details myimage:latest
An administrator wants to install the Defenders to a Kubernetes cluster. This cluster is running the console on the default service endpoint and will be exporting to YAML.
Console Address: $CONSOLE_ADDRESS Websocket Address: $WEBSOCKET_ADDRESS User:
$ADMIN_USER
Which command generates the YAML file for Defender install?
- A . <PLATFORM>/twistcli defender
–address $CONSOLE_ADDRESS
–user $ADMIN_USER
–cluster-address $CONSOLE_ADDRESS - B . <PLATFORM>/twistcli defender export kubernetes
–address $WEBSOCKET_ADDRESS
–user $ADMIN_USER
–cluster-address $CONSOLE_ADDRESS - C . <PLATFORM>/twistcli defender YAML kubernetes
–address $CONSOLE_ADDRESS
–user $ADMIN_USER
–cluster-address $WEBSOCKET_ADDRESS - D . <PLATFORM>/twistcli defender export kubernetes
–address $CONSOLE_ADDRESS
–user $ADMIN_USER
–cluster-address $WEBSOCKET_ADDRESS
In which two ways can Prisma Cloud images be retrieved in Prisma Cloud Compute Self-Hosted Edition? (Choose two.)
- A . Pull the images from the Prisma Cloud registry without any authentication.
- B . Authenticate with Prisma Cloud registry, and then pull the images from the Prisma Cloud registry.
- C . Retrieve Prisma Cloud images using URL auth by embedding an access token.
- D . Download Prisma Cloud images from github.paloaltonetworks.com.
In which two ways can Prisma Cloud images be retrieved in Prisma Cloud Compute Self-Hosted Edition? (Choose two.)
- A . Pull the images from the Prisma Cloud registry without any authentication.
- B . Authenticate with Prisma Cloud registry, and then pull the images from the Prisma Cloud registry.
- C . Retrieve Prisma Cloud images using URL auth by embedding an access token.
- D . Download Prisma Cloud images from github.paloaltonetworks.com.
Which IAM Azure RQL query would correctly generate an output to view users who have sufficient permissions to create security groups within Azure AD and create applications?
- A . config where api.name = ‘azure-active-directory-authorization-policy’ AND son.rule = defaultUserRolePermissions.allowedToCreateSecurityGroups is true and defaultUserRolePermissions.allowedToCreateApps is true
- B . config from cloud.resource where api.name = ‘azure-active-directory-authorization-policy’ AND json.rule = defaultUserRolePermissions exists
- C . config from network where api.name = ‘azure-active-directory-authorization-policy’ AND json.rule = defaultUserRolePermissions.allowedToCreateSecurityGroups is false and defaultUserRolePermissions.allowedToCreateApps is true
- D . config from cloud.resource where api.name = ‘azure-active-directory-authorization-policy’ AND json.rule = defaultUserRolePermissions.allowedToCreateSecurityGroups is true and defaultUserRolePermissions.allowedToCreateApps is true
Which two information types cannot be seen in the data security dashboard? (Choose two).
- A . Bucket owner
- B . Object Data Profile by Region
- C . Top Publicly Exposed Objects By Data Profile
- D . Object content
- E . Total objects
Which policy type should be used to detect and alert on cryptominer network activity?
- A . Audit event
- B . Anomaly
- C . Config-build
- D . Config-run
Based on the following information, which RQL query will satisfy the requirement to identify VM hosts deployed to organization public cloud environments exposed to network traffic from the internet and affected by Text4Shell RCE (CVE-2022-42889) vulnerability?
• Network flow logs from all virtual private cloud (VPC) subnets are ingested to the Prisma Cloud Enterprise Edition tenant.
• All virtual machines (VMs) have Prisma Cloud Defender deployed.
A)
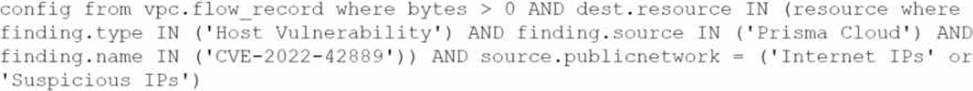
B)
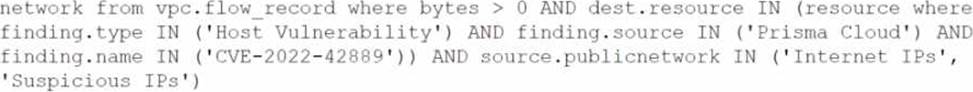
C)
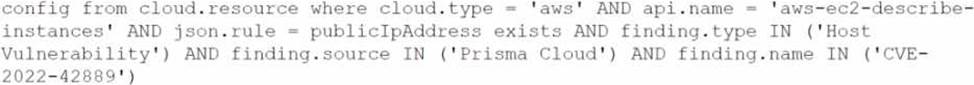
D)
![]()
- A . Option A
- B . Option B
- C . Option C
- D . Option D
