Practice Free PCCSE Exam Online Questions
An administrator has a requirement to ingest all Console and Defender logs to Splunk.
Which option will satisfy this requirement in Prisma Cloud Compute?
- A . Enable the API settings for logging.
- B . Enable the CSV export in the Console.
- C . Enable the syslog option in the Console
- D . Enable the Splunk option in the Console.
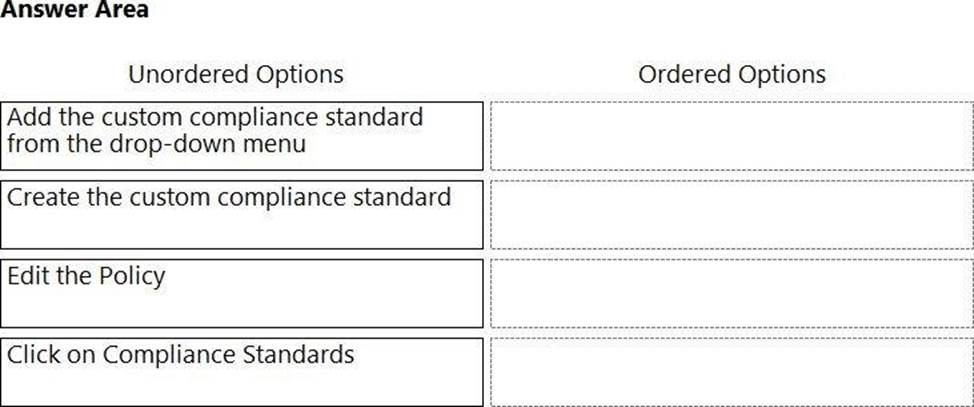
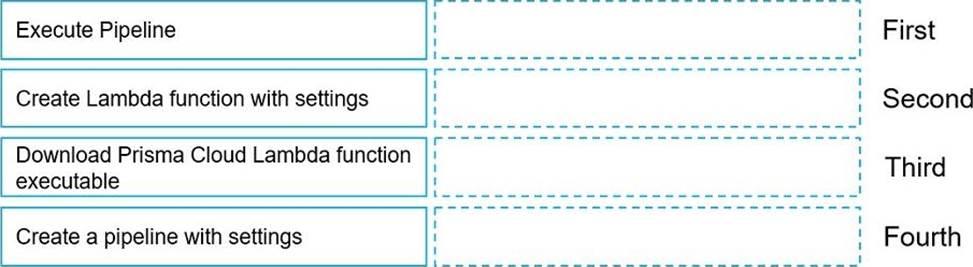
DRAG DROP
Move the steps to the correct order to set up and execute a serverless scan using AWS DevOps.
Which two integrations enable ingesting host findings to generate alerts? (Choose two.)
- A . Splunk
- B . Tenable
- C . JIRA
- D . Qualys
In Azure, what permissions need to be added to Management Groups to allow Prisma Cloud to calculate net effective permissions?
- A . Microsoft.Management/managementGroups/descendants/read
- B . Microsoft.Management/managementGroups/descendants/calculate
- C . PaloAltoNetworks.PrismaCloud/managementGroups/descendants/read
- D . PaloAltoNetworks.PrismaCloud/managementGroups/
A customer wants to harden its environment from misconfiguration.
Prisma Cloud Compute Compliance enforcement for hosts covers which three options? (Choose three.)
- A . Docker daemon configuration files
- B . Docker daemon configuration
- C . Host cloud provider tags
- D . Host configuration
- E . Hosts without Defender agents
An administrator for Prisma Cloud needs to obtain a graphical view to monitor all connections, including connections across hosts and connections to any configured network objects.
Which setting does the administrator enable or configure to accomplish this task?
- A . ADEM
- B . WAAS Analytics
- C . Telemetry
- D . Cloud Native Network Firewall
- E . Host Insight
Which three AWS policy types and identities are used to calculate the net effective permissions? (Choose three).
- A . AWS service control policies (SCPs)
- B . AWS IAM group
- C . AWS IAM role
- D . AWS IAM User
- E . AWS IAM tag policy
Which type of compliance check is available for rules under Defend > Compliance > Containers and Images > CI?
- A . Host
- B . Container
- C . Functions
- D . Image
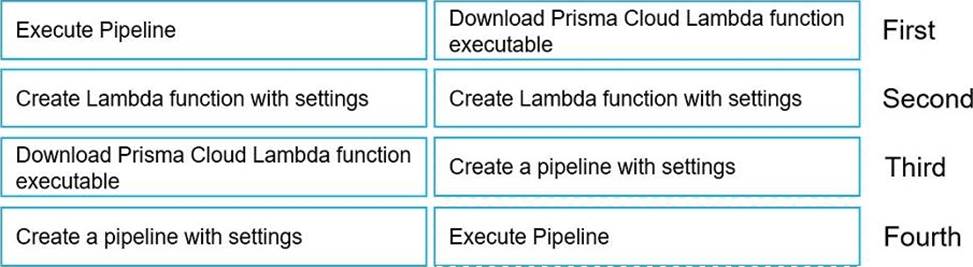
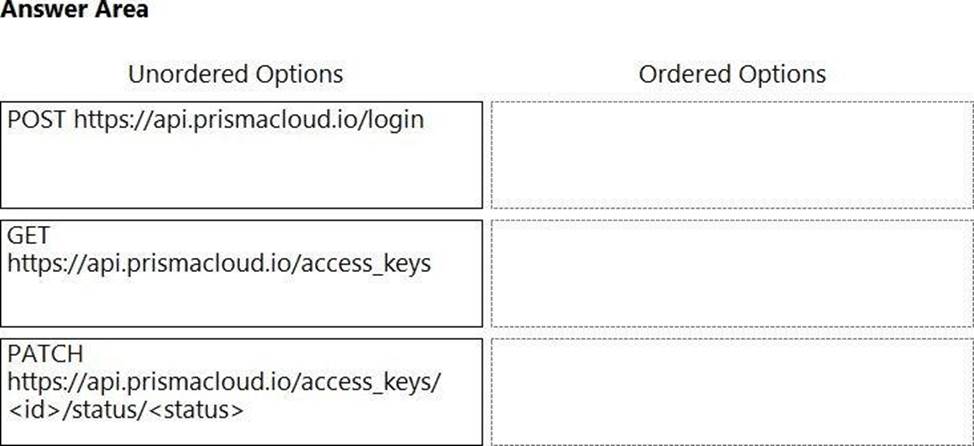
DRAG DROP
An administrator needs to write a script that automatically deactivates access keys that have not been used for 30 days.
In which order should the API calls be used to accomplish this task? (Drag the steps into the correct order from the first step to the last.)
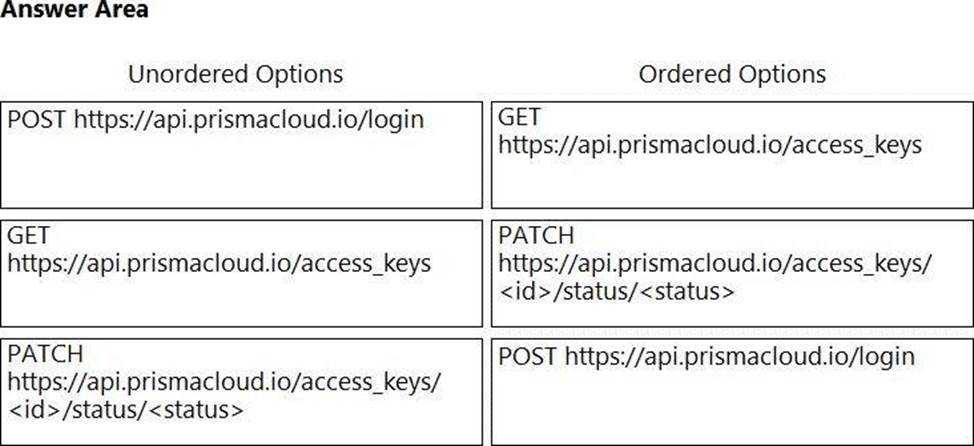
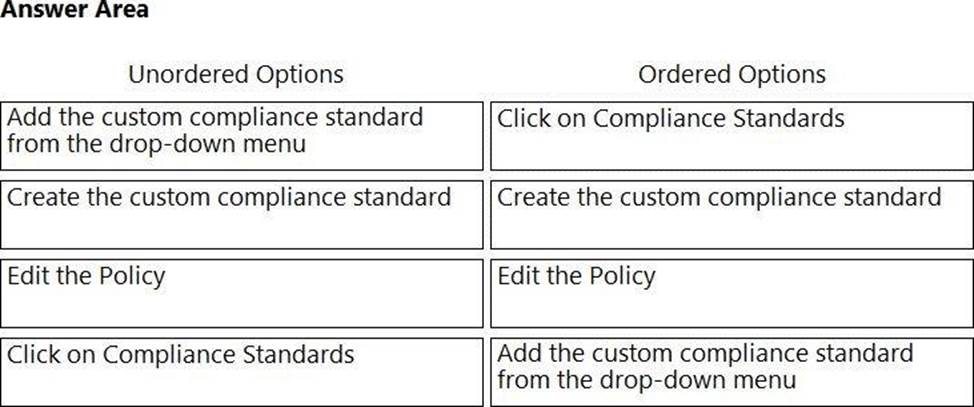
DRAG DROP
Which order of steps map a policy to a custom compliance standard? (Drag the steps into the correct order of occurrence, from the first step to the last.)