Practice Free PCCSE Exam Online Questions
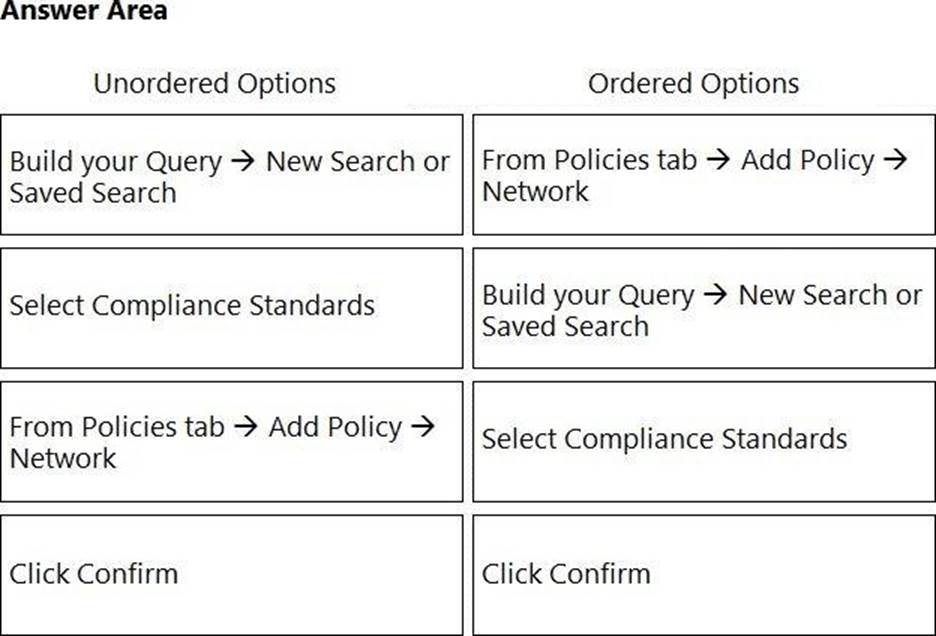
DRAG DROP
What is the order of steps to create a custom network policy? (Drag the steps into the correct order of occurrence, from the first step to the last.)
Which two proper agentless scanning modes are supported with Prisma Cloud? (Choose two).
- A . Spoke Account Mode
- B . Hub Account Mode
- C . Same Account Mode
- D . Main Account Mode
Which ban for DoS protection will enforce a rate limit for users who are unable to post five (5) “. tar.gz" files within five (5) seconds?
- A . One with an average rate of 5 and file extensions match on “. tar.gz" on Web Application and API Security (WAAS)
- B . One with an average rate of 5 and file extensions match on “. tar.gz" on Cloud Native Network Firewall (CNNF)
- C . One with a burst rate of 5 and file extensions match on “. tar.gz" on Web Application and API Security (WAAS) *
- D . One with a burst rate of 5 and file extensions match on “. tar.gz" on Cloud Native Network Firewall (CNNF)
Create an Alert rule
A DevOps lead reviewed some system logs and notices some odd behavior that could be a data exfiltration attempt. The DevOps lead only has access to vulnerability data in Prisma Cloud Compute, so the DevOps lead passes this information to SecOps.
Which pages in Prisma Cloud Compute can the SecOps lead use to investigate the runtime aspects of this attack?
- A . The SecOps lead should investigate the attack using Vulnerability Explorer and Runtime Radar.
- B . The SecOps lead should use Incident Explorer and Compliance Explorer.
- C . The SecOps lead should use the Incident Explorer page and Monitor > Events > Container Audits.
- D . The SecOps lead should review the vulnerability scans in the CI/CD process to determine blame.
A DevOps lead reviewed some system logs and notices some odd behavior that could be a data exfiltration attempt. The DevOps lead only has access to vulnerability data in Prisma Cloud Compute, so the DevOps lead passes this information to SecOps.
Which pages in Prisma Cloud Compute can the SecOps lead use to investigate the runtime aspects of this attack?
- A . The SecOps lead should investigate the attack using Vulnerability Explorer and Runtime Radar.
- B . The SecOps lead should use Incident Explorer and Compliance Explorer.
- C . The SecOps lead should use the Incident Explorer page and Monitor > Events > Container Audits.
- D . The SecOps lead should review the vulnerability scans in the CI/CD process to determine blame.
What are the two ways to scope a CI policy for image scanning? (Choose two.)
- A . container name
- B . image name
- C . hostname
- D . image labels
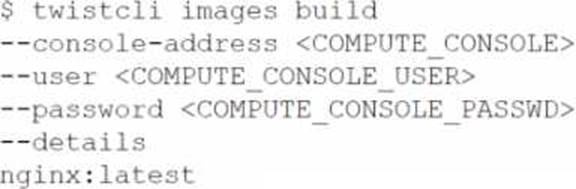
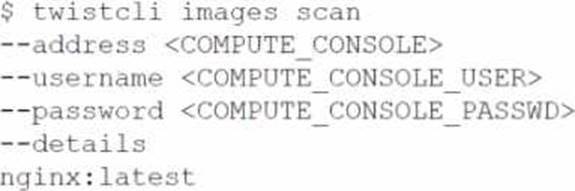
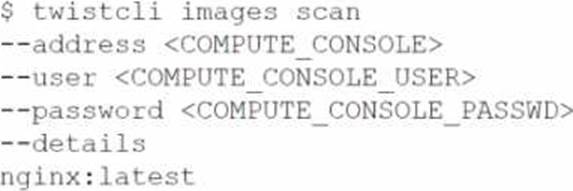
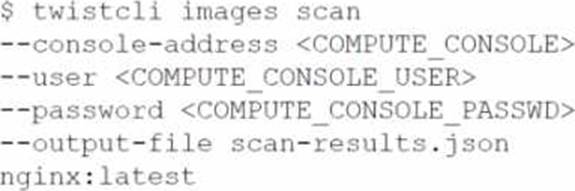
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
C)
D)
- A . Option A
- B . Option B
- C . Option C
- D . Option D
Which statement accurately characterizes SSO Integration on Prisma Cloud?
- A . Prisma Cloud supports IdP initiated SSO, and its SAML endpoint supports the POST and GET methods.
- B . Okta, Azure Active Directory, PingID, and others are supported via SAML.
- C . An administrator can configure different Identity Providers (IdP) for all the cloud accounts that Prisma Cloud monitors.
- D . An administrator who needs to access the Prisma Cloud API can use SSO after configuration.
Which component(s), if any, will Palo Alto Networks host and run when a customer purchases Prisma Cloud Enterprise Edition?
- A . Defenders
- B . Console
- C . Jenkins
- D . twistcli