Practice Free PCCSE Exam Online Questions
An administrator wants to enforce a rate limit for users not being able to post five (5) .tar.gz files within five (5) seconds.
What does the administrator need to configure?
- A . A ban for DoS protection with an average rate of 5 and file extensions match on .tar.gz on WAAS
- B . A ban for DoS protection with a burst rate of 5 and file extensions match on .tar.gz on CNNF
- C . A ban for DoS protection with a burst rate of 5 and file extensions match on .tar gz on WAAS
- D . A ban for DoS protection with an average rate of 5 and file extensions match on .tar.gz on CNNF
Which three types of buckets exposure are available in the Data Security module? (Choose three.)
- A . Public
- B . Private
- C . International
- D . Differential
- E . Conditional
Which three types of buckets exposure are available in the Data Security module? (Choose three.)
- A . Public
- B . Private
- C . International
- D . Differential
- E . Conditional
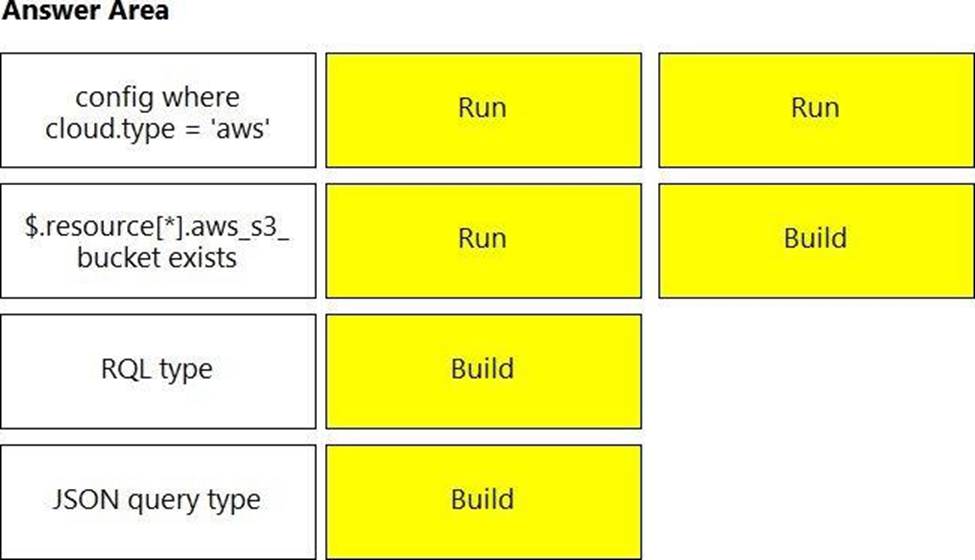
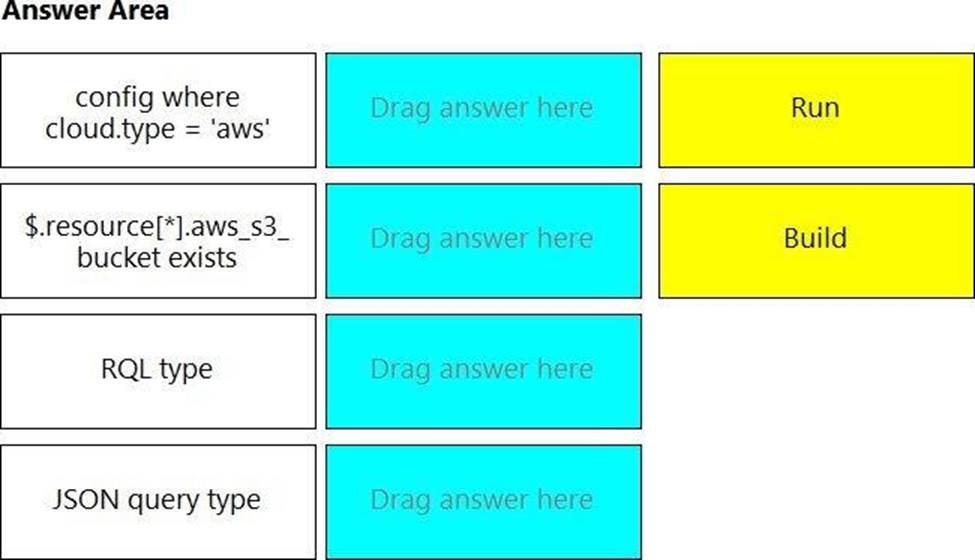
DRAG DROP
You wish to create a custom policy with build and run subtypes.
Match the query types for each example. (Select your answer from the pull-down list. Answers may be used more than once or not at all.)
A security team notices a number of anomalies under Monitor > Events. The incident response team works with the developers to determine that these anomalies are false positives.
What will be the effect if the security team chooses to Relearn on this image?
- A . The model is deleted, and Defender will relearn for 24 hours.
- B . The anomalies detected will automatically be added to the model.
- C . The model is deleted and returns to the initial learning state.
- D . The model is retained, and any new behavior observed during the new learning period will be added to the existing model.
A security team notices a number of anomalies under Monitor > Events. The incident response team works with the developers to determine that these anomalies are false positives.
What will be the effect if the security team chooses to Relearn on this image?
- A . The model is deleted, and Defender will relearn for 24 hours.
- B . The anomalies detected will automatically be added to the model.
- C . The model is deleted and returns to the initial learning state.
- D . The model is retained, and any new behavior observed during the new learning period will be added to the existing model.
Which three incident types will be reflected in the Incident Explorer section of Runtime Defense? (Choose three.)
- A . Crypto miners
- B . Brute Force
- C . Cross-Site Scripting
- D . Port Scanning
- E . SQL Injection
Which step is included when configuring Kubernetes to use Prisma Cloud Compute as an admission controller?
- A . copy the Console address and set the config map for the default namespace.
- B . create a new namespace in Kubernetes called admission-controller.
- C . enable Kubernetes auditing from the Defend > Access > Kubernetes page in the Console.
- D . copy the admission controller configuration from the Console and apply it to Kubernetes.
Which Prisma Cloud policy type detects port scanning activities in a customer environment?
- A . Port Scan
- B . Anomaly
- C . Config
- D . Network
Which Prisma Cloud policy type detects port scanning activities in a customer environment?
- A . Port Scan
- B . Anomaly
- C . Config
- D . Network