Practice Free NSK200 Exam Online Questions
You are creating an API token to allow a DevSecOps engineer to create and update a URL list using REST API v2.
In this scenario, which privilege(s) do you need to create in the API token?
- A . Provide read and write access for the "/events" endpoint.
- B . Provide read and write access for the "/urllist" endpoint.
- C . Provide only read access for the "/urllist" endpoint.
- D . Provide only write access for the "/urllist" endpoint.
B
Explanation:
To create an API token to allow a DevSecOps engineer to create and update a URL list using REST API v2, you need to provide read and write access for the “/urllist” endpoint. The “/urllist” endpoint is the API endpoint that allows you to manage URL lists in your Netskope tenant. You can use this endpoint to perform operations such as create, update, delete, or list URL lists3. To create an API token with this privilege, you need to go to Settings > Tools > REST API v2 > New Token, enter a token name and expiration time, add the “/urllist” endpoint, and select Read+Write as the privilege4. This will allow the DevSecOps engineer to use the API token in their requests to create and update URL lists. Therefore, option B is correct and the other options are incorrect.
Reference: REST API v2 Overview – Netskope Knowledge Portal, Manage URL Lists – Netskope Knowledge Portal
You are an administrator writing Netskope Real-time Protection policies and must determine proper policy ordering.
Which two statements are true in this scenario? (Choose two.)
- A . You must place DLP policies at the bottom.
- B . You do not need to create an "allow all" Web Access policy at the bottom.
- C . You must place Netskope private access malware policies in the middle.
- D . You must place high-risk block policies at the top.
BD
Explanation:
Placing high-risk block policies at the top ensures that critical blocks are enforced first, protecting against the most severe threats. Additionally, an "allow all" Web Access policy at the bottom is not necessary, as policy defaults can handle remaining traffic not explicitly addressed by other rules.
You want to provide malware protection for all cloud storage applications.
In this scenario, which action would accomplish this task?
- A . Create a real-time threat protection policy with a category of Cloud Storage.
- B . Apply a data protection profile.
- C . Apply a CTEP profile.
- D . Create an API threat protection policy with a category of Cloud Storage.
A
Explanation:
Creating a real-time threat protection policy specifically targeting the "Cloud Storage" category ensures that all supported cloud storage applications are covered by malware protection. This approach allows real-time scanning and response to malware threats within cloud storage environments.
Your company has Microsoft Azure ADFS set up as the Identity Provider (idP). You need to deploy the Netskope client to all company users on Windows laptops without user intervention.
In this scenario, which two deployment options would you use? (Choose two.)
- A . Deploy the Netskope client with SCCM.
- B . Deploy the Netskope client with Microsoft GPO.
- C . Deploy the Netskope client using IdP.
- D . Deploy the Netskope client using an email Invitation.
AB
Explanation:
To deploy the Netskope client to all company users on Windows laptops without user intervention, you can use either SCCM or GPO. These are two methods of packaging the application and pushing it silently to the user’s device using Microsoft tools4. These methods do not require the user to have local admin privileges or to initiate the installation themselves. They also allow enforcing the use of the client through company policy. The Netskope client can authenticate the user using Azure ADFS as the identity provider, as long as the UPN of the logged in user matches the directory5
The director of IT asks for confirmation If your organization’s Web traffic would be blocked when the Netskope client fails.
In this situation, what would confirm the fail close status?
- A . Perform a right-click on the Netskope client icon using your mouse.
- B . Review the nsdebuglog.log.
- C . View Application events.
- D . Review user settings.
B
Explanation:
The method that would confirm the fail close status is B. Review the nsdebuglog.log. The nsdebuglog.log is a log file that contains information about the Netskope client’s status, configuration, events, errors, etc. You can review the nsdebuglog.log file to confirm the fail close status by looking for a line that says “failCloseStatus”:“1”. This indicates that the fail close option is enabled for the Netskope client4. The fail close option is a feature that allows you to block all web traffic when the Netskope client fails or loses connection to the Netskope cloud5. Therefore, option B is correct and the other options are incorrect.
Reference: Troubleshooting Netskope Client – Netskope Knowledge Portal, Client Configuration – Netskope Knowledge Portal
Review the exhibit.
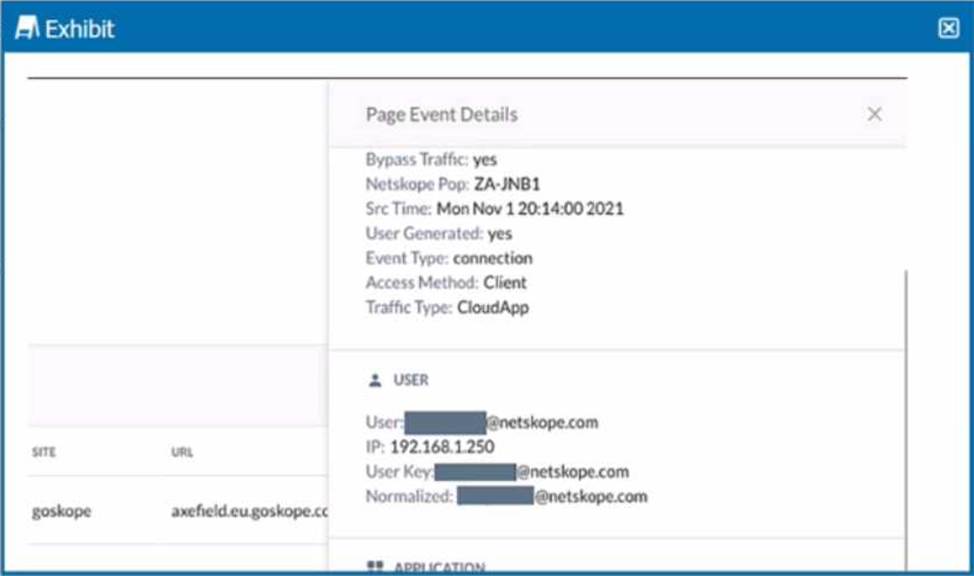
You are asked to restrict users from accessing YouTube content tagged as Sport. You created the required real-time policy; however, users can still access the content
Referring to the exhibit, what is the problem?
- A . The website is in a steering policy exception.
- B . The policy changes have not been applied.
- C . The YouTube content cannot be controlled.
- D . The traffic matched a Do Not Decrypt policy
D
Explanation:
The problem in this scenario is that the traffic matched a Do Not Decrypt policy. A Do Not Decrypt policy is a rule that specifies the traffic that you want to leave encrypted and not further analyzed by Netskope via the Real-time Protection policies1. In the exhibit, we can see that the traffic from the user to YouTube has a “Bypass Traffic” value of “yes” and a “Netskope” value of “yes”. This means that the traffic was steered to Netskope but not decrypted or inspected2. Therefore, the real-time policy that was created to restrict users from accessing YouTube content tagged as Sport did not apply, and users could still access the content. To solve this problem, you need to either remove or modify the Do Not Decrypt policy that matches the traffic to YouTube, or create an exception for the Sport category in the policy3. Therefore, option D is correct and the other options are incorrect.
Reference: Page Events – Netskope Knowledge Portal, Add a Policy for SSL Decryption – Netskope Knowledge Portal, YouTube Content Control – Netskope Knowledge Portal
You have created a specific Skope IT application events query and want to have the query automatically run and display the results every time you log into your tenant.
Which two statements are correct in this scenario? (Choose two.)
- A . Add the Watchlist widget from the library to your home page.
- B . Export a custom Skope IT watchlist to a report and then schedule it to run daily.
- C . Save a custom Skope IT watchlist, then manage filters and share with others.
- D . Add your Skope IT query to a custom watchlist.
CD
Explanation:
Adding a Skope IT query to a custom watchlist allows the query to be saved and easily accessed. Saving the watchlist and managing filters also lets you customize it further and share it with others in your organization if needed.
Review the exhibit.

While diagnosing an NPA connectivity issue, you notice an error message in the Netskope client logs.
Referring to the exhibit, what does this error represent?
- A . The Netskope client has been load-balanced to a different data center.
- B . The primary publisher is unavailable or cannot be reached.
- C . There Is an EDNS or LDNS resolution error.
- D . There Is an upstream device trying to intercept the NPA TLS connection.
D
Explanation:
The error message in the exhibit represents that there is an upstream device trying to intercept the NPA TLS connection. The error message is “ERROR SSL certificate verification failed: self signed certificate in certificate chain”. This means that the Netskope client is receiving a certificate that is not issued by Netskope, but by a device that is intercepting and decrypting the traffic between the client and the Netskope cloud. This can cause the client to fail to establish a secure connection to the NPA service and access the private applications4. To solve this problem, you need to either bypass or trust the upstream device that is performing SSL decryption, such as a firewall or proxy5. Therefore, option D is correct and the other options are incorrect.
Reference: Troubleshooting Netskope Client – Netskope Knowledge Portal, Netskope Client Troubleshooting Guide – The Netskope Community
