Practice Free NSK200 Exam Online Questions
You want to allow both the user identities and groups to be imported in the Netskope platform.
Which two methods would satisfy this requirement? (Choose two.)
- A . Use System for Cross-domain Identity Management (SCIM).
- B . Use Manual Entries.
- C . Use Directory Importer.
- D . Use Bulk Upload with a CSV file.
AD
Explanation:
To allow both the user identities and groups to be imported in the Netskope platform, you can use either the System for Cross-domain Identity Management (SCIM) method or the Bulk Upload with a CSV file method. Both of these methods allow for the import of user identities and groups from different identity providers (IdPs) that support SCIM or CSV formats. The SCIM method is recommended for large-scale deployments, as it automates the exchange of user identity information across apps for user provisioning. The CSV method is recommended for small-scale deployments, as it allows for manual upload of user details in a comma-separated values file. The other methods are not suitable for this requirement. The Manual Entries method does not allow for the import of groups, only user emails. The Directory Importer method does not import users and groups directly into the Netskope platform, but rather connects to an Active Directory or LDAP server and periodically fetches user and group information.
Reference: Provisioning Users for Netskope Client2, SCIM Integration3, Bulk Upload via CSV file
You are comparing the behavior of Netskope’s Real-time Protection policies to API Data Protection
policies.
In this Instance, which statement is correct?
- A . All real-time policies are enforced, regardless of sequential order, while API policies are analyzed sequentially from top to bottom and stop once a policy Is matched.
- B . Both real-time and API policies are analyzed sequentially from top to bottom and stop once a policy Is matched.
- C . All API policies are enforced, regardless of sequential order, while real-time policies are analyzed sequentially from top to bottom and stop once a policy Is matched.
- D . Both real-time and API policies are all enforced, regardless of sequential order.
C
Explanation:
Netskope’s Real-time Protection policies and API Data Protection policies have different ways of applying actions based on the policy order. Real-time Protection policies are analyzed sequentially from top to bottom and stop once a policy is matched. This means that only one policy action is applied per transaction. API Data Protection policies are all enforced, regardless of sequential order. This means that multiple policy actions can be applied per file or email. Therefore, the correct statement is that all API policies are enforced, regardless of sequential order, while real-time policies are analyzed sequentially from top to bottom and stop once a policy is matched.
Reference: Real-time Protection Policies1, API Data Protection Policies2
Your company wants to know if there has been any unusual user activity. In the UI, you go to Skope IT -> Alerts.
Which two types of alerts would you filter to find this information? (Choose two.)
- A . Alert type = uba
- B . Alert type = anomaly
- C . Alert type = malware
- D . Alert type = policy
AB
Explanation:
To identify unusual user activity, filter alerts by "uba" (User Behavior Analytics) and "anomaly." UBA and anomaly alerts highlight deviations from typical user behavior, which are indicators of unusual or potentially risky activities.
You are provisioning Netskope users from Okta with SCIM Provisioning, and users are not showing up in the tenant.
In this scenario, which two Netskope components should you verify first In Okta for accuracy? (Choose two.)
- A . IdP Entity ID
- B . OAuth token
- C . Netskope SAML certificate
- D . SCIM server URL
BD
Explanation:
To provision Netskope users from Okta with SCIM Provisioning, and users are not showing up in the tenant, the two Netskope components that you should verify first in Okta for accuracy are B. OAuth token and D. SCIM server URL. The OAuth token is a credential that allows Okta to authenticate with the Netskope SCIM server and perform user provisioning operations4. The SCIM server URL is the endpoint that Okta uses to communicate with the Netskope SCIM server and send user data5. Both of these components must be configured correctly in Okta for the SCIM Provisioning to work. You can find them in the Netskope UI under Settings > Tools > Directory Tools > SCIM Integration6. Therefore, options B and D are correct and the other options are incorrect.
Reference: SCIM-Based User Provisioning – Netskope Knowledge Portal, Netskope + Okta Use Case: Provisioning Users and Managing Groups Using SCIM – Netskope, Netskope Partner Okta – Netskope
Your customer is using a virtual desktop infrastructure (VDI) for their support engineers. Multiple users will be logging into the same device, and they want to detect activities for each user.
- A . Install Netskope client in default mode and enable DTLS.
- B . Install Netskope client and create a separate steering configuration for each user.
- C . Install Netskope client in peruserconfig mode.
- D . Install Netskope client and create a separate device configuration for each user.
C
Explanation:
Installing the Netskope client in "peruserconfig" mode allows for user-specific configurations on shared devices like those in a VDI environment. This mode enables Netskope to detect and report activities separately for each user, even if multiple users are logged into the same device.
Review the exhibit.
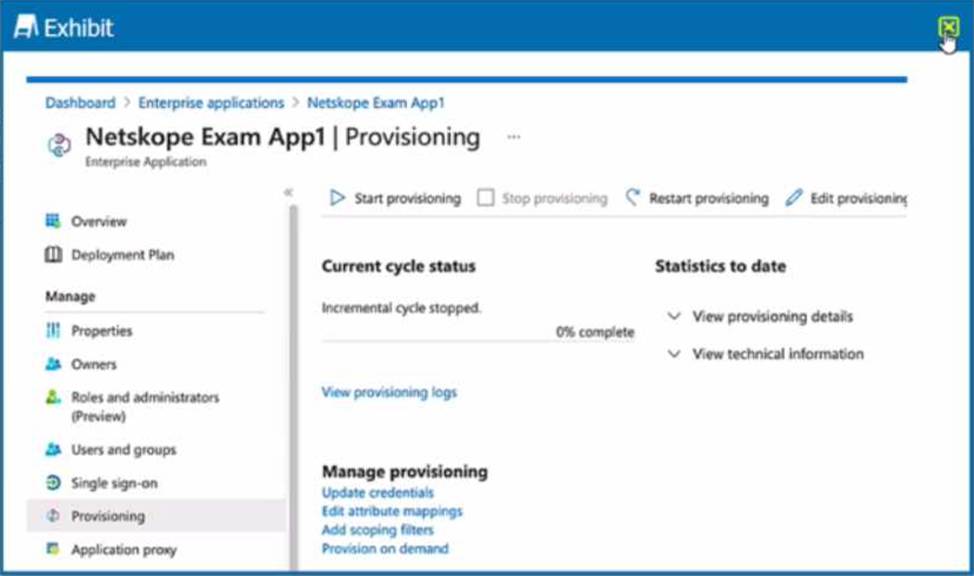
What is the purpose of the configuration page shown Ii the exhibit?
- A . to provision a Netskope client using SCCM
- B . to allow users to authenticate against the proxy
- C . to onboard Active Directory users to a Netskope tenant
- D . to enforce administrative role-based access
C
Explanation:
The configuration page shown in the exhibit is used to onboard Active Directory users to a Netskope tenant. This is done by configuring the Active Directory settings in the Netskope platform and then importing the users from Active Directory.
The configuration page allows you to specify the following parameters:
Directory Service: The type of directory service that you are using, such as Active Directory or LDAP.
Domain Name: The name of your Active Directory domain, such as example.com.
Domain Controller: The IP address or hostname of your Active Directory domain controller, such as dc1.example.com.
Username: The username of an account that has read access to your Active Directory, such as [email protected].
Password: The password of the account that has read access to your Active Directory.
Base DN: The base distinguished name of the container or organizational unit that contains the users and groups that you want to import, such as OU=Users,DC=example,DC=com.
User Filter: The LDAP filter that defines the criteria for selecting the users that you want to import, such as (objectClass=user).
Group Filter: The LDAP filter that defines the criteria for selecting the groups that you want to import, such as (objectClass=group).
After configuring these parameters, you can click on Test Connection to verify that the connection to your Active Directory is successful. Then you can click on Import Users to start importing the users and groups from your Active Directory to your Netskope tenant.
Reference: Onboarding Active Directory Users to a Netskope Tenant1
Review the exhibit.
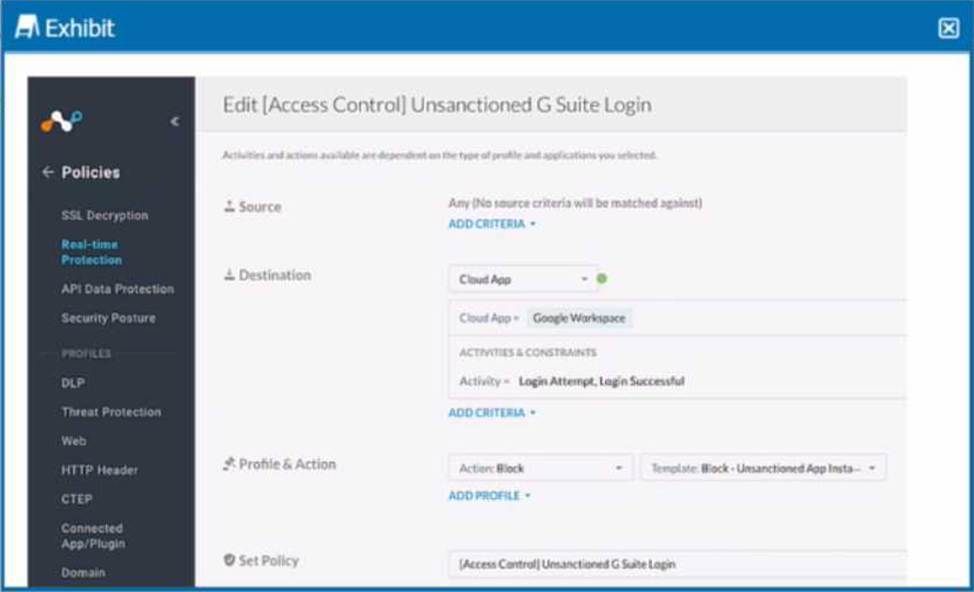
Your company uses Google as the corporate collaboration suite; however, corporate policy restricts the use of personal Google services. The exhibit provides a partially completed policy to ensure that users cannot log into their personal account.
What should be added to achieve the desired outcome in this scenario?
- A . Google Gmail app
- B . User Constraint
- C . DLP profile
- D . Device classification
B
Explanation:
In order to restrict users from logging into their personal Google accounts, the policy should include a user constraint. This will ensure that only users with corporate accounts can access the corporate collaboration suite. The user constraint can be added by selecting the “User” option in the “Source” field and then choosing the appropriate user group or identity provider. The other options are not relevant for this scenario.
Reference: [Creating a Policy to Block Personal Google Services], [Policy Creation], [User Constraint]
You want to secure Microsoft Exchange and Gmail SMTP traffic for DLP using Netskope.
Which statement is true about this scenario when using the Netskope client?
- A . Netskope can inspect outbound SMTP traffic for Microsoft Exchange and Gmail.
- B . Enable Cloud Firewall to Inspect Inbound SMTP traffic for Microsoft Exchange and Gmail.
- C . Netskope can inspect inbound and outbound SMTP traffic for Microsoft Exchange and Gmail.
- D . Enable REST API v2 to Inspect inbound SMTP traffic for Microsoft Exchange and Gmail.
A
Explanation:
Netskope can inspect outbound SMTP traffic for Microsoft Exchange and Gmail using the Netskope client. The Netskope client intercepts the SMTP traffic from the user’s device and forwards it to the Netskope cloud for DLP scanning. The Netskope client does not inspect inbound SMTP traffic, as this is handled by the cloud email service or the MTA. Therefore, option A is correct and the other options are incorrect.
Reference: Configure Netskope SMTP Proxy with Microsoft O365 Exchange, Configure Netskope SMTP Proxy with Gmail, SMTP DLP, Best Practices for Email Security with SMTP proxy
You have deployed Netskope Secure Web Gateway (SWG). Users are accessing new URLs that need to be allowed on a daily basis. As an SWG administrator, you are spending a lot of time updating Web policies. You want to automate this process without having to log into the Netskope tenant
Which solution would accomplish this task?
- A . You can use Cloud Log Shipper.
- B . You can minimize your work by sharing URLs with Netskope support.
- C . You can use Cloud Risk Exchange.
- D . You can use REST API to update the URL list.
D
Explanation:
To automate the process of updating Web policies without having to log into the Netskope tenant, you can use REST API to update the URL list. REST API is a feature that allows you to use an auth token to make authorized calls to the Netskope API and access resources via URI paths1. You can use REST API to update a URL list with new values by providing the name of an existing URL list and a comma-separated list of URLs or IP addresses2. This can help you automate or script the management of your URL lists and keep them up-to-date. Therefore, option D is correct and the other options are incorrect.
Reference: REST API v2 Overview – Netskope Knowledge Portal, Update a URL List – Netskope Knowledge Portal
Which statement describes how Netskope’s REST API, v1 and v2, handles authentication?
- A . Both REST API v1 and v2 require the use of tokens to make calls to the API
- B . Neither REST API v1 nor v2 require the use of tokens.
- C . REST API v2 requires the use of a token to make calls to the API. while API vl does not.
- D . REST API v1 requires the use of a token to make calls to the API. while API v2 does not.
A
Explanation:
The statement that describes how Netskope’s REST API, v1 and v2, handles authentication is A. Both REST API v1 and v2 require the use of tokens to make calls to the API. A token is a unique string that identifies the user or application that is making the API request. The token must be included in the HTTP header of every API call as an authorization parameter1. The token can be generated from the Netskope UI or from the Netskope Platform API2. The token can also be revoked or refreshed as needed3. Therefore, option A is correct and the other options are incorrect.
Reference: REST API v1 Overview – Netskope Knowledge Portal, Netskope Platform API Endpoints for REST API v1 – Netskope Knowledge Portal, REST API v2 Overview – Netskope Knowledge Portal
