Practice Free MS-102 Exam Online Questions
You have a new Microsoft 365 E5 tenant.
You need to enable an alert policy that will be triggered when an elevation of Microsoft Exchange Online administrative privileges is detected.
What should you do first?
- A . Enable auditing.
- B . Enable Microsoft 365 usage analytics.
- C . Create an Insider risk management policy.
- D . Create a communication compliance policy.
A
Explanation:
Microsoft Purview auditing solutions provide an integrated solution to help organizations effectively respond to security events, forensic investigations, internal investigations, and compliance obligations. Thousands of user and admin operations performed in dozens of Microsoft 365 services and solutions are captured, recorded, and retained in your organization’s unified audit log. Audit records for these events are searchable by security ops, IT admins, insider risk teams, and compliance and legal investigators in your organization. This capability provides visibility into the activities performed across your Microsoft 365 organization.
Note: Permissions alert policies
Example: Elevation of Exchange admin privilege
Generates an alert when someone is assigned administrative permissions in your Exchange Online organization. For example, when a user is added to the Organization Management role group in Exchange Online.
Reference:
https://learn.microsoft.com/en-us/microsoft-365/compliance/audit-solutions-overview
https://learn.microsoft.com/en-us/microsoft-365/compliance/alert-policies
HOTSPOT
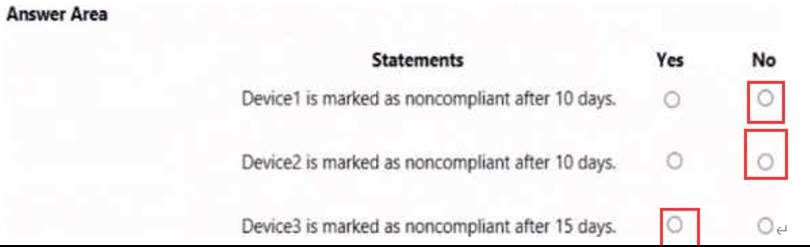
You have three devices enrolled in Microsoft Endpoint Manager as shown in the following table.

The device compliance policies in Endpoint Manager are configured as shown in the following table.

The device compliance policies have the assignments shown in the following table.

For each of the following statements, select Yes if the statement Is true. Otherwise, select No. NOTE: Each correct selection is worth one point.

You are reviewing alerts in the Microsoft 365 Defender portal.
How long are the alerts retained in the portal?
- A . 30 days
- B . 60 days
- C . 3 months
- D . 6 months
- E . 12 months
D
Explanation:
Data retention information for Microsoft Defender for Office 365
By default, data across different features is retained for a maximum of 30 days. However, for some of the features, you can specify the retention period based on policy. See the following table for the different retention periods for each feature.
Defender for Office 365 Plan 1
* Alert metadata details (Microsoft Defender for Office alerts) 90 days.
Note: By default, the alerts queue in the Microsoft 365 Defender portal displays the new and in progress alerts from the last 30 days. The most recent alert is at the top of the list so you can see it first.

Reference: https://learn.microsoft.com/en-us/microsoft-365/security/office-365-security/mdo-data-retention
Your company has multiple offices.
You have a Microsoft 365 E5 tenant that uses Microsoft Intune for device management. Each office has a local administrator.
You need to ensure that the local administrators can manage only the devices in their respective office.
What should you use?
- A . scope tags
- B . configuration profiles
- C . device categories
- D . conditional access policies
A
Explanation:
Reference: https://docs.microsoft.com/en-us/mem/intune/fundamentals/scope-tags
You have a Microsoft 365 tenant.
You plan to implement Endpoint Protection device configuration profiles.
Which platform can you manage by using the profile?
- A . Android
- B . CentOS Linux
- C . iOS
- D . Window 10
D
Explanation:
Reference: https://docs.microsoft.com/en-us/mem/intune/protect/endpoint-protection-configure
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it as a result these questions will not appear in the review screen.
Your network contains an Active Directory forest.
You deploy Microsoft 365.
You plan to implement directory synchronization.
You need to recommend a security solution for the synchronized identities.
The solution must meet the following requirements:
• Users must be able to authenticate successfully to Microsoft 365 services if Active Directory becomes unavailable.
• User passwords must be 10 characters or more.
Solution: Implement pass-through authentication and configure password protection in the Azure AD tenant.
Does this meet the goal?
- A . Yes
- B . No
Your network contains an Active Directory forest named Contoso. Local.
You have a Microsoft 365 subscription.
You plan to implement a directory synchronization solution that will use password hash
synchronization.
From the Microsoft 365 admin center, you successfully verify the contoso.com domain name.
You need to prepare the environment for the planned directory synchronization solution.
What should you do first?
- A . From Active Directory Domains and Trusts, add contoso.com as a UPN suffix.
- B . From the Microsoft 365 admin center verify the Contoso. Local domain name.
- C . From the public DNS zone of contoso.com, add a new mail exchanger (MX) record.
- D . From Active Directory Users and Computers, modify the UPN suffix for all users.
You have a Microsoft 365 subscription.
You plan to use Adoption Score and need to ensure that it can obtain device and software metrics.
What should you do?
- A . Enable Endpoint analytics.
- B . Run the Microsoft 365 network connectivity test on each device.
- C . Enable privileged access.
- D . Configure Support integration.
You have a hybrid Azure Active Directory (Azure AD) tenant and a Microsoft Endpoint Configuration Manager deployment.
You have the devices shown in the following table.

You plan to enable co-management.
You need to identify which devices support co-management without requiring the installation of additional software.
Which devices should you identify?
- A . Device1 only
- B . Device2 only
- C . Device3 only
- D . Device2 and Device3 only
- E . Device1, Device2, and Device3
HOTSPOT
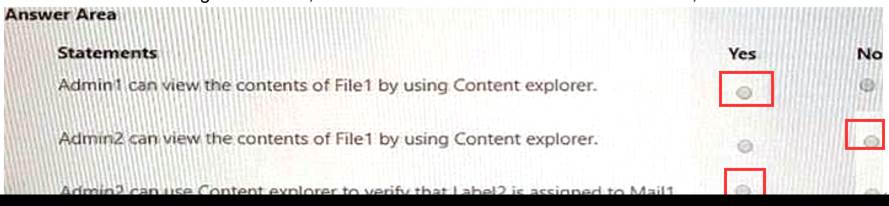
You have a Microsoft 365 E5 subscription that contains the users shown in the following table.

You have labels in Microsoft 365 as shown in the following table.

The content in Microsoft 365 is assigned labels as shown in the following table.

You have labels In Microsoft 365 as shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.