Practice Free MS-102 Exam Online Questions
You have a Microsoft 365 E5 subscription.
You onboard all devices to Microsoft Defender for Endpoint
You need to use Defender for Endpoint to block access to a malicious website at www.contoso.com.
Which two actions should you perform? Each correct answer presents part of the solution. NOTE: Each correct answer is worth one point.
- A . Create a web content filtering policy.
- B . Configure an enforcement scope.
- C . Enable Custom network indicators.
- D . Create an indicator.
- E . Enable automated investigation.
HOTSPOT
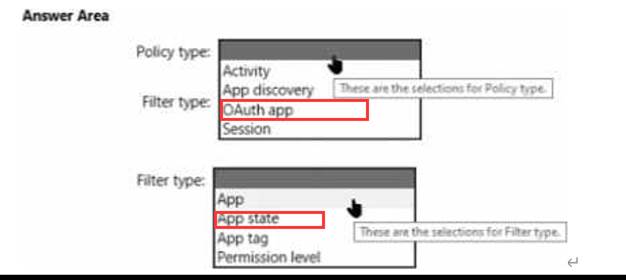
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps.
You need to create a policy that will generate an email alert when a banned app is detected requesting permission to access user information or data in the subscription.
What should you configure? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You have a Microsoft 365 tenant.
You plan to implement device configuration profiles in Microsoft Intune.
Which platform can you manage by using the profiles?
- A . Ubuntu Linux
- B . macOS
- C . Android Enterprise
- D . Windows 8.1
HOTSPOT
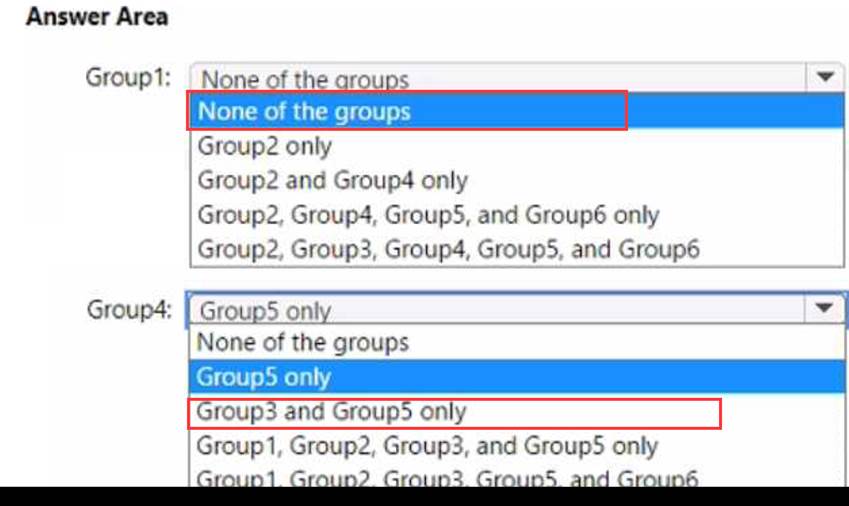
You have a Microsoft 365 E5 subscription that contains the groups shown in the following table.

Which groups can be members of Group1 and Group4? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You have a Microsoft 365 subscription that contains the users shown in the following table.

You need to configure group-based licensing to meet the following requirements:
To all users, deploy an Office 365 E3 license without the Power Automate license option.
To all users, deploy an Enterprise Mobility + Security E5 license.
To the users in the research department only, deploy a Power BI Pro license.
To the users in the marketing department only, deploy a Visio Plan 2 license.
What is the minimum number of deployment groups required?
- A . 1
- B . 2
- C . 3
- D . 4
- E . 5
C
Explanation:
One for all users, one for the research department, and one for the marketing department.
Note: What are Deployment Groups?
With Deployment Groups, you can orchestrate deployments across multiple servers and perform rolling updates, while ensuring high availability of your application throughout. You can also deploy to servers on-premises or virtual machines on Azure or any cloud, plus have end-to-end traceability of deployed artifact versions down to the server level.
Reference: https://devblogs.microsoft.com/devops/deployment-groups-is-now-generally-available-sharing-of-targets-and-more
Which report should the New York office auditors view?
- A . DLP policy matches
- B . DLP false positives and overrides
- C . DLP incidents
- D . Top Senders and Recipients
C
Explanation:
Reference: https://docs.microsoft.com/en-us/office365/securitycompliance/data-loss-prevention-policies
This report also shows policy matches over time, like the policy matches report. However, the policy matches report shows matches at a rule level; for example, if an email matched three different rules, the policy matches report shows three different line items. By contrast, the incidents report shows matches at an item level; for example, if an email matched three different rules, the incidents report shows a single line item for that piece of content. Because the report counts are aggregated differently, the policy matches report is better for identifying matches with specific rules and fine tuning DLP policies. The incidents report is better for identifying specific pieces of content that are problematic for your DLP policies.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an on-premises Active Directory domain named contoso.com.
The domain contains the users shown in the following table.

The domain syncs to an Azure AD tenant named contoso.com as shown in the exhibit. (Click the Exhibit tab.)

User2 fails to authenticate to Azure AD when signing in as [email protected].
You need to ensure that User2 can access the resources in Azure AD.
Solution: From the Microsoft Entra admin center, you assign User2 the Security Reader role. You instruct User2 to sign in as [email protected].
Does this meet the goal?
- A . Yes
- B . No
B
Explanation:
This is not a permissions issue so you do not need to assign the Security Reader role.
The on-premises Active Directory domain is named contoso.com. User2 could sign on as [email protected] but you would first need to change the UPN of User2 to [email protected].
You have a Microsoft 365 tenant that contains 500 Windows 10 devices and a Microsoft Endpoint Manager device compliance policy.
You need to ensure that only devices marked as compliant can access Microsoft Office 365 apps.
Which policy type should you configure?
- A . conditional access
- B . account protection
- C . attack surface reduction (ASR)
- D . Endpoint detection and response
A
Explanation:
Reference: https://docs.microsoft.com/en-us/mem/intune/protect/device-compliance-get-started
You have a Microsoft 365 E5 tenant that contains 500 Windows 10 devices. The devices are enrolled in Microsoft intune.
You plan to use Endpoint analytics to identify hardware issues.
You need to enable Window health monitoring on the devices to support Endpoint analytics.
What should you do?
- A . Configure the Endpoint analytics baseline regression threshold.
- B . Create a configuration profile.
- C . Create a Windows 10 Security Baseline profile
- D . Create a compliance policy.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps.
You need to be notified when a single user downloads more than 50 files during any 60-second period.
What should you configure?
- A . a session policy
- B . a file policy
- C . an activity policy
- D . an anomaly detection policy
