Practice Free MS-102 Exam Online Questions
HOTSPOT
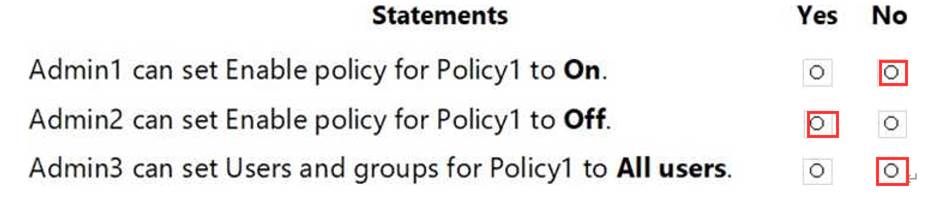
You have a Microsoft 365 E5 subscription linked to an Azure Active Directory (Azure AD) tenant.
The tenant contains a group named Group1 and the users shown in the following table:

The tenant has a conditional access policy that has the following configurations:
Name: Policy1
Assignments:
– Users and groups: Group1
– Cloud aps or actions: All cloud apps Access controls:
Grant, require multi-factor authentication Enable policy: Report-only
You set Enabled Security defaults to Yes for the tenant.
For each of the following settings select Yes, if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.

You have a Microsoft 365 E5 subscription.
You need to recommend a solution for monitoring and reporting application access.
The solution must meet the following requirements:
• Support KQL for querying data.
• Retain report data for at least one year.
What should you include in the recommendation?
- A . a security report in Microsoft 365 Defender
- B . End point analytics
- C . Microsoft 365 usage analytics
- D . Azure Monitor workbooks
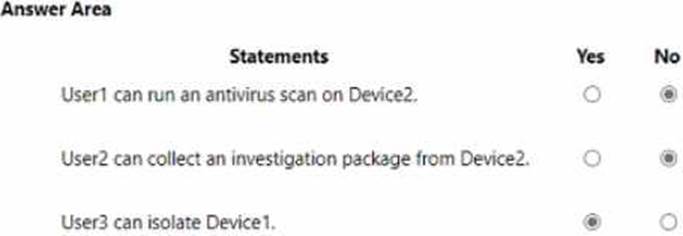
HOTSPOT
You have an Azure AD tenant that contains the users shown in the following table.

Your company uses Microsoft Defender for Endpoint. Microsoft Defender for Endpoint contains the roles shown in the following table.

Microsoft Defender for Endpoint contains the device groups shown in the following table.

For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE; Each correct selection is worth one point.

HOTSPOT
Your company uses a legacy on-premises LDAP directory that contains 100 users.
The company purchases a Microsoft 365 subscription.
You need to import the 100 users into Microsoft 365 by using the Microsoft 365 admin center.
Which type of file should you use and which properties are required? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

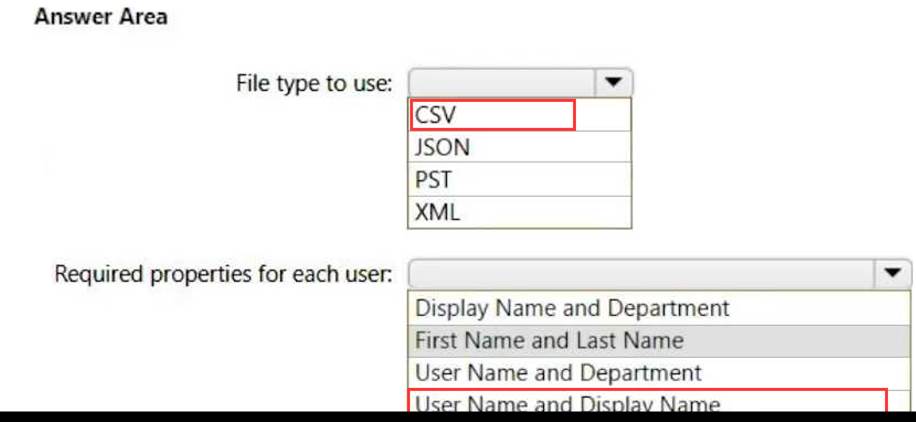
Explanation:
Box 1: CSV
Add multiple users in the Microsoft 365 admin center
Sign in to Microsoft 365 with your work or school account.
In the admin center, choose Users > Active users.
Select Add multiple users.
On the Import multiple users panel, you can optionally download a sample CSV file with or without sample data filled in.
Etc.
Note: More information about how to add users to Microsoft 365 Not sure what CSV format is?
A CSV file is a file with comma separated values. You can create or edit a file like this with any text editor or spreadsheet program, such as Excel.
Box 2: User Name and Display Name
What if I don’t have all the information required for each user? The user name and display name are required, and you cannot add a new user without this information. If you don’t have some of the other information, such as the fax, you can use a space plus a comma to indicate that the field should remain blank.
Reference: https://learn.microsoft.com/en-us/microsoft-365/enterprise/add-several-users-at-the-same-time
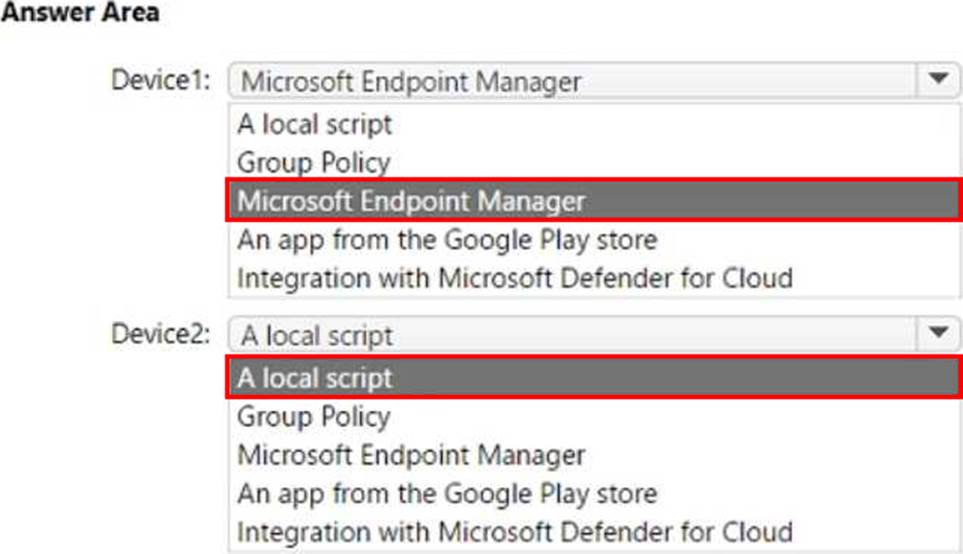
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Intune and contains the devices shown in the following table.

You need to onboard Device1 and Device2 to Microsoft Defender for Endpoint.
What should you use to onboard each device? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

HOTSPOT
You have a Microsoft 365 subscription that contains a Microsoft SharePoint Online site named Site1.
Site1 has he files in the following table.

The Site1 users are assigned the roles shown in the following table.

You create a data less prevention (DLP) policy names Policy1 as shown in the following exhibit.

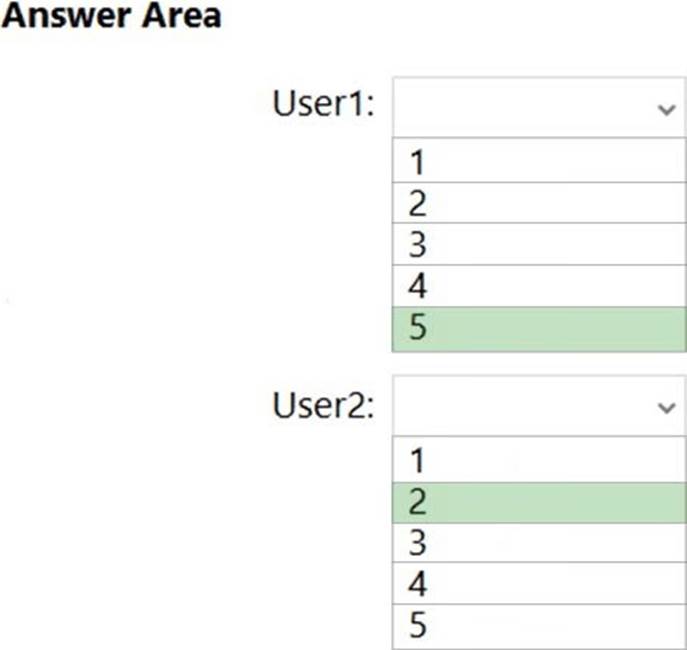
How many files will be visible to user1 and User2 after Policy’ is applied to answer, selected select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

You have a Microsoft 365 E5 tenant.
You plan to deploy a monitoring solution that meets the following requirements:
Captures Microsoft Teams channel messages that contain threatening or violent language.
Alerts a reviewer when a threatening or violent message is identified.
What should you include in the solution?
- A . Data Subject Requests (DSRs)
- B . Insider risk management policies
- C . Communication compliance policies
- D . Audit log retention policies
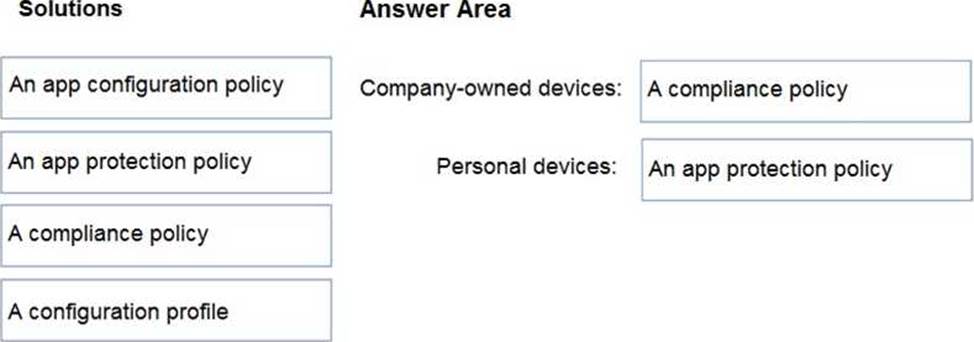
DRAG DROP
Your company has a Microsoft 365 E5 tenant.
Users access resources in the tenant by using both personal and company-owned Android devices.
Company policies requires that the devices have a threat level of medium or lower to access Microsoft Exchange Online mailboxes.
You need to recommend a solution to identify the threat level of the devices and to control access of the devices to the resources.
What should you include in the solution for each device type? To answer, drag the appropriate components to the correct devices. Each component may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.

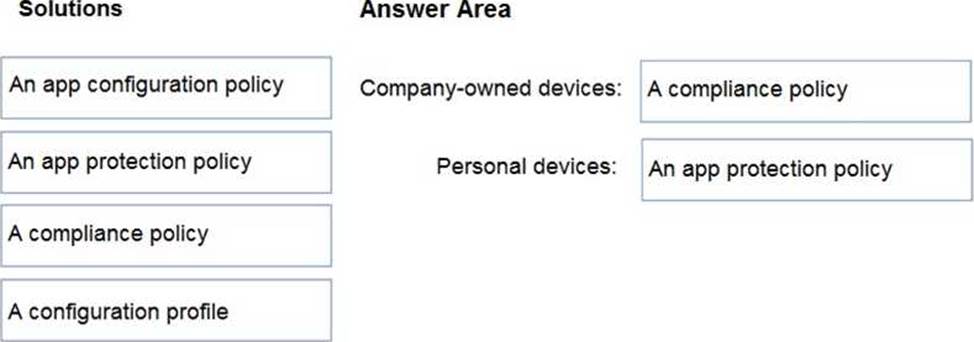
DRAG DROP
Your company has a Microsoft 365 E5 tenant.
Users access resources in the tenant by using both personal and company-owned Android devices.
Company policies requires that the devices have a threat level of medium or lower to access Microsoft Exchange Online mailboxes.
You need to recommend a solution to identify the threat level of the devices and to control access of the devices to the resources.
What should you include in the solution for each device type? To answer, drag the appropriate components to the correct devices. Each component may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.

You have a Microsoft Azure Active Directory (Azure AD) tenant named Contoso.com.
You create a Microsoft Defender for identity instance Contoso.
The tenant contains the users shown in the following table.

You need to modify the configuration of the Defender for identify sensors.
Solutions: You instruct User4 to modify the Defender for identity sensor configuration.
Does this meet the goal?
- A . Yes
- B . No
