Practice Free MD-102 Exam Online Questions
HOTSPOT
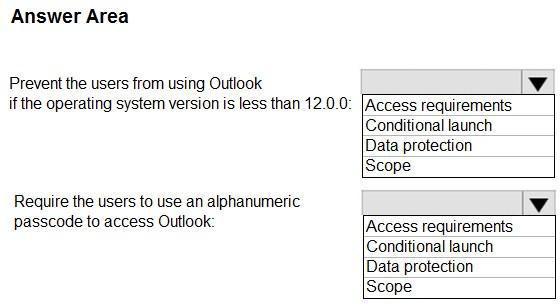
You have a Microsoft 365 subscription.
Users have iOS devices that are not enrolled in Microsoft Intune.
You create an app protection policy for the Microsoft Outlook app as shown in the exhibit. (Click the Exhibit tab.)
You need to configure the policy to meet the following requirements:
Prevent the users from using the Outlook app if the operating system version is less than 12.0.0.
Require the users to use an alphanumeric passcode to access the Outlook app.
What should you configure in an app protection policy for each requirement? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
Explanation:
Box 1: Conditional launch
Configure conditional launch settings to set sign-in security requirements for your access protection policy.
By default, several settings are provided with pre-configured values and actions. You can delete some of these, like the Min OS version. You can also select additional settings from the Select one dropdown.
Note: There are three categories of policy settings: Data relocation, Access requirements, and Conditional launch.
Box 2. Access requirements
Access requirements include:
PIN for access: Select Require to require a PIN to use this app. The user is prompted to set up this PIN the first time they run the app in a work or school context. The PIN is applied when working either online or offline.
You can configure the PIN strength using the settings available under the PIN for access section.
Reference: https://docs.microsoft.com/en-us/intune/app-protection-policy-settings-ios
You have a Microsoft 365 E5 subscription.
You need to configure the automated investigation and response (AIR) remediation level for a device named Device1 to require approval for all folders.
What should you create?
E. a security group
F. a device group
G. an administrative unit
H. an action group
Explanation:
Configure automated investigation and remediation capabilities in Microsoft Defender for Endpoint
If you’re using Defender for Endpoint, you can specify an automation level so that when a threat is detected on a device, the entity can be remediated automatically or only upon approval by your security team. You
can configure automated investigation and remediation with device groups.
Reference: https://learn.microsoft.com/en-us/defender-endpoint/configure-automated-investigations-remediation
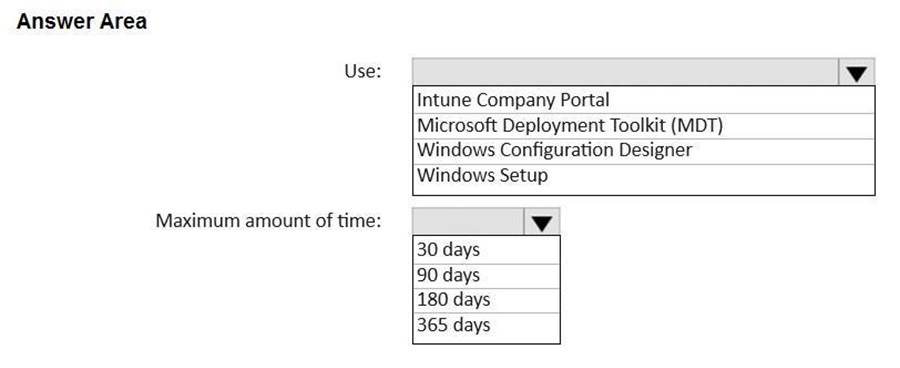
HOTSPOT
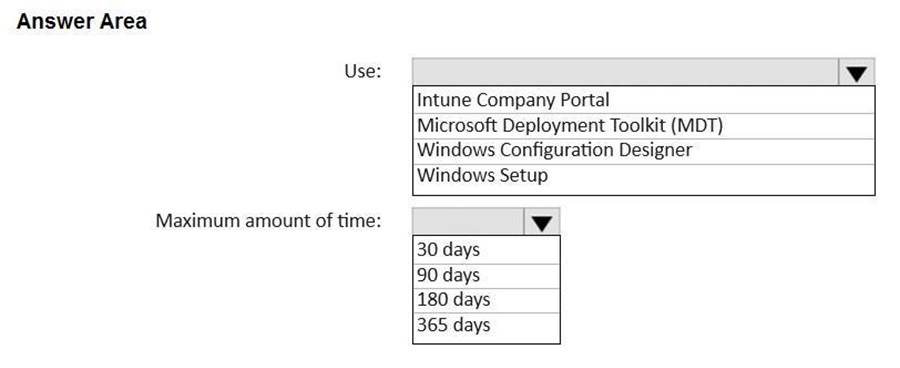
You have a Microsoft 365 E5 subscription and use Microsoft Intune.
You purchase 50 Windows devices.
You configure automatic enrollment to Intune for Microsoft Entra joined devices.
You need to use a provisioning package to join the devices to Microsoft Entra.
What should you use to create the provisioning package, and what is the maximum amount of time you can use the package for bulk enrollment? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
Explanation:
Box 1: Windows Configuration Designer
Use
Intune service, Bulk enrollment for Windows devices
Join new Windows devices to Microsoft Entra ID and Intune. To bulk enroll devices for your Microsoft Entra tenant, you create a provisioning package with the Windows Configuration Designer (WCD) app. Applying the provisioning package to corporate-owned devices joins the devices to your Microsoft Entra tenant and enrolls them for Intune management. Once the package is applied, it’s ready for your Microsoft Entra users to sign in.
Box 2: 180 days
Maximum amount of time
Select Enroll in Azure AD, enter a Bulk Token Expiry date, and then select Get Bulk Token. The token validity period is 180 days.
Reference: https://learn.microsoft.com/en-us/mem/intune/enrollment/windows-bulk-enroll
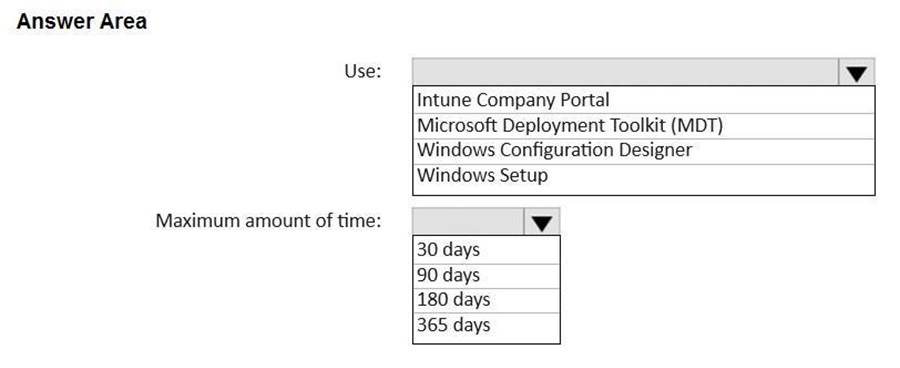
HOTSPOT
You have a Microsoft 365 E5 subscription and use Microsoft Intune.
You purchase 50 Windows devices.
You configure automatic enrollment to Intune for Microsoft Entra joined devices.
You need to use a provisioning package to join the devices to Microsoft Entra.
What should you use to create the provisioning package, and what is the maximum amount of time you can use the package for bulk enrollment? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
Explanation:
Box 1: Windows Configuration Designer
Use
Intune service, Bulk enrollment for Windows devices
Join new Windows devices to Microsoft Entra ID and Intune. To bulk enroll devices for your Microsoft Entra tenant, you create a provisioning package with the Windows Configuration Designer (WCD) app. Applying the provisioning package to corporate-owned devices joins the devices to your Microsoft Entra tenant and enrolls them for Intune management. Once the package is applied, it’s ready for your Microsoft Entra users to sign in.
Box 2: 180 days
Maximum amount of time
Select Enroll in Azure AD, enter a Bulk Token Expiry date, and then select Get Bulk Token. The token validity period is 180 days.
Reference: https://learn.microsoft.com/en-us/mem/intune/enrollment/windows-bulk-enroll
HOTSPOT
You have a Microsoft 365 E5 subscription and use Microsoft Intune.
You purchase 50 Windows devices.
You configure automatic enrollment to Intune for Microsoft Entra joined devices.
You need to use a provisioning package to join the devices to Microsoft Entra.
What should you use to create the provisioning package, and what is the maximum amount of time you can use the package for bulk enrollment? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
Explanation:
Box 1: Windows Configuration Designer
Use
Intune service, Bulk enrollment for Windows devices
Join new Windows devices to Microsoft Entra ID and Intune. To bulk enroll devices for your Microsoft Entra tenant, you create a provisioning package with the Windows Configuration Designer (WCD) app. Applying the provisioning package to corporate-owned devices joins the devices to your Microsoft Entra tenant and enrolls them for Intune management. Once the package is applied, it’s ready for your Microsoft Entra users to sign in.
Box 2: 180 days
Maximum amount of time
Select Enroll in Azure AD, enter a Bulk Token Expiry date, and then select Get Bulk Token. The token validity period is 180 days.
Reference: https://learn.microsoft.com/en-us/mem/intune/enrollment/windows-bulk-enroll
You have a Microsoft 365 E5 subscription that contains 100 Windows 10 devices enrolled in Microsoft Intune.
You plan to use Endpoint analytics.
You need to create baseline metrics.
What should you do first?
E. Modify the Baseline regression threshold.
F. Onboard 10 devices to Endpoint analytics.
G. Create a Log Analytics workspace.
H. Create an Azure Monitor workbook.
Explanation:
Onboarding from the Endpoint analytics portal is required for Intune managed devices.
Reference: https://docs.microsoft.com/en-us/mem/analytics/enroll-intune
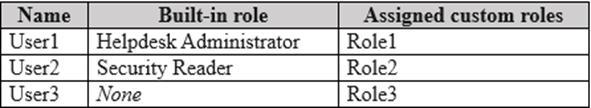
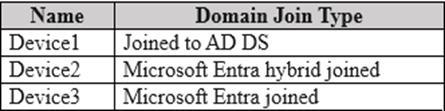
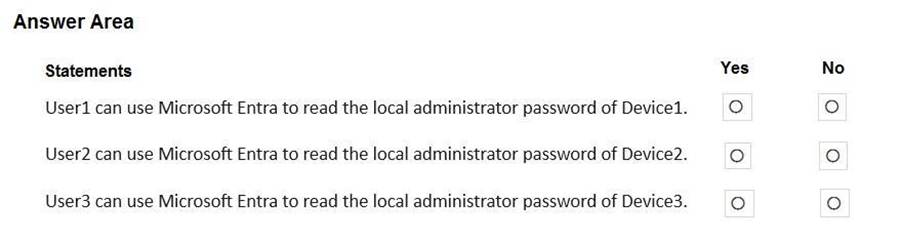
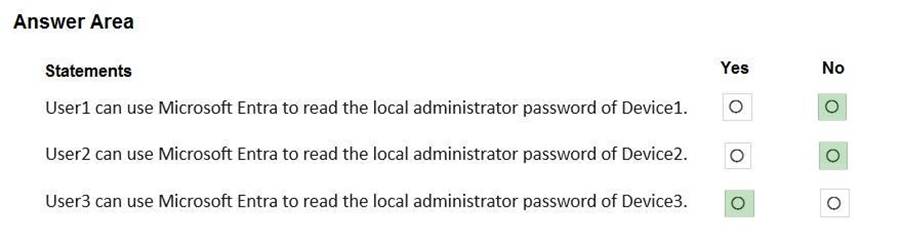
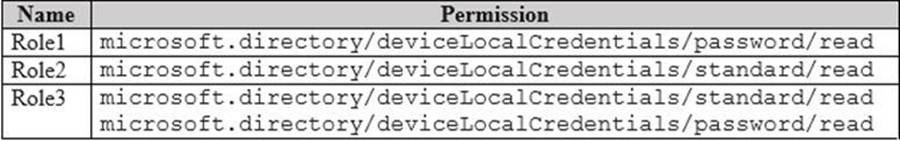
HOTSPOT
Your network contains an on-premises Active Directory Domain Services (AD DS) domain.
You have a Microsoft 365 E5 subscription that includes Microsoft Intune and syncs with the AD DS domain.
Windows Local Administrator Password Solution (Windows LAPS) is enabled in Microsoft Entra ID.
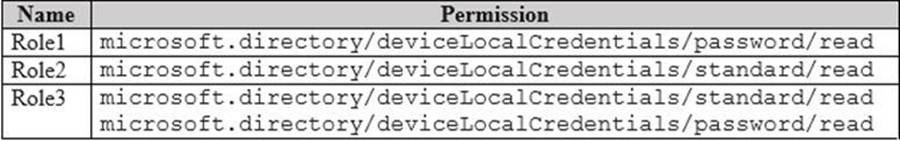
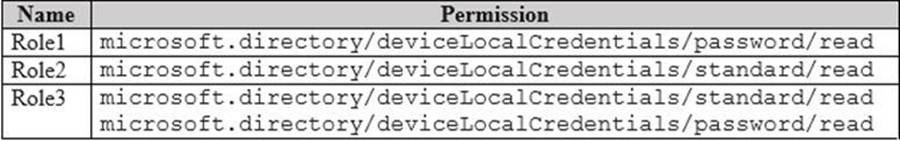
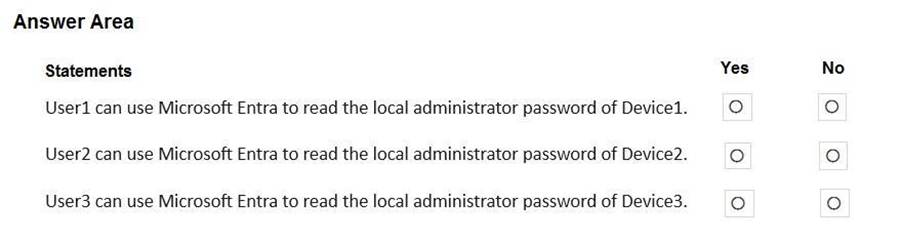
The subscription has the custom roles shown in the following table.
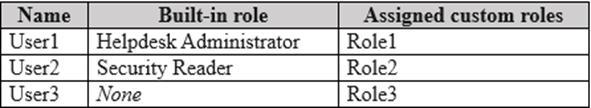
Microsoft Entra contains the users shown in the following table.
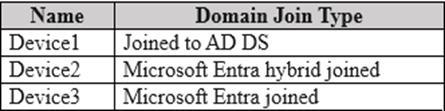
You have the devices shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Hot Area:
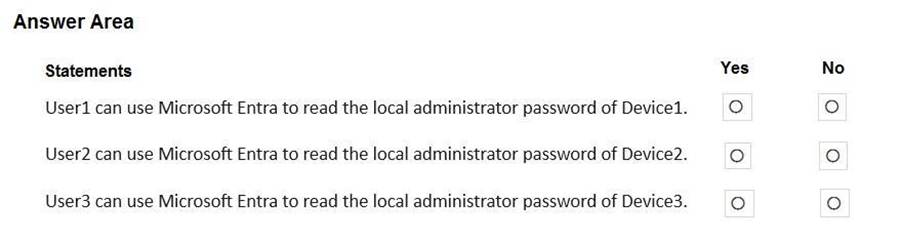
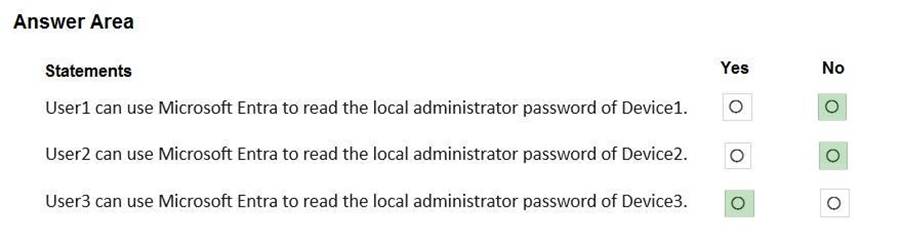
Explanation:
Box 1: No
No – User1 can use Microsoft Entra to read the local administrator password of Device1.
Device1 is joined to AD DS, but that does not support LAPS.
Box 2: No
No – User2 can use Microsoft Entra to read the local administrator password of Device2.
User2 is Security Reader.
User2 is assigned the custom role Role2
Role2 has the permission microsoft.directory/deviceLocalCredentials/standard/read, but this meet the LAPS requirement.
Box 3: Yes
Yes – User3 can use Microsoft Entra to read the local administrator password of Device3.
User3 is assigned the custom role Role3
Role2 has the permission microsoft.directory/deviceLocalCredentials/password/read, which meet the LAPS requirement.
Device3 is Microsoft Entra Joined, which also meets the LAPS requirement.
Note: Windows Local Administrator Password Solution in Microsoft Entra ID Join types
LAPS is supported on Microsoft Entra joined or Microsoft Entra hybrid joined devices only. Microsoft Entra registered devices aren’t supported.
Required roles or permission
Other than the built-in Microsoft Entra roles like Cloud Device Administrator and Intune Administrator that are granted device.LocalCredentials.Read.All, you can use Microsoft Entra custom roles or administrative units to authorize local administrator password recovery. For example:
Custom roles must be assigned the microsoft.directory/deviceLocalCredentials/password/read permission to authorize local administrator password recovery. You can create a custom role and grant permissions using the Microsoft Entra admin center, Microsoft Graph API or PowerShell. Once you create a custom role, you can assign it to users.
Reference: https://learn.microsoft.com/en-us/entra/identity/devices/howto-manage-local-admin-passwords
HOTSPOT
Your network contains an on-premises Active Directory Domain Services (AD DS) domain.
You have a Microsoft 365 E5 subscription that includes Microsoft Intune and syncs with the AD DS domain.
Windows Local Administrator Password Solution (Windows LAPS) is enabled in Microsoft Entra ID.
The subscription has the custom roles shown in the following table.
Microsoft Entra contains the users shown in the following table.
You have the devices shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Hot Area:
Explanation:
Box 1: No
No – User1 can use Microsoft Entra to read the local administrator password of Device1.
Device1 is joined to AD DS, but that does not support LAPS.
Box 2: No
No – User2 can use Microsoft Entra to read the local administrator password of Device2.
User2 is Security Reader.
User2 is assigned the custom role Role2
Role2 has the permission microsoft.directory/deviceLocalCredentials/standard/read, but this meet the LAPS requirement.
Box 3: Yes
Yes – User3 can use Microsoft Entra to read the local administrator password of Device3.
User3 is assigned the custom role Role3
Role2 has the permission microsoft.directory/deviceLocalCredentials/password/read, which meet the LAPS requirement.
Device3 is Microsoft Entra Joined, which also meets the LAPS requirement.
Note: Windows Local Administrator Password Solution in Microsoft Entra ID Join types
LAPS is supported on Microsoft Entra joined or Microsoft Entra hybrid joined devices only. Microsoft Entra registered devices aren’t supported.
Required roles or permission
Other than the built-in Microsoft Entra roles like Cloud Device Administrator and Intune Administrator that are granted device.LocalCredentials.Read.All, you can use Microsoft Entra custom roles or administrative units to authorize local administrator password recovery. For example:
Custom roles must be assigned the microsoft.directory/deviceLocalCredentials/password/read permission to authorize local administrator password recovery. You can create a custom role and grant permissions using the Microsoft Entra admin center, Microsoft Graph API or PowerShell. Once you create a custom role, you can assign it to users.
Reference: https://learn.microsoft.com/en-us/entra/identity/devices/howto-manage-local-admin-passwords
HOTSPOT
Your network contains an on-premises Active Directory Domain Services (AD DS) domain.
You have a Microsoft 365 E5 subscription that includes Microsoft Intune and syncs with the AD DS domain.
Windows Local Administrator Password Solution (Windows LAPS) is enabled in Microsoft Entra ID.
The subscription has the custom roles shown in the following table.
Microsoft Entra contains the users shown in the following table.
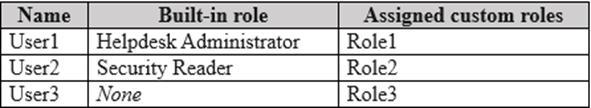
You have the devices shown in the following table.
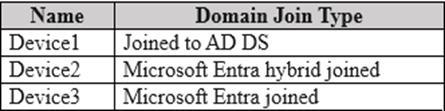
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Hot Area:
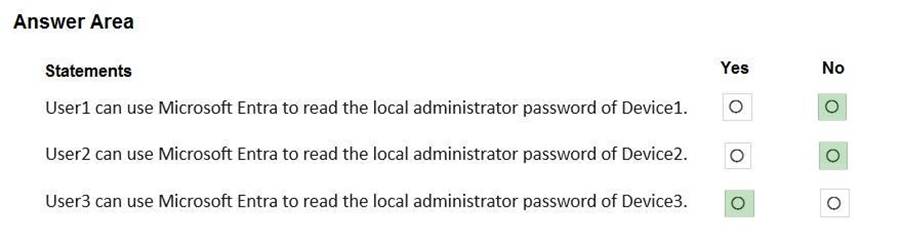
Explanation:
Box 1: No
No – User1 can use Microsoft Entra to read the local administrator password of Device1.
Device1 is joined to AD DS, but that does not support LAPS.
Box 2: No
No – User2 can use Microsoft Entra to read the local administrator password of Device2.
User2 is Security Reader.
User2 is assigned the custom role Role2
Role2 has the permission microsoft.directory/deviceLocalCredentials/standard/read, but this meet the LAPS requirement.
Box 3: Yes
Yes – User3 can use Microsoft Entra to read the local administrator password of Device3.
User3 is assigned the custom role Role3
Role2 has the permission microsoft.directory/deviceLocalCredentials/password/read, which meet the LAPS requirement.
Device3 is Microsoft Entra Joined, which also meets the LAPS requirement.
Note: Windows Local Administrator Password Solution in Microsoft Entra ID Join types
LAPS is supported on Microsoft Entra joined or Microsoft Entra hybrid joined devices only. Microsoft Entra registered devices aren’t supported.
Required roles or permission
Other than the built-in Microsoft Entra roles like Cloud Device Administrator and Intune Administrator that are granted device.LocalCredentials.Read.All, you can use Microsoft Entra custom roles or administrative units to authorize local administrator password recovery. For example:
Custom roles must be assigned the microsoft.directory/deviceLocalCredentials/password/read permission to authorize local administrator password recovery. You can create a custom role and grant permissions using the Microsoft Entra admin center, Microsoft Graph API or PowerShell. Once you create a custom role, you can assign it to users.
Reference: https://learn.microsoft.com/en-us/entra/identity/devices/howto-manage-local-admin-passwords
HOTSPOT
You have a Microsoft 365 subscription that uses Microsoft Intune Suite.
You use Microsoft Intune to manage devices.
You plan to create Windows 11 device builds for the marketing and research departments. The solution must meet the requirements:
Marketing department devices must support Windows Update for Business.
![]()
Research department devices must have support for feature update versions for up to 36 months from release.
![]()
What is the minimum Windows 11 edition required for each department? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
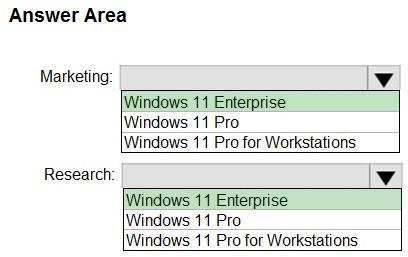
Explanation:
Box 1: Windows 11 Enterprise
Marketing department devices must support Windows Update for Business.
Licensing
Windows Update for Business deployment service requires users of the devices to have one of the following licenses:
Windows 10/11 Enterprise E3 or E5 (included in Microsoft 365 F3, E3, or E5) Windows 10/11 Education A3 or A5 (included in Microsoft 365 A3 or A5) Windows Virtual Desktop Access E3 or E5 Microsoft 365 Business Premium
Box 2: Windows 11 Enterprise
Research department devices must have support for feature update versions for up to 36 months from release.
Feature updates for Windows 10 and later policy in Intune
In addition to a license for Intune, your organization must have one of the following subscriptions that include a license for Windows Update for Business deployment service:
Windows 10/11 Enterprise E3 or E5 (included in Microsoft 365 F3, E3, or E5)
Windows 10/11 Education A3 or A5 (included in Microsoft 365 A3 or A5) Windows Virtual Desktop Access E3 or E5 Microsoft 365 Business Premium
Reference: https://learn.microsoft.com/en-us/windows/deployment/update/deployment-service-prerequisites
https://learn.microsoft.com/en-us/mem/intune/protect/windows-10-feature-updates
