Practice Free JN0-636 Exam Online Questions
In an effort to reduce client-server latency transparent mode was enabled an SRX series device.
Which two types of traffic will be permitted in this scenario? (Choose Two)
- A . ARP
- B . Layer 2 non-IP multicast
- C . BGP
- D . IPsec
AB
Explanation:
To answer this question, you need to know what transparent mode is and what types of traffic it permits. Transparent mode is a mode of operation for SRX Series devices that provides Layer 2 bridging capabilities with full security services. In transparent mode, the SRX Series device acts as a bridge between two network segments and inspects the packets without modifying the source or destination information in the IP packet header. The SRX Series device does not have an IP address in transparent mode, except for the management interface1.
Therefore, the types of traffic that will be permitted in transparent mode are:
A) ARP (Address Resolution Protocol) traffic. ARP is a protocol that maps IP addresses to MAC addresses. ARP traffic is a type of Layer 2 traffic that does not require an IP address on the SRX Series device. ARP traffic is permitted in transparent mode to allow the SRX Series device to learn the MAC addresses of the hosts on the bridged network segments2.
B) Layer 2 non-IP multicast traffic. Layer 2 non-IP multicast traffic is a type of traffic that uses MAC addresses to send data to multiple destinations. Layer 2 non-IP multicast traffic does not require an IP address on the SRX Series device. Layer 2 non-IP multicast traffic is permitted in transparent mode to allow the SRX Series device to forward data to the appropriate destinations on the bridged network segments3.
The other options are incorrect because:
C) BGP (Border Gateway Protocol) traffic. BGP is a protocol that exchanges routing information between autonomous systems. BGP traffic is a type of Layer 3 traffic that requires an IP address on the SRX Series device. BGP traffic is not permitted in transparent mode, because the SRX Series device does not have an IP address in transparent mode, except for the management interface1.
D) IPsec (Internet Protocol Security) traffic. IPsec is a protocol that provides security and encryption for IP packets. IPsec traffic is a type of Layer 3 traffic that requires an IP address on the SRX Series device. IPsec traffic is not permitted in transparent mode, because the SRX Series device does not have an IP address in transparent mode, except for the management interface1.
Reference: Transparent Mode Overview
ARP Support in Transparent Mode
Layer 2 Non-IP Multicast Traffic Support in Transparent Mode
You configured a chassis cluster for high availability on an SRX Series device and enrolled this HA cluster with the Juniper ATP Cloud.
Which two statements are correct in this scenario? (Choose two.)
- A . You must use different license keys on both cluster nodes.
- B . When enrolling your devices, you only need to enroll one node.
- C . You must set up your HA cluster after enrolling your devices with Juniper ATP Cloud
- D . You must use the same license key on both cluster nodes.
Exhibit
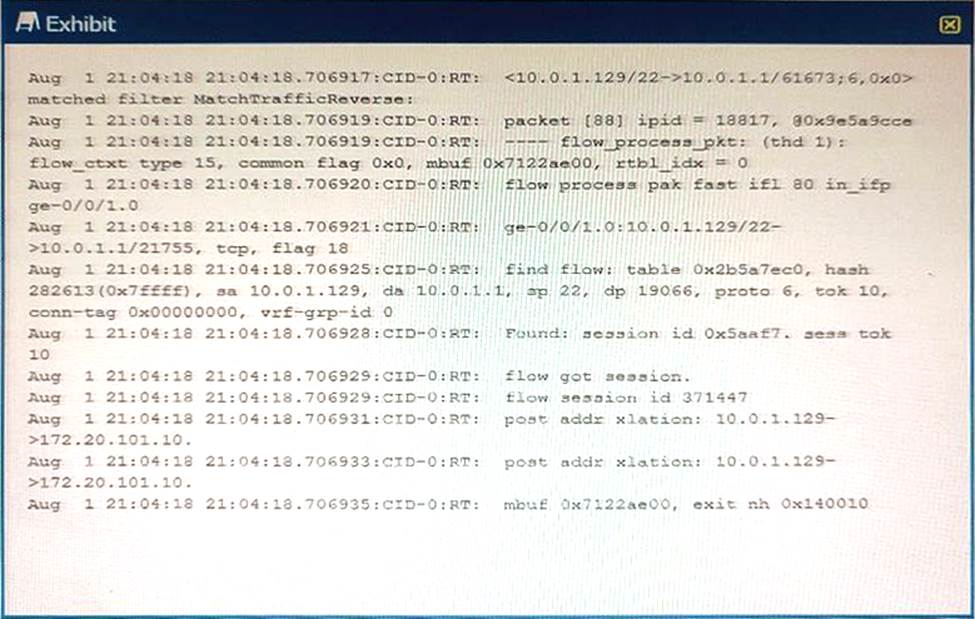
You are using traceoptions to verity NAT session information on your SRX Series device
Referring to the exhibit, which two statements are correct? (Choose two.)
- A . This packet is part of an existing session.
- B . The SRX device is changing the source address on this packet from
- C . This is the first packet in the session
- D . The SRX device is changing the destination address on this packet 10.0.1 1 to 172 20.101.10.
You must setup a Ddos solution for your ISP. The solution must be agile and not block legitimate traffic.
Which two products will accomplish this task? (Choose two.)
- A . Contrail Insights
- B . MX Series device
- C . Corero Smartwall TDD
- D . SRX Series device
BC
Explanation:
You must set up a DDoS solution for your ISP. The solution must be agile and not block legitimate traffic.
The two products that will accomplish this task are:
B) MX Series device. MX Series devices are high-performance routers that can provide DDoS protection at the network edge by integrating with Corero SmartWall Threat Defense Director (TDD) software. MX Series devices can leverage the packet processing capabilities of the MX-SPC3 Services Card to perform real-time DDoS detection and mitigation at line rate, scaling from 50 Gbps to 40 Tbps. MX Series devices can also use Juniper Networks Security Intelligence (SecIntel) to receive threat intelligence feeds from Juniper ATP Cloud or Juniper Threat Labs and apply them to the security policies. MX Series devices can provide an agile and effective DDoS solution for your ISP without blocking legitimate traffic12.
C) Corero SmartWall TDD. Corero SmartWall TDD is a software solution that runs on MX Series devices and PTX Series devices to provide DDoS protection at the network edge. Corero SmartWall TDD uses behavioral analytics and detailed network visibility to detect and block DDoS attacks in seconds, without affecting the normal traffic. Corero SmartWall TDD can also provide advanced protection from “carpet bombing” attacks, 5G DDoS visibility, and multi-tenant portal for as-a-service offerings or views by department within an enterprise. Corero SmartWall TDD can provide an agile and effective DDoS solution for your ISP without blocking legitimate traffic34.
The other options are incorrect because:
A) Contrail Insights. Contrail Insights is a software solution that provides network analytics and visibility for cloud and data center environments. Contrail Insights can help you monitor, troubleshoot, and optimize the performance and security of your network, but it does not provide DDoS protection by itself. Contrail Insights can integrate with other Juniper products, such as Contrail Enterprise Multicloud, Contrail Service Orchestration, and AppFormix, to provide a comprehensive network management solution, but it is not a DDoS solution for your ISP5.
D) SRX Series device. SRX Series devices are high-performance firewalls that can provide DDoS protection at the network perimeter by integrating with Juniper ATP Cloud and Juniper Threat Labs. SRX Series devices can use SecIntel to receive threat intelligence feeds from Juniper ATP Cloud or Juniper Threat Labs and apply them to the security policies. SRX Series devices can also use IDP to detect and prevent application-level attacks, such as SQL injection, cross-site scripting, and buffer overflow. SRX Series devices can provide a robust and effective DDoS solution for your network, but they are not designed to handle high-volume DDoS attacks at the network edge, as MX Series devices and Corero SmartWall TDD are.
Reference: Juniper and Corero Joint DDoS Protection Solution MX-SPC3 Services Card Overview
Corero SmartWall Threat Defense Director (TDD)
Juniper Networks and Corero: A Modern Approach to DDoS Protection at Scale Contrail Insights Overview
[SRX Series Services Gateways]
[Juniper Networks Security Intelligence (SecIntel)]
What is the purpose of the Switch Microservice of Policy Enforcer?
- A . to isolate infected hosts
- B . to enroll SRX Series devices with Juniper ATP Cloud
- C . to inspect traffic for malware
- D . to synchronize security policies to SRX Series devices
To analyze and detect malware, Juniper ATP Cloud performs which two functions? (Choose two.)
- A . cache lookup: to see if the file is seen already and known to be malicious
- B . antivirus scan: with a single vendor solution to see if the file contains any potential threats
- C . dynamic analysis: to see what happens if you execute the file in a real environment
- D . static analysis: to see what happens if you execute the file in a real environment
You have a webserver and a DNS server residing in the same internal DMZ subnet. The public Static NAT addresses for the servers are in the same subnet as the SRX Series devices internet-facing interface. You implement DNS doctoring to ensure remote users can access the webserver.
Which two statements are true in this scenario? (Choose two.)
- A . The DNS doctoring ALG is not enabled by default.
- B . The Proxy ARP feature must be configured.
- C . The DNS doctoring ALG is enabled by default.
- D . The DNS CNAME record is translated.
Exhibit
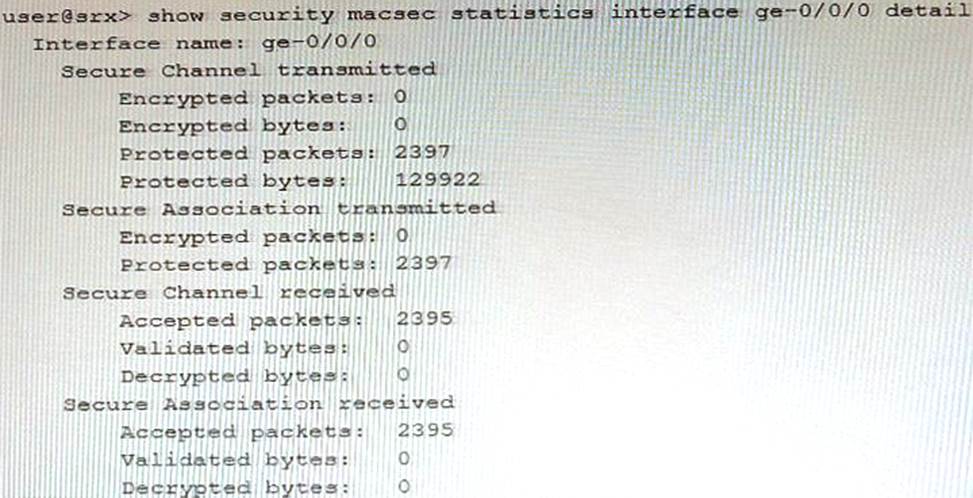
Referring to the exhibit, which two statements are true? (Choose two.)
- A . The data that traverses the ge-0/070 interface is secured by a secure association key.
- B . The data that traverses the ge-070/0 interface can be intercepted and read by anyone.
- C . The data that traverses the ge-070/0 interface cannot be intercepted and read by anyone.
- D . The data that traverses the ge-O/0/0 interface is secured by a connectivity association key.
Exhibit
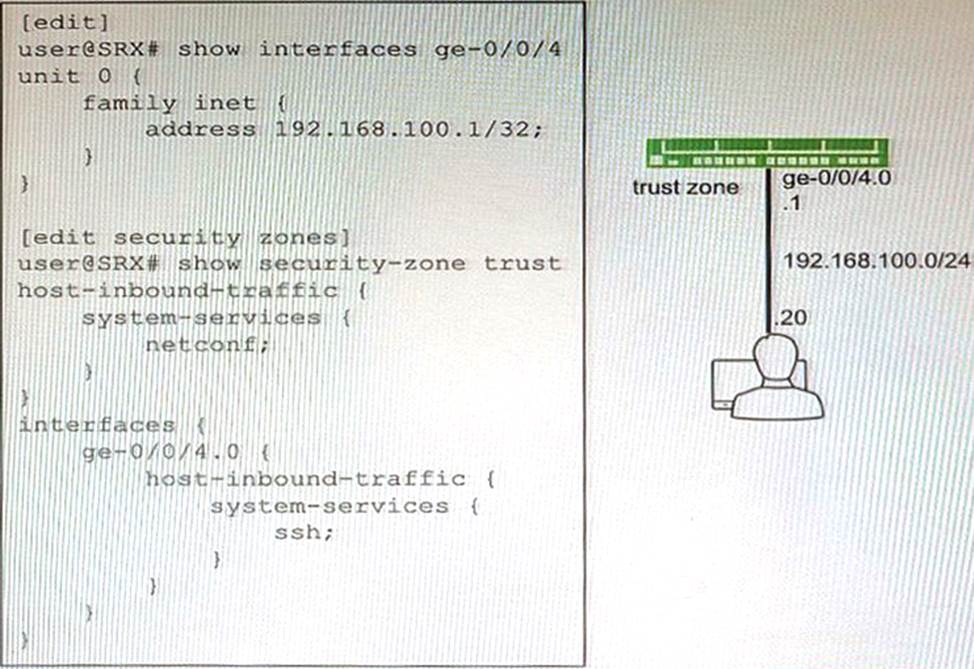
You are not able to ping the default gateway of 192.168 100 1 (or your network that is located on your SRX Series firewall.
Referring to the exhibit, which two commands would correct the configuration of your SRX Series device? (Choose two.)
A)
![]()
B)
![]()
C)
![]()
D)
![]()
- A . Option A
- B . Option B
- C . Option C
- D . Option D
Exhibit
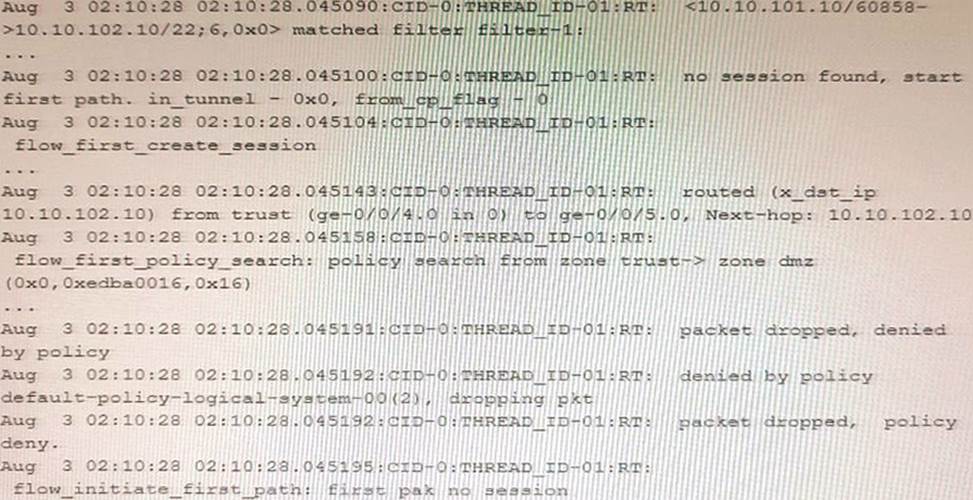
Which two statements are correct about the output shown in the exhibit? (Choose two.)
- A . The packet is processed as host inbound traffic.
- B . The packet matches the default security policy.
- C . The packet matches a configured security policy.
- D . The packet is processed in the first path packet flow.
