Practice Free JN0-335 Exam Online Questions
What are three capabilities of AppQoS? (Choose three.)
- A . re-write DSCP values
- B . assign a forwarding class
- C . re-write the TTL
- D . rate-limit traffic
- E . reserve bandwidth
A B D
Explanation:
AppQoS can modify the DSCP (Differentiated Services Code Point) values in IP packet headers. This is crucial for defining the level of service for each packet, influencing how network devices prioritize traffic.
It can assign traffic to specific forwarding classes. This feature allows network administrators to group different types of traffic (e.g., VoIP, streaming, bulk data) into categories that are treated differently based on predefined network policies, ensuring that critical applications receive the necessary bandwidth and priority.
AppQoS is capable of rate-limiting traffic, which involves setting a maximum bandwidth limit for certain types of traffic. This ensures that no single application or service consumes more bandwidth than allocated, thus preventing network congestion and ensuring fair bandwidth distribution among all applications.
These features are essential for managing network performance and ensuring that critical applications receive the necessary resources to function effectively. AppQoS does not inherently include capabilities to re-write TTL (Time To Live) values or reserve bandwidth as primary functions, but it manages bandwidth usage through rate limiting and priority settings.
Click the Exhibit button.
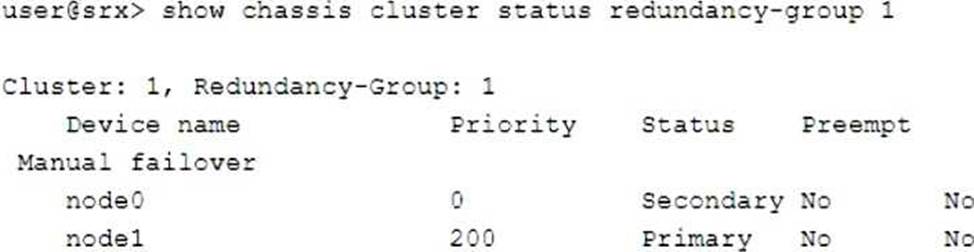
Which two statements describe the output shown in the exhibit? (Choose two.)
- A . Redundancy group 1 experienced an operational failure.
- B . Redundancy group 1 was administratively failed over.
- C . Node 0 is controlling traffic for redundancy group 1.
- D . Node 1 is controlling traffic for redundancy group 1.
C, D
Explanation:
The output indicates that node1 has a priority of 200 and is marked as "Primary," which means it is currently the active node controlling traffic for redundancy group 1. The "Primary" status designates that this node is handling the traffic for the specified redundancy group.
According to the exhibit, node0 is listed with a priority of 0 and is marked as "Secondary." This status indicates that node0 is currently not controlling traffic for redundancy group 1, serving instead in a standby role ready to take over should node1 fail or become unavailable.
Which two statements are true about Juniper ATP Cloud? (Choose two.)
- A . Dynamic analysis is always performed to determine if a file contains malware.
- B . If the cache lookup determines that a file contains malware, performed to verify the results.
- C . Dynamic analysis is not always necessary to determine if a file contains malware.
- D . If the cache lookup determines that a file contains malware, static analysis is not performed to verify the results.
C D
Explanation:
Dynamic analysis is not always necessary to determine if a file contains malware, as the ATP Cloud uses a cache lookup to quickly identify known malicious files. If the cache lookup determines that a file contains malware, static analysis is not performed to verify the results. This information can be found on the Juniper website here: https://www.juniper.net/documentation/en_US/release-independent/security/jnpr-security-srx-series/inform
Which statement defines the function of an Application Layer Gateway (ALG)?
- A . The ALG uses software processes for permitting or disallowing specific IP address ranges.
- B . The ALG uses software that is used by a single TCP session using the same port numbers as the application.
- C . The ALG contains protocols that use one application session for each TCP session.
- D . The ALG uses software processes for managing specific protocols.
D
Explanation:
The statement that defines the function of an Application Layer Gateway (ALG) is: The ALG uses software processes for managing specific protocols. An ALG is a security component that operates at the application layer (layer 7) of the OSI model and handles data associated with certain application protocols, such as SIP, FTP, RTSP, etc. An ALG acts as a proxy or intermediary between the client and the server applications and performs various functions, such as address and port translation, resource allocation, application response control, and synchronization of data and control traffic. An ALG can also inspect and modify the application payload to enable firewall or NAT traversal, prevent spoofing or DoS attacks, or enforce granular security policies based on application-specific commands. Reference: = Application-level gateway – Wikipedia, What Is an Application Layer Gateway (ALG)? | F5, What is ALG •• Application Layer Gateway | 3CX
Which two devices would you use for DDoS protection with Policy Enforcer? (Choose two.)
- A . vQFX
- B . MX
- C . vMX
- D . QFX
B C
Explanation:
The MX and vMX devices can be used for DDoS protection with Policy Enforcer. Policy Enforcer is a Juniper Networks solution that provides real-time protection from DDoS attacks. It can be used to detect and block malicious traffic, and also provides granular control over user access and policy enforcement. The MX and vMX devices are well-suited for use with Policy Enforcer due to their high-performance hardware and advanced security features.
Which two statements are correct about SSL proxy server protection? (Choose two.)
- A . You do not need to configure the servers to use the SSL proxy the function on the SRX Series device.
- B . You must load the server certificates on the SRX Series device.
- C . The servers must be configured to use the SSL proxy function on the SRX Series device.
- D . You must import the root CA on the servers.
A B
Explanation:
When using SSL proxy, the servers themselves do not require any special configuration to utilize the SSL proxy function on the SRX device. The SSL proxy operates transparently, intercepting and decrypting SSL/TLS traffic before it reaches the servers.
For the SSL proxy to function effectively, especially in server protection mode where it impersonates the server to the client, it is necessary to load the server’s certificates onto the SRX device. This allows the SRX to establish a trusted connection with the client using the server’s credentials.
Which two statements are true about Juniper ATP Cloud? (Choose two.)
- A . Juniper ATP Cloud only uses one antivirus software package to analyze files.
- B . Juniper ATP Cloud uses multiple antivirus software packages to analyze files.
- C . Juniper ATP Cloud uses antivirus software packages to protect against zero-day threats.
- D . Juniper ATP Cloud does not use antivirus software packages to protect against zero-day threats.
B, D
Explanation:
Two statements that are true about Juniper ATP Cloud are:
Juniper ATP Cloud uses multiple antivirus software packages to analyze files: Juniper ATP Cloud is a cloud-based service that provides advanced threat prevention and detection for your network. It integrates with SRX Series firewalls and MX Series routers to analyze files and network traffic for signs of malicious activity. Juniper ATP Cloud uses multiple antivirus software packages from different vendors to scan files for known malware signatures and provide a comprehensive verdict based on their results.
Juniper ATP Cloud does not use antivirus software packages to protect against zero-day threats: Juniper ATP Cloud protects against zero-day threats by using dynamic analysis, not antivirus software packages. Dynamic analysis is a method of executing files in a sandbox environment and observing their behavior and network interactions. Dynamic analysis can uncover unknown malware that may evade static analysis or signature-based detection methods.
Reference: = Juniper Advanced Threat Prevention Cloud (ATP Cloud), Juniper Advanced Threat Prevention Cloud | ATP Cloud | Juniper Networks, Breaking Down Security Complexity with Juniper Networks’ ATP Cloud
You are preparing a proposal for a new customer who has submitted the following requirements for a vSRX deployment:
— globally distributed,
— rapid provisioning,
— scale based on demand,
— and low CapEx.
Which solution satisfies these requirements?
- A . AWS
- B . Network Director
- C . Juniper ATP Cloud
- D . VMWare ESXi
A
Explanation:
The solution that satisfies the requirements for a vSRX deployment is AWS. AWS (Amazon Web Services) is a cloud computing platform that provides on-demand services such as infrastructure, platform, software, and database as a service. AWS is globally distributed, meaning that it has data centers in multiple regions around the world. AWS also allows rapid provisioning, meaning that you can launch vSRX instances in minutes using preconfigured Amazon Machine Images (AMIs) or custom templates. AWS also enables scaling based on demand, meaning that you can adjust the number and size of vSRX instances according to your network traffic and performance needs. AWS also has low CapEx (capital expenditure), meaning that you only pay for what you use and do not need to invest in hardware or maintenance costs.
Reference: = vSRX Deployment Guide for AWS, Understand vSRX Virtual Firewall with AWS, What Is Amazon Web Services?
When a security policy is deleted, which statement is correct about the default behavior of active sessions allowed by that policy?
- A . The active sessions allowed by the policy will be dropped.
- B . The active sessions allowed by the policy will be marked as a legacy flow and will continue to be forwarded.
- C . The active sessions allowed by the policy will be reevaluated by the cached
- D . The active sessions allowed by the policy will continue
B
Explanation:
When a security policy is deleted, the existing sessions that were previously allowed by that policy are not immediately dropped; instead, they are typically treated as legacy flows. This means they are allowed to continue until they naturally end or until the session timeout is reached. This behavior ensures that deleting a policy does not abruptly disrupt ongoing traffic flows that were previously authorized by that policy. This approach helps in avoiding unintended service disruptions, especially in production environments where active connections may be critical to operations.
You want to set up JSA to collect network traffic flows from network devices on your network.
Which two statements are correct when performing this task? (Choose two.)
- A . BGP FlowSpec is used to collect traffic flows from Junos OS devices.
- B . Statistical sampling increases processor utilization
- C . Statistical sampling decreases event correlation accuracy.
- D . Superflows reduce traffic licensing requirements.
C D
Explanation:
Statistical sampling involves collecting a representative subset of data rather than examining all traffic. While this method decreases processor utilization by reducing the volume of data that must be analyzed and stored, it can also lead to decreased accuracy in event correlation because not all events are captured.
Superflows in JSA are aggregated flow records that represent summaries of multiple flow records. This aggregation reduces the number of flows that need to be processed and stored, which can help in managing licensing requirements related to the volume of traffic being analyzed, especially in environments with high traffic volumes.
