Practice Free JN0-335 Exam Online Questions
Which method does the loT Security feature use to identify traffic sourced from IoT devices?
- A . The SRX Series device streams metadata from the loT device transit traffic to Juniper ATP Cloud Juniper ATP Cloud.
- B . The SRX Series device streams transit traffic received from the IoT device to Juniper ATP Cloud.
- C . The SRX Series device identifies loT devices using their MAC address.
- D . The SRX Series device identifies loT devices from metadata extracted from their transit traffic.
D
Explanation:
The metadata is used to identify the type of device, its associated activities and its threat profile. This information is used to determine the appropriate security policy for the device. For more information on loT Security, please refer to the Juniper Security, Specialist (JNCIS-SEC) study guide.
Which statement about security policy schedulers is correct?
- A . Multiple policies can use the same scheduler.
- B . A policy can have multiple schedulers.
- C . When the scheduler is disabled, the policy will still be available.
- D . A policy without a defined scheduler will not become active
A
Explanation:
Schedulers can be defined and reused by multiple policies, allowing for more efficient management of policy activation and deactivation. This can be particularly useful for policies that need to be activated during specific time periods, such as business hours or maintenance windows.
Exhibit
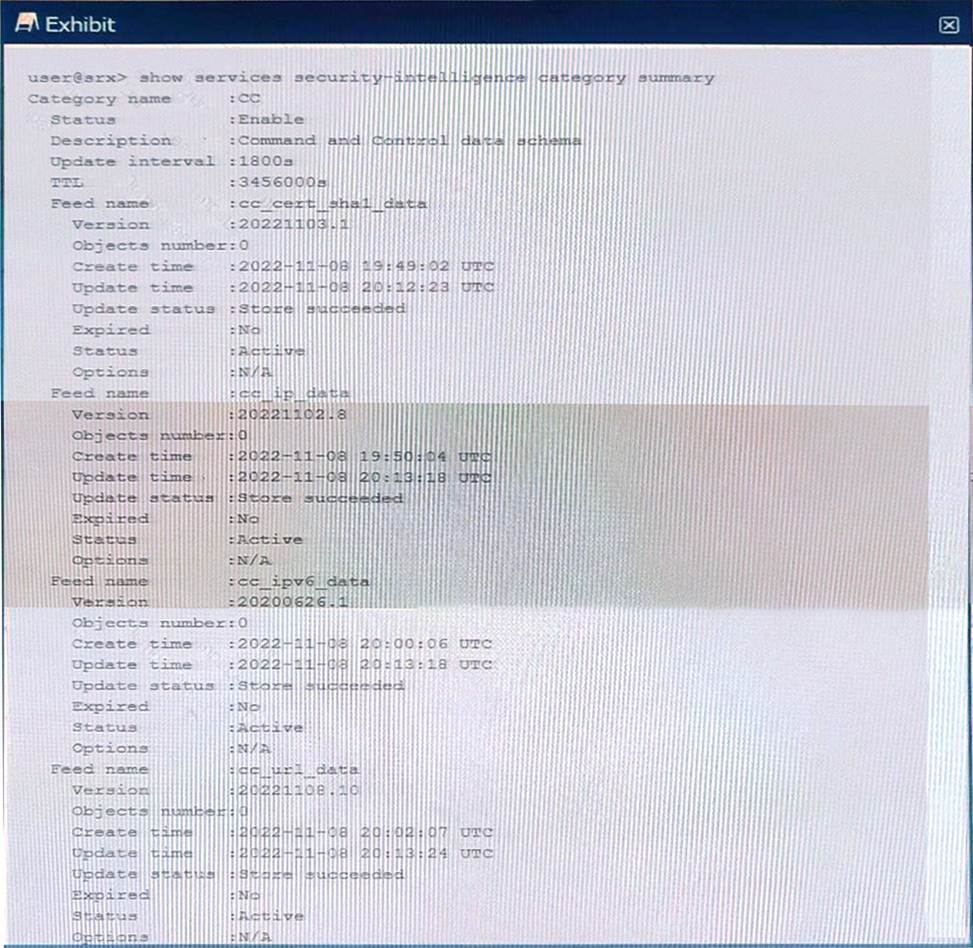
You just finished setting up your command-and-control (C&C) category with Juniper ATP Cloud. You notice that all of the feeds have zero objects in them.
Which statement is correct in this scenario?
- A . The security intelligence policy must be configured; on a unified security policy
- B . Use the commit full command to start the download.
- C . No action is required, the feeds take a few minutes to download.
- D . Set the maximum C&C entries within the Juniper ATP Cloud GUI.
C
Explanation:
According to the Juniper Networks JNCIS-SEC Study Guide, when you set up your command-and-control (C&C) category with Juniper ATP Cloud, all of the feeds will initially have zero objects in them. This is normal, as it can take a few minutes for the feeds to download. No action is required in this scenario and you will notice the feeds start to populate with objects once the download is complete.
You want to be alerted if the wrong password is used more than three times on a single device within five minutes.
Which Juniper Networks solution will accomplish this task?
- A . Adaptive Threat Profiling
- B . Juniper Secure Analytics
- C . Juniper Identity Management Service
- D . Intrusion Prevention System
B
Explanation:
The Juniper Networks solution that will accomplish the task of alerting if the wrong password is used more than three times on a single device within five minutes is Juniper Secure Analytics (JSA). JSA is a security intelligence platform that collects, analyzes, and correlates network data from various sources, such as firewalls, routers, switches, servers, and applications. JSA can detect and respond to threats, anomalies, and vulnerabilities in real time using rules, offenses, reports, and dashboards. JSA can also integrate with JIMS (Juniper Identity Management Service) to obtain user identity information from Active Directory domains or syslog sources. JSA can use this information to create custom rules that trigger offenses or alerts based on user behavior or activity, such as failed login attempts or password changes.
Reference: = Juniper Secure Analytics Troubleshooting Guide, Juniper Identity Management Service User Guide
Which two statements about SRX Series device chassis clusters are correct? (Choose two.)
- A . The chassis cluster data plane is connected with revenue ports.
- B . The chassis cluster can contain a maximum of three devices.
- C . The chassis cluster data plane is connected with SPC ports.
- D . The chassis cluster can contain a maximum of two devices.
A, D
Explanation:
Two statements that are correct about SRX Series device chassis clusters are:
The chassis cluster data plane is connected with revenue ports: A chassis cluster is a high-availability feature that groups two identical SRX Series devices into a cluster that acts as a single device. The cluster has two types of links: control links and fabric links. The control links are used for exchanging heartbeat messages and configuration synchronization between the nodes. The fabric links are used for forwarding data traffic between the nodes. The fabric links are connected with revenue ports, which are regular Ethernet interfaces that can also be used for normal traffic when not in cluster mode.
The chassis cluster can contain a maximum of two devices: A chassis cluster can only consist of two nodes: node 0 and node 1. The nodes must be the same model, have the same hardware configuration, run the same software version, and have the same license keys. The nodes share a common configuration and act as backup for each other in case of failure.
Reference: = Configuring Chassis Clustering on SRX Series Devices, SRX Series Chassis Cluster Configuration Overview, Connecting SRX Series Firewalls to Create a Chassis Cluster
Exhibit
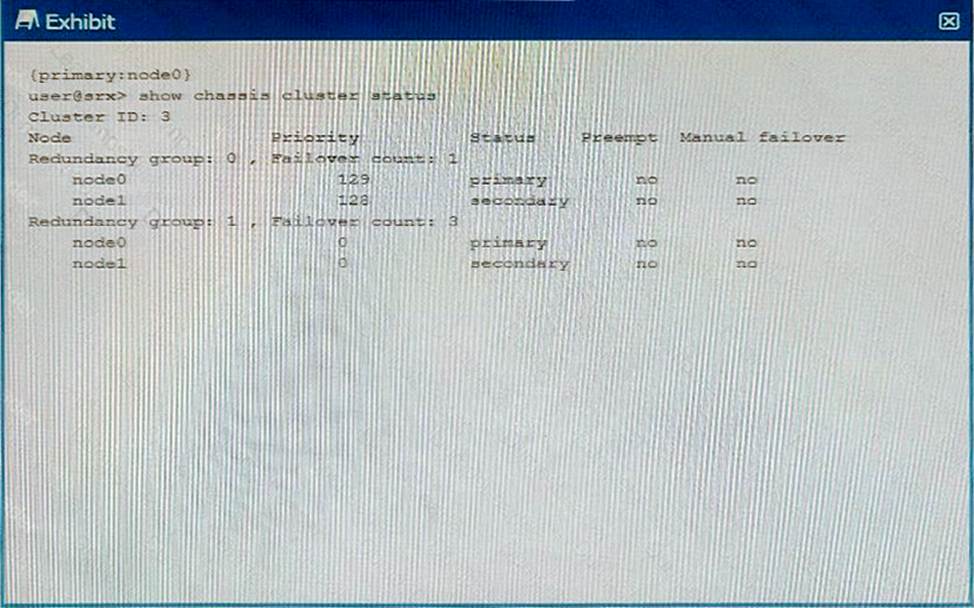
Using the information from the exhibit, which statement is correct?
- A . Redundancy group 1 is in an ineligible state.
- B . Node1 is the active node for the control plane
- C . There are no issues with the cluster.
- D . Redundancy group 0 is in an ineligible state.
You want to control when cluster failovers occur.
In this scenario, which two specific parameters would you configure on an SRX Series device? (Choose two.)
- A . hearcbeac-interval
- B . heartbeac-address
- C . hearcbeat-cos
- D . hearcbeac-chreshold
A, D
Explanation:
To control when cluster failovers occur, you need to configure two specific parameters on an SRX Series device: heartbeat-interval and heartbeat-threshold. These parameters determine how often the nodes in a cluster exchange heartbeat messages and how many consecutive heartbeats can be missed before a failover is triggered. The heartbeat-interval specifies the time interval in seconds between each heartbeat message. The default value is 1 second and the range is from 0.1 to 10 seconds. The heartbeat-threshold specifies the number of consecutive heartbeats that must be missed before a failover occurs. The default value is 3 and the range is from 2 to 255. Reference: = Configuring Chassis Clustering on SRX Series Devices, Chassis Cluster Redundancy Group Failover
Click the Exhibit button.
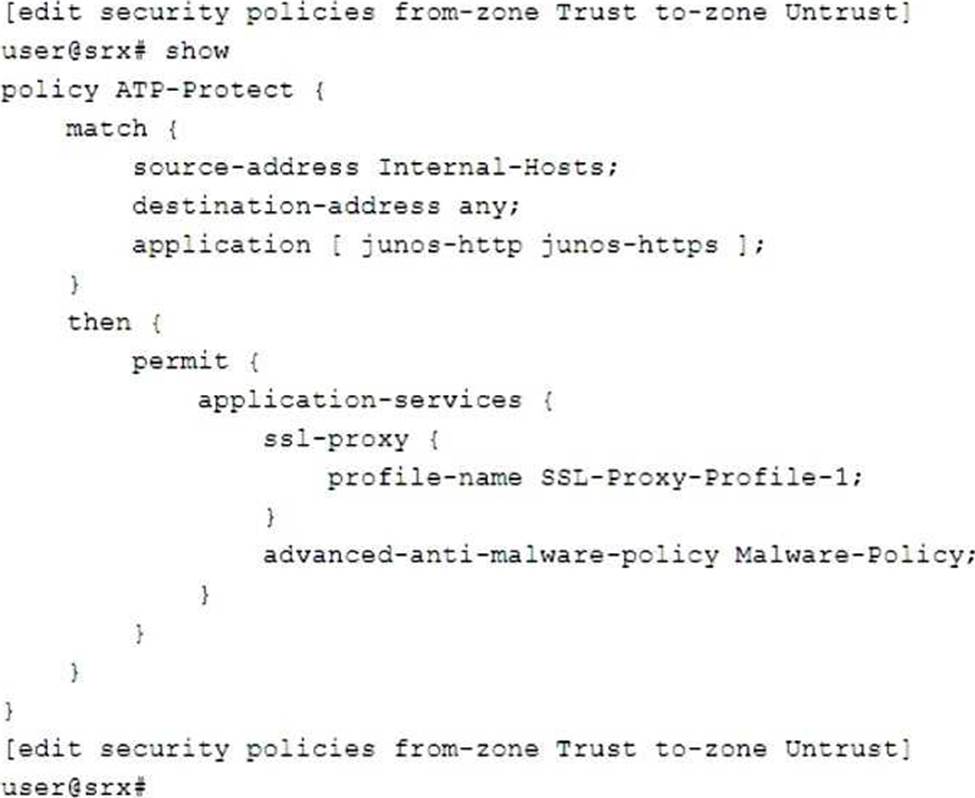
You are asked to create a security policy that will automatically add infected hosts to the infected hosts feed and block further communication through the SRX Series device.
What needs to be added to this configuration to complete this task?
- A . Add a security intelligence policy to the permit portion of the security policy.
- B . Add an action to the permit portion of the security policy.
- C . Add logging to the permit portion of the security policy.
- D . Add a match rule to the security policy with an appropriate threat level.
A
Explanation:
To create a security policy that will automatically add infected hosts to the infected hosts feed and block further communication through the SRX Series device, you need to add a security intelligence policy to the permit portion of the security policy. A security intelligence policy is a policy that allows you to block or monitor traffic from malicious sources based on threat intelligence feeds from Juniper ATP Cloud or other providers. One of the feeds that you can use is the Infected-Hosts feed, which contains IP addresses of hosts that are infected with malware and communicate with command-and-control servers. You can create a profile and a rule for the Infected-Hosts feed and specify the threat level and the action to take for the infected hosts. Then, you can link the security intelligence policy with the firewall policy and apply it to the traffic that you want to protect. Reference: = Security Intelligence Overview, Configuring Security Intelligence Policy, Configure the Security Intelligence Policy on the SRX Series Device
What are two benefits of using a vSRX in a software-defined network? (Choose two.)
- A . scalability
- B . no required software license
- C . granular security
- D . infinite number of interfaces
A C
Explanation:
– Scalability: vSRX instances can be easily added or removed as the needs of the network change, making it a flexible option for scaling in a software-defined network.
– Granular Security: vSRX allows for granular security policies to be enforced at the virtual interface level, making it an effective solution for securing traffic in a software-defined network.
The two benefits of using a vSRX in a software-defined network are scalability and granular security. Scalability allows you to increase the number of resources available to meet the demands of network traffic, while granular security provides a level of control and flexibility to your network security that is not possible with a traditional firewall. With a vSRX, you can create multiple levels of security policies, rules, and access control lists to ensure that only authorized traffic can enter and exit your network. Additionally, you would not require a software license to use the vSRX, making it an economical solution for those looking for increased security and flexibility.
Which two sources are used by Juniper Identity Management Service (JIMS) for collecting username and device IP addresses? (Choose two.)
- A . Microsoft Exchange Server event logs
- B . DNS
- C . Active Directory domain controller event logs
- D . OpenLDAP service ports
B C
Explanation:
Juniper Identity Management Service (JIMS) collects username and device IP addresses from both DNS and Active Directory domain controller event logs. DNS is used to resolve hostnames to IP addresses, while Active Directory domain controller event logs are used to get information about user accounts, such as when they last logged in.
