Practice Free HPE6-A84 Exam Online Questions
Refer to the scenario.
A customer has an AOS10 architecture that is managed by Aruba Central. Aruba infrastructure devices authenticate clients to an Aruba ClearPass cluster.
In Aruba Central, you are examining network traffic flows on a wireless IoT device that is categorized as “Raspberry Pi” clients. You see SSH traffic. You then check several more wireless IoT clients and see that they are sending SSH also.
You want an easy way to communicate the information that an IoT client has used SSH to Aruba ClearPass Policy Manager (CPPM).
What step should you take?
- A . On CPPM create an Endpoint Context Server that points to the Central API.
- B . On CPPM enable Device Insight integration.
- C . On Central configure APs and gateways to use CPPM as the RADIUS accounting server.
- D . On Central set up CPPM as a Webhook application.
The customer needs a way for users to enroll new wired clients in Intune. The clients should have limited access that only lets them enroll and receive certificates. You plan to set up these rights in an AOS-CX role named “provision.”
The customer’s security team dictates that you must limit these clients’ Internet access to only the necessary sites. Your switch software supports IPv4 and IPv6 addresses for the rules applied in the “provision” role.
What should you recommend?
- A . Configuring the rules for the “provision” role with IPv6 addresses, which tend to be more stable
- B . Enabling tunneling to the MCs on the “provision” role and then setting up the privileges on the MCs
- C . Configuring the “provision” role as a downloadable user role (DUR) in CPPM
- D . Assigning the “provision” role to a VLAN and then setting up the rules within a Layer 2 access control list (ACL)
A customer wants CPPM to authenticate non-802.1X-capable devices.
An admin has created the service shown in the exhibits below:
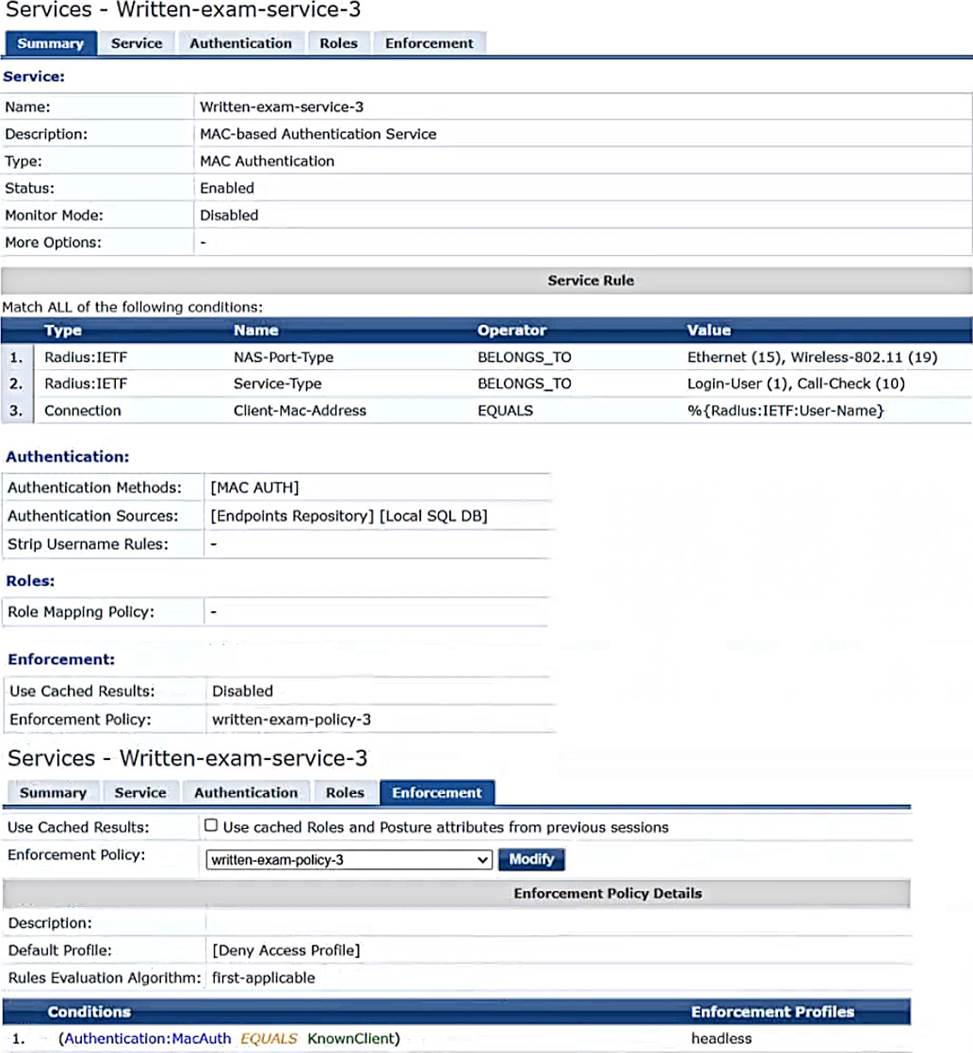
What is one recommendation to improve security?
- A . Adding an enforcement policy rule that denies access to endpoints with the Conflict flag
- B . Using Active Directory as the authentication source
- C . Creating and using a custom MAC-Auth authentication method
- D . Enabling caching of posture and roles
Refer to the scenario.
A customer requires these rights for clients in the “medical-mobile” AOS firewall role on Aruba Mobility Controllers (MCs):
Permitted to receive IP addresses with DHCP
Permitted access to DNS services from 10.8.9.7 and no other server
Permitted access to all subnets in the 10.1.0.0/16 range except denied access to 10.1.12.0/22
Denied access to other 10.0.0.0/8 subnets
Permitted access to the Internet
Denied access to the WLAN for a period of time if they send any SSH traffic
Denied access to the WLAN for a period of time if they send any Telnet traffic
Denied access to all high-risk websites
External devices should not be permitted to initiate sessions with “medical-mobile” clients, only send return traffic.
The line below shows the effective configuration for the role.
There are multiple issues with this configuration.
What is one change you must make to meet the scenario requirements? (In the options, rules in a policy are referenced from top to bottom. For example, “medical-mobile” rule 1 is “ipv4 any any svc-dhcp permit,” and rule 6 is “ipv4 any any any permit’.)
- A . Apply the “apprf-medical-mobile-sacl" policy explicitly to the “medical-mobile” user-role under the “medical-mobile” policy.
- B . In the “medical-mobile” policy, change the action for rules 2 and 3 to reject.
- C . In the “medical-mobile” policy, move rule 5 under rule 6.
- D . In the “medical-mobile” policy, change the subnet mask in rule 5 to 255.255.252.0.
Refer to the scenario.
# Introduction to the customer
You are helping a company add Aruba ClearPass to their network, which uses Aruba network infrastructure devices.
The company currently has a Windows domain and Windows CA. The Window CA issues certificates to domain computers, domain users, and servers such as domain controllers. An example of a certificate issued by the Windows CA is shown here.
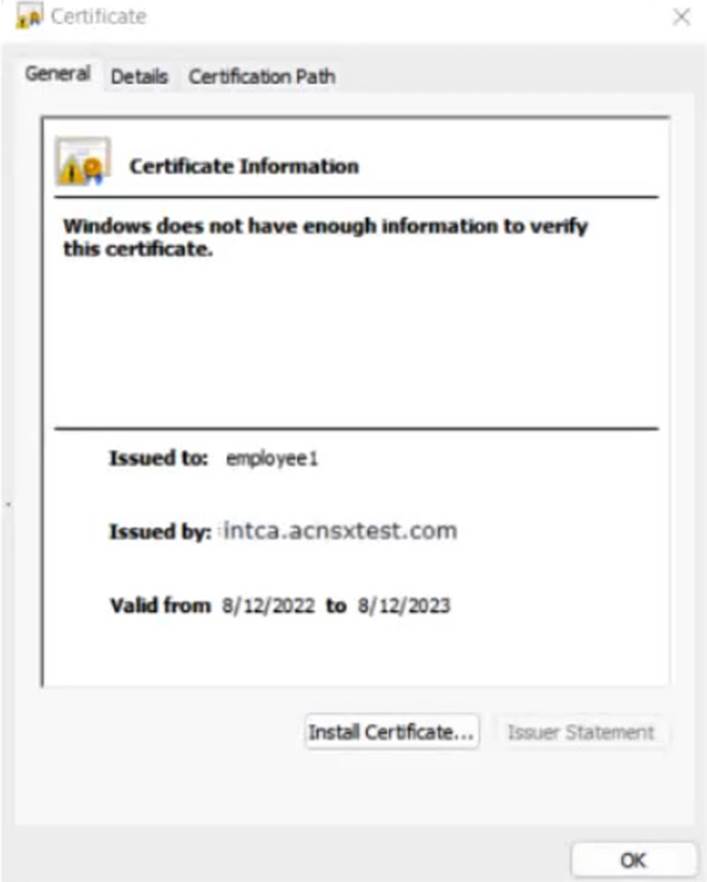
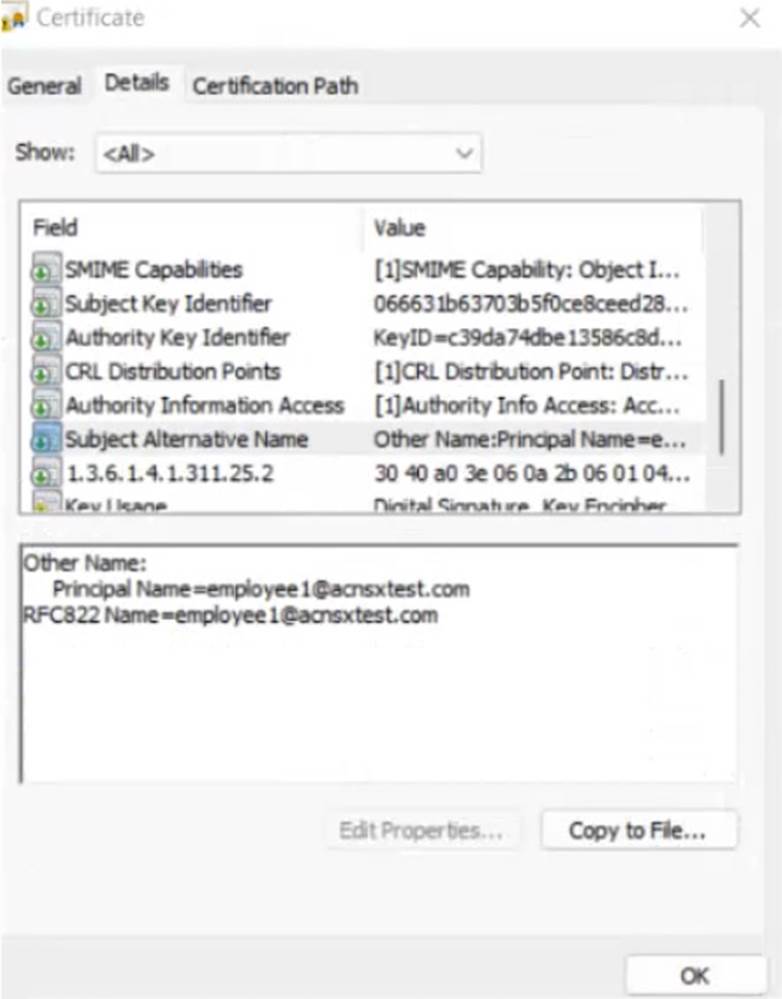
The company is in the process of adding Microsoft Endpoint Manager (Intune) to manage its mobile clients. The customer is maintaining the on-prem AD for now and uses Azure AD Connect to sync with Azure AD.
# Requirements for issuing certificates to mobile clients
The company wants to use ClearPass Onboard to deploy certificates automatically to mobile clients enrolled in Intune. During this process, Onboard should communicate with Azure AD to validate the clients. High availability should also be provided for this scenario; in other words, clients should be able to get certificates from Subscriber 2 if Subscriber 1 is down.
The Intune admins intend to create certificate profiles that include a UPN SAN with the UPN of the user who enrolled the device.
# Requirements for authenticating clients
The customer requires all types of clients to connect and authenticate on the same corporate SSID.
The company wants CPPM to use these authentication methods:
EAP-TLS to authenticate users on mobile clients registered in Intune TEAR, with EAP-TLS as the inner method to authenticate Windows domain computers and the users on them
To succeed, EAP-TLS (standalone or as a TEAP method) clients must meet these requirements:
Their certificate is valid and is not revoked, as validated by OCSP
The client’s username matches an account in AD
# Requirements for assigning clients to roles
After authentication, the customer wants the CPPM to assign clients to ClearPass roles based on the following rules:
Clients with certificates issued by Onboard are assigned the “mobile-onboarded” role
Clients that have passed TEAP Method 1 are assigned the “domain-computer” role
Clients in the AD group “Medical” are assigned the “medical-staff” role
Clients in the AD group “Reception” are assigned to the “reception-staff” role
The customer requires CPPM to assign authenticated clients to AOS firewall roles as follows:
Assign medical staff on mobile-onboarded clients to the “medical-mobile” firewall role
Assign other mobile-onboarded clients to the “mobile-other” firewall role
Assign medical staff on domain computers to the “medical-domain” firewall role
All reception staff on domain computers to the “reception-domain” firewall role
All domain computers with no valid user logged in to the “computer-only” firewall role
Deny other clients access –
# Other requirements
Communications between ClearPass servers and on-prem AD domain controllers must be encrypted.
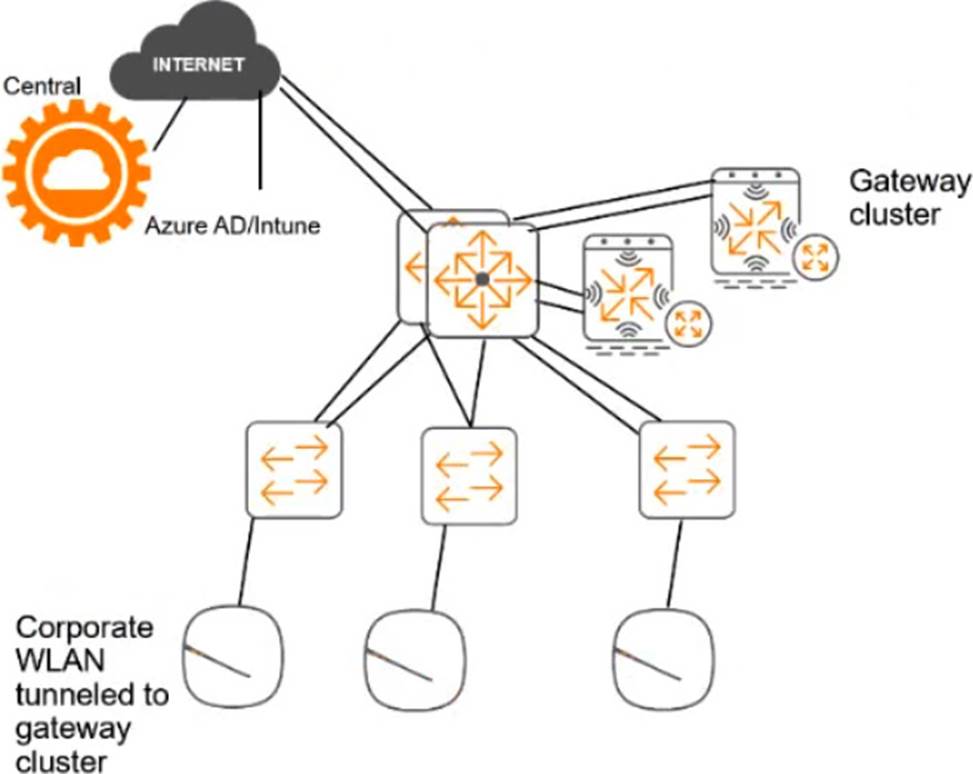
# Network topology
For the network infrastructure, this customer has Aruba APs and Aruba gateways, which are managed by Central. APs use tunneled WLANs, which tunnel traffic to the gateway cluster. The customer also has AOS-CX switches that are not managed by Central at this point.
# ClearPass cluster IP addressing and hostnames
A customer’s ClearPass cluster has these IP addresses:
Publisher = 10.47.47.5 –
Subscriber 1 = 10.47.47.6 –
Subscriber 2 = 10.47.47.7 –
Virtual IP with Subscriber 1 and Subscriber 2 = 10.47.47.8
The customer’s DNS server has these entries
cp.acnsxtest.com = 10.47.47.5
cps1.acnsxtest.com = 10.47.47.6
cps2.acnsxtest.com = 10.47.47.7
radius.acnsxtest.com = 10.47.47.8
onboard.acnsxtest.com = 10.47.47.8
You have created a role mapping policy as shown in the exhibits below.
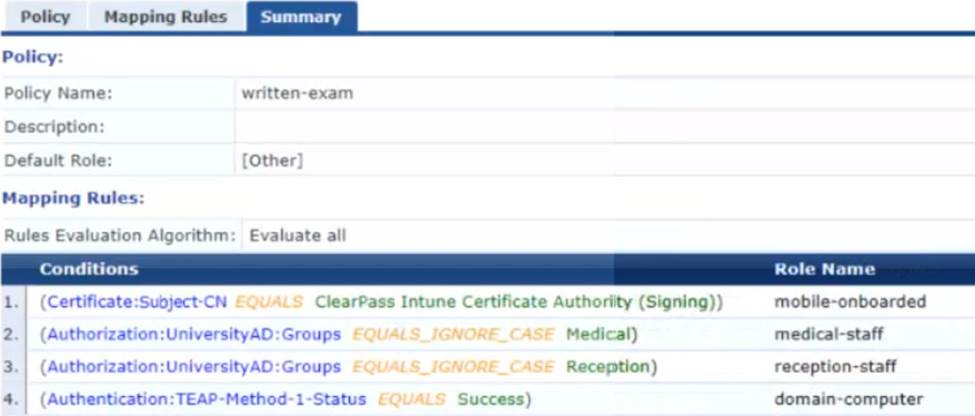
What is one change that you need to make to this policy?
- A . In rule 1 change Subject-CN to Issuer-CN.
- B . Move rules 2 and 3 to the top of the list.
- C . Change the rules evaluation mechanism to first applicable.
- D . Change the default role to “mobile-onboarded.”
Refer to the scenario.
A customer has an AOS10 architecture that is managed by Aruba Central. Aruba infrastructure devices authenticate clients to an Aruba ClearPass cluster.
In Aruba Central, you are examining network traffic flows on a wireless IoT device that is categorized as “Raspberry Pi” clients. You see SSH traffic. You then check several more wireless IoT clients and see that they are sending SSH also.
You want a relatively easy way to communicate the information that an IoT client has used SSH to Aruba CPPM.
What is one prerequisite?
- A . Enable event processing on subscribers in the ClearPass cluster.
- B . In CPPM’s CA trust list, add the Aruba Infrastructure usage to the DigiCert certificate.
- C . Obtain a data collector token from Central’s platform integration settings.
- D . Create an API application and token within the REST API settings.
You are setting up Aruba ClearPass Policy Manager (CPPM) to enforce EAP-TLS authentication with Active Directory as the authentication source. The company wants to prevent users with disabled accounts from connecting even if those users still have valid certificates.
As the first part of meeting these criteria, what should you do to enable CPPM to determine where accounts are enabled in AD or not?
- A . Add an Endpoint Context Server to the domain controller with actions for querying the domain controller for account status.
- B . Enable OCSP in the EAP-TLS authentication method settings and configure an OCSP override to the domain controller FQDN.
- C . Add a custom attribute for user Account Control to the filters in the AD authentication source.
- D . Install a Microsoft Active Directory extension in Aruba ClearPass Guest and set up an HTTP authentication source that points to that extension.
Refer to the scenario.
A customer has asked you to review their AOS-CX switches for potential vulnerabilities.
The configuration for these switches is shown below:
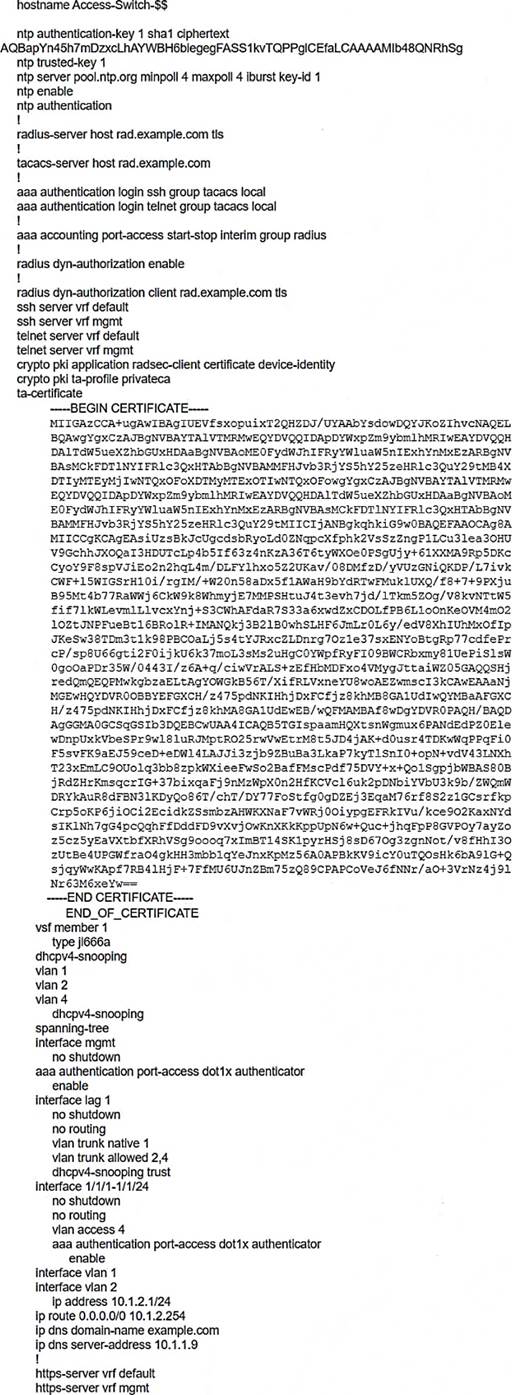
What is one recommendation to make?
- A . Let the RADIUS server configure VLANs on LAG 1 dynamically.
- B . Use MDS instead of SHA1 for the NTP authentication key.
- C . Encrypt the certificate in the TA-profile.
- D . Create a control plane ACL to limit the sources that can access the switch with SSH.
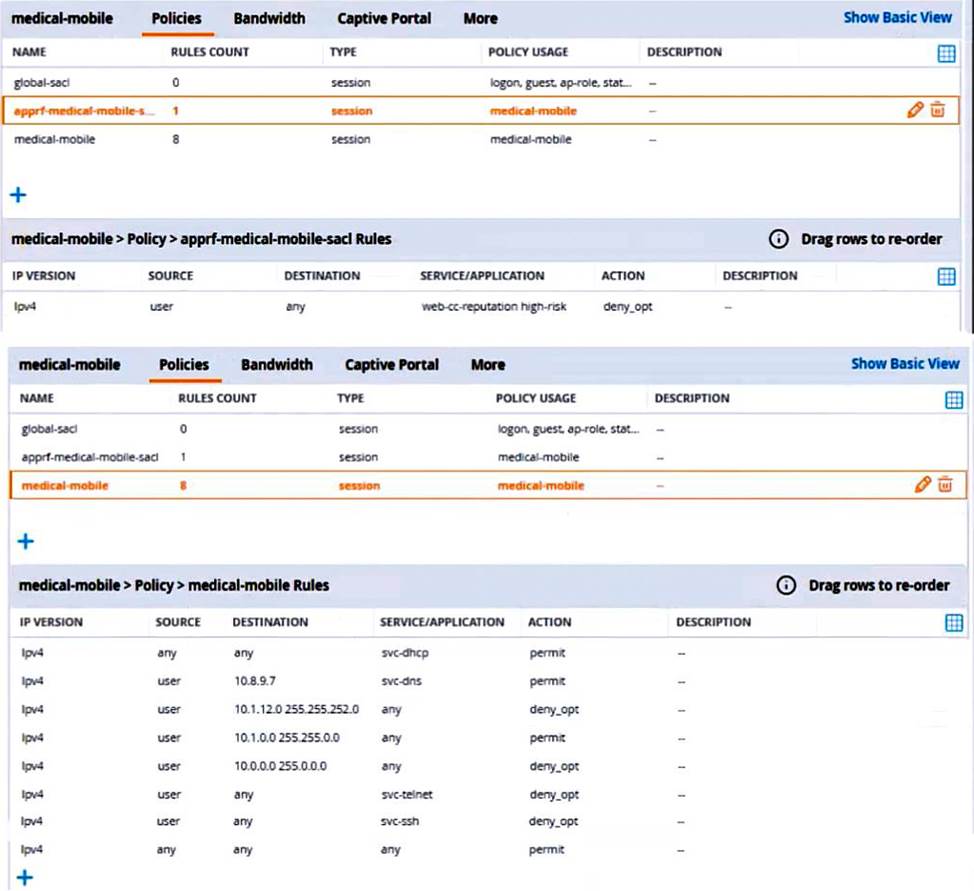
Refer to the scenario.
A customer requires these rights for clients in the “medical-mobile” AOS firewall role on Aruba Mobility Controllers (MCs):
Permitted to receive IP addresses with DHCP
Permitted access to DNS services from 10.8.9.7 and no other server
Permitted access to all subnets in the 10.1.0.0/16 range except denied access to 10.1.12.0/22
Denied access to other 10.0.0.0/8 subnets
Permitted access to the Internet
Denied access to the WLAN for a period of time if they send any SSH traffic
Denied access to the WLAN for a period of time if they send any Telnet traffic
Denied access to all high-risk websites
External devices should not be permitted to initiate sessions with “medical-mobile” clients, only send return traffic.
The exhibits below show the configuration for the role.
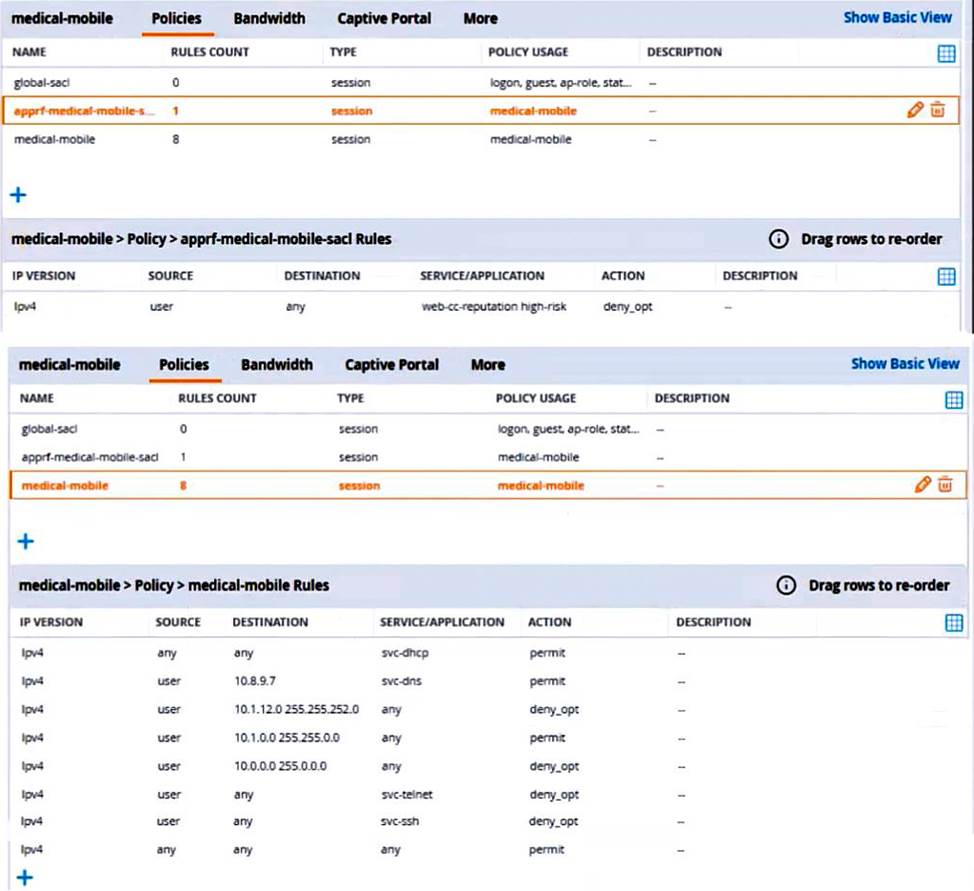
There are multiple issues with the configuration.
What is one of the changes that you must make to the policies to meet the scenario requirements? (In the options, rules in a policy are referenced from top to bottom. For example, “medical-mobile” rule 1 is “ipv4 any any svc-dhcp permit,” and rule 8 is “ipv4 any any any permit’.)
- A . In the “medical-mobile” policy, change the source in rule 1 to “user.”
- B . In the “medical-mobile” policy, change the subnet mask in rule 3 to 255.255.248.0.
- C . In the “medical-mobile” policy, move rules 6 and 7 to the top of the list.
- D . Move the rule in the “apprf-medical-mobile-sacl” policy between rules 7 and 8 in the “medical-mobile” policy.
Refer to the scenario.
An organization wants the AOS-CX switch to trigger an alert if its RADIUS server (cp.acnsxtest.local) rejects an unusual number of client authentication requests per hour. After some discussions with other Aruba admins, you are still not sure how many rejections are usual or unusual. You expect that the value could be different on each switch.
You are helping the developer understand how to develop an NAE script for this use case.
You are helping a customer define an NAE script for AOS-CX switches. The script will monitor statistics from a RADIUS server defined on the switch. You want to future proof the script by enabling admins to select a different hostname or IP address for the monitored RADIUS server when they create an agent from the script.
What should you recommend?
- A . Use this variable, %{radius-ip}, when defining the monitor URI in the NAE agent script.
- B . Define a parameter for the RADIUS server; reference that parameter instead of the server name/ip when defining the monitor URI.
- C . Use a callback action to collect the name of any RADIUS servers defined on the switch at the time the agent is created.
- D . Make the script editable so that admins can edit it on demand when they are creating scripts.
