Practice Free CWSP-207 Exam Online Questions
What 802.11 WLAN security problem is directly addressed by mutual authentication?
- A . Wireless hijacking attacks
- B . Weak password policies
- C . MAC spoofing
- D . Disassociation attacks
- E . Offline dictionary attacks
- F . Weak Initialization Vectors
When 802.1X/EAP is properly deployed, which of these external databases can a RADIUS server query for proxy authentication?
- A . Active Directory
- B . E-Directory
- C . Open Directory
- D . All of the above
WLAN administrator Marko Tisler is troubleshooting an IPsec VPN problem that has been deployed as the security solution over a point-to-point 802.11 wireless bridge link between two buildings.
Marko cannot get the VPN tunnel to establish and notices that the IKE Phase 1 exchange is successful; however, IKE Phase 2 is failing.
What are the possible causes of this problem? (Choose all that apply.)
- A . The VPN server behind the root bridge is using AES-256 encryption and the VPN endpoint device behind the nonroot bridge is using AES-192 encryption.
- B . The VPN server behind the root bridge is using SHA-1 hash for data integrity and the VPN endpoint device behind the nonroot bridge is using MD-5 for data integrity.
- C . The root CA certificate installed on the VPN device behind the nonroot bridge was not used to sign the server certificate on the VPN server behind the root bridge.
- D . The clock settings of the VPN server that sits behind the root bridge predate the creation of the server certificate.
- E . The public/private IP address settings are misconfigured on the VPN device behind the nonroot bridge.
Given: XYZ Hospital plans to improve the security and performance of their Voice over Wi-Fi implementation and will be upgrading to 802.11n phones with 802.1X/EAP authentication.
XYZ would like to support fast secure roaming for the phones and will require the ability to troubleshoot reassociations that are delayed or dropped during inter-channel roaming.
What portable solution would be recommended for XYZ to troubleshoot roaming problems?
- A . WIPS sensor software installed on a laptop computer
- B . Spectrum analyzer software installed on a laptop computer
- C . An autonomous AP mounted on a mobile cart and configured to operate in monitor mode
- D . Laptop-based protocol analyzer with multiple 802.11n adapters
WLAN administrator Alexandra Gunther recently upgraded her company’s WLAN infrastructure with APs that are Voice Enterprise certified.
She configured the APs for fast BSS transition (FT) and deployed new iPads that also support FT. The iPads are roaming in a fast and secure manner; however, she noticed that some older laptops can no longer connect to the WLAN.
What is the cause of the problem?
- A . FT is not backward compatible with legacy client devices.
- B . FT clients and OKC clients cannot connect to the same SSID.
- C . FT and PMK caching clients cannot connect to the same SSID.
- D . The laptop radio drivers cannot decipher the FT information element in the AP beacon.
What are the three roles of the 802.1X framework, as defined by the 802.1X standard, that are performed by the client STA, the AP (or WLAN controller), and the RADIUS server? (Choose 3)
- A . Enrollee
- B . Registrar
- C . AAA Server
- D . Authentication Server
- E . Supplicant
- F . Authenticator
- G . Control Point
Given: The ABC Corporation currently utilizes an enterprise Public Key Infrastructure (PKI) to allow employees to securely access network resources with smart cards.
The new wireless network will use WPA2-Enterprise as its primary authentication solution. You have been asked to recommend a Wi-Fi Alliance-tested EAP method.
What solutions will require the least change in how users are currently authenticated and still integrate with their existing PKI?
- A . EAP-FAST
- B . EAP-TLS
- C . PEAPv0/EAP-MSCHAPv2
- D . LEAP
- E . PEAPv0/EAP-TLS
- F . EAP-TTLS/MSCHAPv2
The ACME Company is using WPA2-Personal to secure handheld barcode scanners that are not capable of 802.1X/EAP authentication.
Because an employee was recently fired, all the barcode scanners and APs had to be reconfigured with a new static 64-bit PSK.
What type of WLAN security solution may have avoided this administrative headache?
- A . MAC filter
- B . Hidden SSID
- C . Change the default settings
- D . Proprietary PSK
You have been tasked with troubleshooting a client connectivity problem at your company’s headquarters. All the APs and employee iPads are configured for PSK authentication.
An employee notices that he cannot connect his iPad to the AP in the reception area of the main building but can connect to other APs.
View the following graphic and describe the cause of the problem.
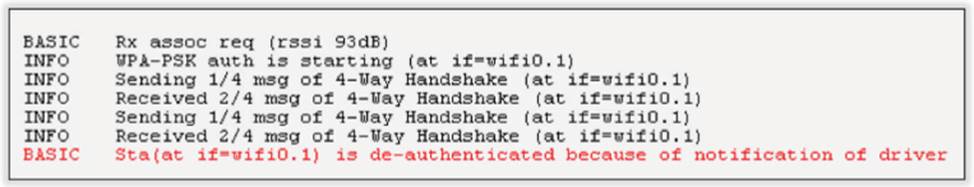
- A . The WLAN client driver is not communicating properly with the device’s OS.
- B . The APs are configured for CCMP encryption only. The client only supports TKIP.
- C . The client has been configured with the wrong WPA2 Personal passphrase.
- D . The AP in the reception area has been configured with the wrong WPA2 Personal passphrase.
When you are using an 802.11 wireless controller solution, which device would you consider the authenticator?
- A . Access point
- B . RADIUS database
- C . LDAP
- D . WLAN controller
- E . VLAN
