Practice Free CWSP-207 Exam Online Questions
What are some of the purposes of the 4-Way Handshake? (Choose all that apply.)
- A . Transfer the GTK to the supplicant.
- B . Derive a PTK from the PMK.
- C . Transfer the GMK to the supplicant.
- D . Confirm cipher suites.
What are of some of the common security capabilities often found in a WLAN controller?
- A . VPN server
- B . Firewall
- C . RADIUS server
- D . WIPS
- E . All of the above
This graphic shows a WLAN discovery tool screen capture.
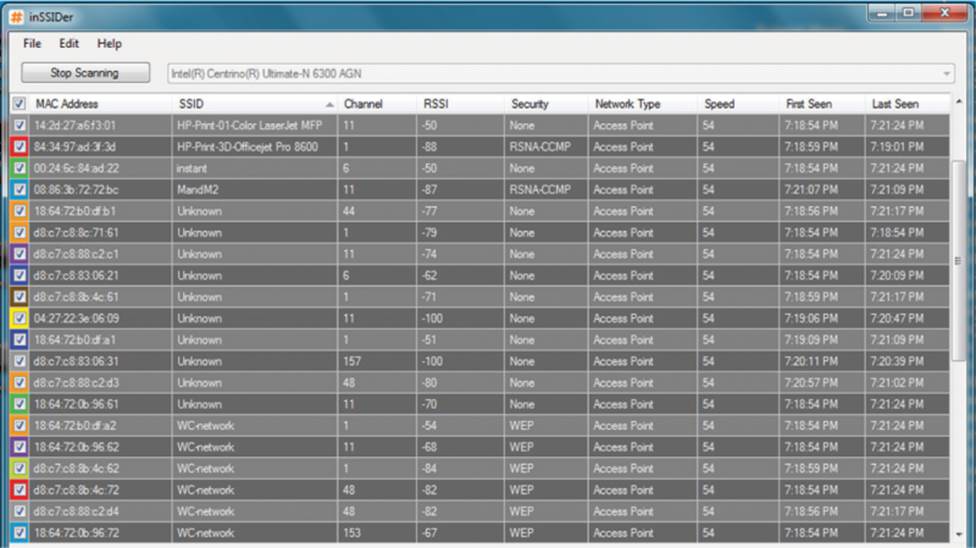
How many SSIDs are configured with cloaking enabled? (Choose all that apply.)
- A . None
- B . At least ten
- C . One
- D . Ten
- E . Exact number cannot be determined
Given: WLAN attacks are typically conducted by hackers to exploit a specific vulnerability within a network.
What statement correctly pairs the type of WLAN attack with the exploited vulnerability? (Choose 3)
- A . Management interface exploit attacks are attacks that use social engineering to gain credentials from managers.
- B . Zero-day attacks are always authentication or encryption cracking attacks.
- C . RF DoS attacks prevent successful wireless communication on a specific frequency or frequency range.
- D . Hijacking attacks interrupt a user’s legitimate connection and introduce a new connection with an evil twin AP.
- E . Social engineering attacks are performed to collect sensitive information from unsuspecting users
- F . Association flood attacks are Layer 3 DoS attacks performed against authenticated client stations
Given: You are using a Wireless Aggregator utility to combine multiple packet captures. One capture exists for each of channels 1, 6 and 11.
What kind of troubleshooting are you likely performing with such a tool?
- A . Wireless adapter failure analysis.
- B . Interference source location.
- C . Fast secure roaming problems.
- D . Narrowband DoS attack detection.
The ___________ key is used to encrypt/decrypt unicast 802.11 frames, and the ___________ key is used to encrypt/decrypt broadcast and multicast 802.11 frames.
- A . Group Master, Group Temporal
- B . Pairwise Master, Group Temporal
- C . Master Session, Pairwise Transient
- D . Pairwise Transient, Group Temporal
- E . Pairwise Master, Pairwise Transient
3DES has effective key sizes of how many bits? (Choose all that apply.)
- A . 56
- B . 64
- C . 112
- D . 128
- E . 168
- F . 192
Chris has been hired as a consultant to secure the Harkins Corporation’s WLAN infrastructure. Management has asked him to choose a WLAN authentication solution that will best protect the company’s network resources from unauthorized users.
The company is also looking for a strong dynamic encryption solution for data privacy reasons. Management is also looking for the cheapest solution as well as a solution that is easy to administer.
Which of these WLAN security solutions does Chris decide meets all of the objectives required by management? (Choose the best answer.)
- A . EAP-TLS and TKIP/RC4 encryption
- B . EAP-TLS and CCMP/AES encryption
- C . EAP-PEAPv0 (MSCHAPv2) and CCMP/AES encryption
- D . EAP-PEAPv0 (EAP-TLS) and CCMP/AES encryption
- E . EAP-FAST/manual provisioning and CCMP/AES encryption
- F . EAP-MD5 and CCMP/AES encryption
In which of these enterprise RADIUS deployments do the EAP communications not traverse across a WAN link? (Choose all that apply.)
- A . Single-site deployment
- B . Distributed autonomous sites
- C . Distributed sites, centralized RADIUS and LDAP
- D . Distributed sites with RADIUS, centralized LDAP
- E . Distributed sites with RADIUS proxy, centralized RADIUS and LDAP
Which of these attacks would be typically associated with malicious eavesdropping? (Choose all that apply.)
- A . NetStumbler
- B . Peer-to-peer
- C . Protocol analyzer capture
- D . Packet reconstruction
- E . PS polling attack
