Practice Free CWSP-207 Exam Online Questions
What are the keys that make up a pairwise transient key? (Choose all that apply.)
- A . STK
- B . KEK
- C . SMK
- D . TK
- E . KCK
Which of these types of EAP do not use tunneled authentication? (Choose all that apply.)
- A . EAP-LEAP
- B . EAP-PEAPv0 (EAP-MSCHAPv2)
- C . EAP-PEAPv1 (EAP-GTC)
- D . EAP-FAST
- E . EAP-TLS (normal mode)
- F . EAP-MD5
In an effort to optimize WLAN performance, ABC Company has upgraded their WLAN infrastructure from 802.11a/g to 802.11n. 802.11a/g clients are still supported and are used throughout ABC’s facility.
ABC has always been highly security conscious, but due to budget limitations, they have not yet updated their overlay WIPS solution to 802.11n or 802.11ac.
Given ABC’s deployment strategy, what security risks would not be detected by the 802.11a/g WIPS?
- A . Hijacking attack performed by using a rogue 802.11n AP against an 802.11a client
- B . Rogue AP operating in Greenfield 40 MHz-only mode
- C . 802.11a STA performing a deauthentication attack against 802.11n APs
- D . 802.11n client spoofing the MAC address of an authorized 802.11n client
What is the difference between the inner and outer identity?
- A . Only the authentication server provides its credentials in the outer identity response.
- B . The inner identity is only for authentication server credentials provided to the supplicant.
- C . The inner identity must correspond to the outer identity for realm-based authentications.
- D . The outer identity is in plain text; the inner identity is securely transmitted inside a TLS tunnel.
- E . The outer identity is only for authentication server credentials provided to the supplicant.
What type of WLAN attacks might be detected by a distributed WIDS/WIPS solution using a signature analysis software engine? (Choose all that apply.)
- A . PS-Poll flood
- B . Deauthentication attack
- C . Protocol fuzzing
- D . Virtual carrier attack
- E . CTS flood attack
- F . Zero day attack
When RSN security is in place, which security handshake is used to distribute keys to encrypt broadcast/multicast traffic even though a previous security association has already occurred?
- A . Peer Key Handshake
- B . Group Key Handshake
- C . 4-Way Handshake
- D . 2-Way Handshake
Given: The Aircrack-ng WLAN software tool can capture and transmit modified 802.11 frames over the wireless network. It comes pre-installed on Kali Linux and some other Linux distributions.
What are three uses for such a tool? (Choose 3)
- A . Transmitting a deauthentication frame to disconnect a user from the AP.
- B . Auditing the configuration and functionality of a WIPS by simulating common attack sequences
- C . Probing the RADIUS server and authenticator to expose the RADIUS shared secret
- D . Cracking the authentication or encryption processes implemented poorly in some WLANs
After viewing this graphic, determine which type of WLAN attack tool could be used to create this Layer 1 denial of service to the WLAN.
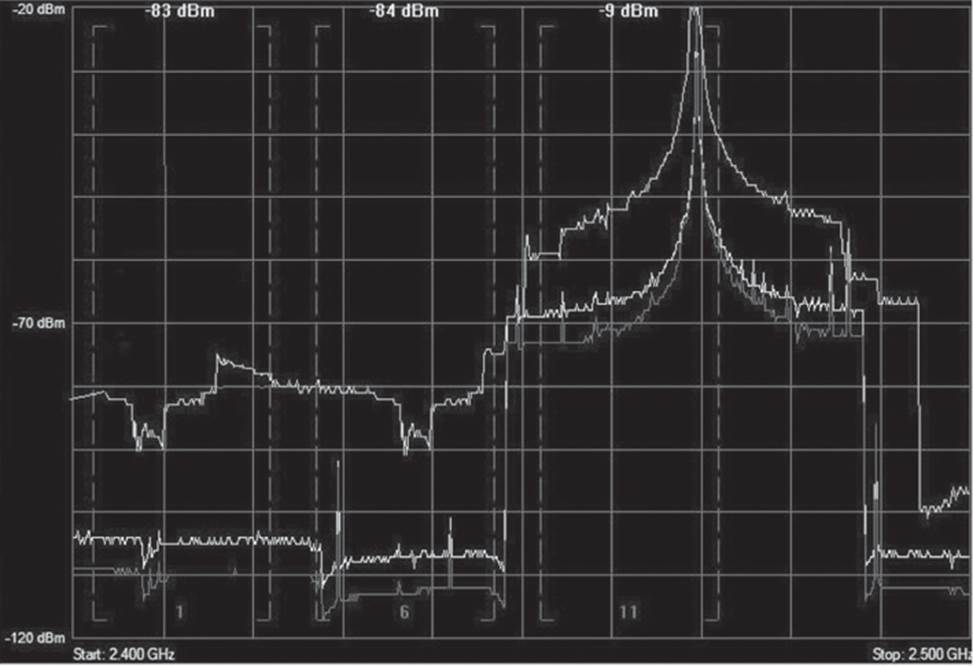
- A . All-band hopping jammer
- B . Wide-band jammer
- C . Narrow-band jammer
- D . Queensland software utility
- E . Packet generator
What statements are true about 802.11-2012 Protected Management Frames? (Choose 2)
- A . 802.11w frame protection protects against some Layer 2 denial-of-service (DoS) attacks, but it cannot prevent all types of Layer 2 DoS attacks.
- B . When frame protection is in use, the PHY preamble and header as well as the MAC header are encrypted with 256- or 512-bit AES.
- C . Authentication, association, and acknowledgment frames are protected if management frame protection is enabled, but deauthentication and disassociation frames are not.
- D . Management frame protection protects disassociation and deauthentication frames.
What is some of the operation information that an 802.11k-2008Ccompliant client station may receive in the neighbor report from an 802.11k-2008Ccompliant access point (AP)? (Choose all that apply.)
- A . BSSID of neighbor AP
- B . PHY types supported by neighbor AP
- C . APSD support of neighbor AP
- D . Channel number of neighbor AP
- E . All of the above
