Practice Free CWSP-207 Exam Online Questions
The corporate IT administrators, Hunter, Rion, and Liam, are huddled together to try to solve an issue with the newly deployed VoWiFi phones. The chosen security solution is PEAPv0 (EAP-MSCHAPv2) for the voice SSID that also has Voice Enterprise enabled on the access points.
The VoWiFi phones are authenticating flawlessly and voice calls are stable when the employees use the devices from their desk. However, there seem to be gaps in the audio and sometimes disconnects when the employees are talking on the VoWiFi phones and move to other areas of the building.
What are the possible causes of the interruption of service for the voice calls while the employees are mobile? (Choose all that apply.)
- A . VoWiFi phones should only be configured for PSK authentication when roaming is a requirement.
- B . VoWiFi phones are reauthenticating every time they roam to a new AP.
- C . VoWiFi phones do not use opportunistic key caching.
- D . VoWiFi phones do not support fast BSS transition.
Which of the following is a self-service process for an employee to provision a BYOD device to connect to the secure corporate network?
- A . Captive Portal
- B . 802.1X/EAP Configurator
- C . MDM
- D . Over-the-air management
- E . Onboarding
Kenny has been tasked with designing an 802.1X/EAP solution for the corporate WLAN. The company headquarters and datacenter reside in London.
Employees need secure WLAN access at 15 remote offices in other European cities. Kenny needs a solution that is cost-efficient but should provide secure WLAN connectivity for the majority of users if a remote WAN link goes down.
Which of these RADIUS deployment models best meets his requirements? (Choose the best answer.)
- A . Single-site deployment
- B . Distributed autonomous sites
- C . Distributed sites, centralized RADIUS and LDAP
- D . Distributed sites with RADIUS, centralized LDAP
- E . Distributed sites with RADIUS proxy, centralized RADIUS and LDAP
What mechanism can be used if the guest VLAN is not supported at the edge of the network and only resides in a DMZ?
- A . GRE
- B . VPN
- C . STP
- D . RTSP
- E . IGMP
Name two types of rogue devices that cannot be detected by a Layer 2 wireless intrusion prevention system (WIPS).
- A . 900 MHz radio
- B . 802.11h-compliant device
- C . FHSS radio
- D . 802.11b routers
- E . 802.11g mixed-mode device
In a guest firewall policy, which IP networks should be restricted? (Choose two.)
- A . 172.16.0.0/12
- B . 20.0.0.0/8
- C . 192.16.0.0/16
- D . 172.10.0.0/24
- E . 10.0.0.0/8
168.80.5/24
User VLANS:
VLAN 201
VLAN 202
VLAN 203
SSIDs:
SSID-1: (employee) security: (802.1X/EAP/CCMP) – VLAN 201 – BSSID (00:08:12:43:0F:30)
SSID-2 (voice) security: (PSK/TKIP and WEP) – VLAN 202 – BSSID (00:08:12:43:0F:31)
SSID-3: (guest) security: (WEP) – VLAN 203 – BSSID (00:08:12:43:0F:32)
Based on the settings on Bob’s access point, what type of WLAN security exits within the coverage area of the AP? (Choose all that apply.)
- A . Closed security network
- B . Transition security network
- C . Pre-RSNA security network
- D . Open security network
- E . Robust security network
When two client stations are already associated to an AP, which handshake is used to create a different unicast key that the two client stations can use for a private conversation while they remain associated to the AP?
- A . Mesh Group Key Handshake
- B . Group Key Handshake
- C . 4-Way Handshake
- D . 2-Way Handshake
- E . TDLS Peer Key Handshake
Which of the following protocols is designed to provide more secure encryption than the weak wired encryption privacy?
- A . LEAP
- B . TKIP
- C . PEAP
- D . CCMP
After viewing the frame capture in the graphic shown here, identify which type of security network is being used.
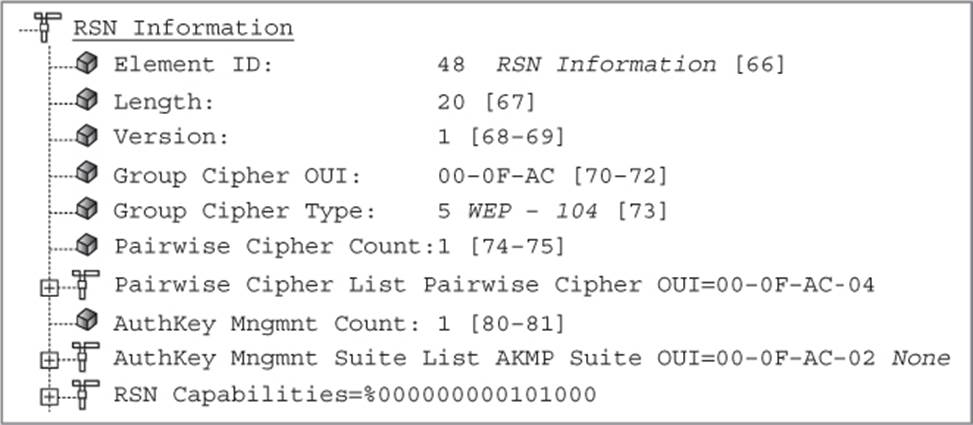
- A . Robust security network
- B . Rotund security network
- C . Transition security network
- D . WPA security network
