Practice Free CWSP-207 Exam Online Questions
After viewing the image shown here, what type of credentials can be strengthened with the software application that is depicted? (Choose all that apply.)

- A . Passwords
- B . Shared secrets
- C . Passphrases
- D . Pairwise master keys
- E . Pairwise transient keys
- F . Group temporal keys
For a WIPS system to identify the location of a rogue WLAN device using location patterning (RF fingerprinting), what must be done as part of the WIPS installation?
- A . All WIPS sensors must be installed as dual-purpose (AP/sensor) devices.
- B . A location chipset (GPS) must be installed with it.
- C . At least six antennas must be installed in each sensor.
- D . The RF environment must be sampled during an RF calibration process.
After viewing the frame capture in the graphic shown here, identify which type of encryption method is being used.
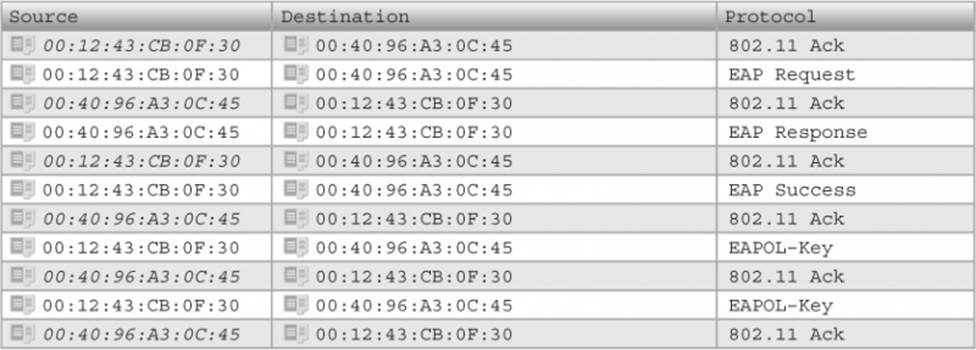
- A . TKIP
- B . CCMP
- C . xSec
- D . Fortress
- E . WEP
- F . AES
Given: WLAN protocol analyzers can read and record many wireless frame parameters.
What parameter is needed to physically locate rogue APs with a protocol analyzer?
- A . SSID
- B . IP Address
- C . BSSID
- D . Signal strength
- E . RSN IE
- F . Noise floor
Wireless Intrusion Prevention Systems (WIPS) are used for what purposes? (Choose 3)
- A . Performance monitoring and troubleshooting
- B . Enforcing wireless network security policy
- C . Detecting and defending against eavesdropping attacks
- D . Security monitoring and notification
- E . Preventing physical carrier sense attacks
- F . Classifying wired client devices
Wireless Intrusion Prevention Systems (WIPS) are used for what purposes? (Choose 3)
- A . Performance monitoring and troubleshooting
- B . Enforcing wireless network security policy
- C . Detecting and defending against eavesdropping attacks
- D . Security monitoring and notification
- E . Preventing physical carrier sense attacks
- F . Classifying wired client devices
Given: One of the security risks introduced by WPA2-Personal is an attack conducted by an authorized network user who knows the passphrase. In order to decrypt other users’ traffic, the attacker must obtain certain information from the 4-way handshake of the other users.
In addition to knowing the Pairwise Master Key (PMK) and the supplicant’s address (SA), what other three inputs must be collected with a protocol analyzer to recreate encryption keys? (Choose 3)
- A . Authenticator nonce
- B . Supplicant nonce
- C . Authenticator address (BSSID)
- D . GTKSA
- E . Authentication Server nonce
What is the main purpose of using a WLAN protocol analyzer during the Layer 2 analysis of a WLAN security audit? (Choose all that apply.)
- A . Identifying unauthorized devices
- B . Auditing the wired infrastructure
- C . Performing penetration testing
- D . Validating security compliance of authorized devices
- E . Auditing the WIPS
Given: Many corporations configure guest VLANs on their WLAN controllers that allow visitors to have Internet access only. The guest traffic is tunneled to the DMZ to prevent some security risks.
In this deployment, what risks are still associated with implementing the guest VLAN without any advanced traffic monitoring or filtering features enabled? (Choose 2)
- A . Intruders can send spam to the Internet through the guest VLAN.
- B . Peer-to-peer attacks can still be conducted between guest users unless application-layer monitoring and filtering are implemented.
- C . Unauthorized users can perform Internet-based network attacks through the WLAN.
- D . Guest users can reconfigure AP radios servicing the guest VLAN unless unsecure network management protocols (e.g. Telnet, HTTP) are blocked.
- E . Once guest users are associated to the WLAN, they can capture 802.11 frames from the corporate VLANs.
What are some of the methods used by WIPS vendors to determine if a rogue device is connected to the wired network infrastructure? (Choose all that apply.)
- A . TTL packet analysis
- B . RF triangulation
- C . Signature analysis
- D . Behavioral analysis
- E . MAC table analysis
- F . Proprietary analysis
