Practice Free CWSP-207 Exam Online Questions
Given: You are installing 6 APs on the outside of your facility. They will be mounted at a height of 6 feet.
What must you do to implement these APs in a secure manner beyond the normal indoor AP implementations? (Choose the single best answer.)
- A . User external antennas.
- B . Use internal antennas.
- C . Power the APs using PoE.
- D . Ensure proper physical and environmental security using outdoor ruggedized APs or enclosures.
Which of these methods allows an authenticator and supplicant to skip an entire 802.1X/EAP authentication and proceed with the traditional 4-Way Handshake? (Choose all that apply.)
- A . PMK caching
- B . PTK caching
- C . Opportunistic key caching
- D . Fast BSS transition
What is a primary criteria for a network to qualify as a Robust Security Network (RSN)?
- A . Token cards must be used for authentication.
- B . Dynamic WEP-104 encryption must be enabled.
- C . WEP may not be used for encryption.
- D . WPA-Personal must be supported for authentication and encryption.
- E . WLAN controllers and APs must not support SSHv1.
What security can be used to stop attackers from seeing the MAC addresses used by your legitimate 802.11 WLAN devices?
- A . MAC spoofing
- B . VPN tunneling
- C . CCMP/AES encryption
- D . Use 802.1X authentication
- E . None of the above
You have been tasked with configuring a secure WLAN for 400 APs at the corporate offices. All the APs and employee Windows laptops have been configured for 802.1X using EAP-MSCHAPv2. The domain user accounts are failing authentication with every attempt.
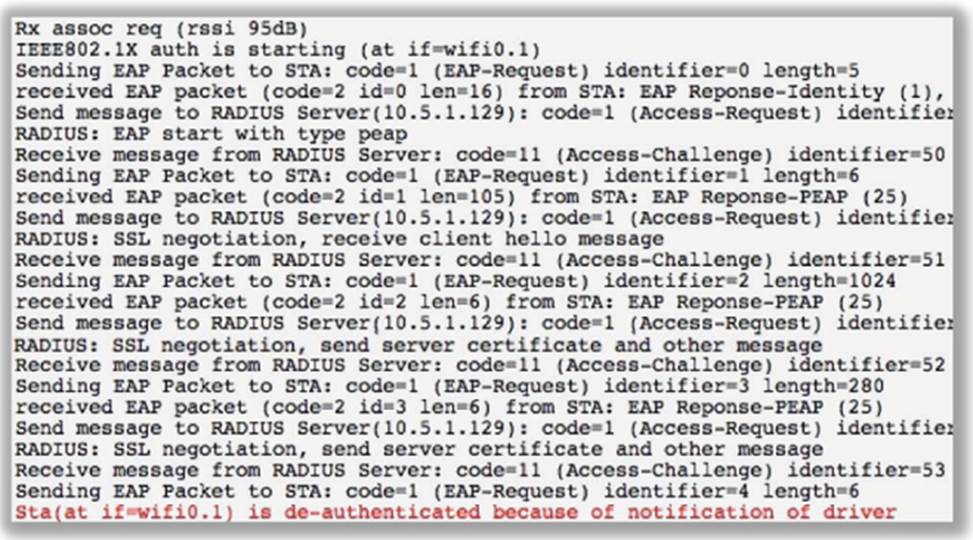
After viewing the graphic shown here, determine the possible causes of the problem. (Choose all that apply.)
- A . The networking settings on the AP are incorrect.
- B . The Windows OS laptops’ supplicant has been configured for machine authentication.
- C . The supplicant clock settings are incorrect.
- D . An authentication port mismatch exists between the AP and the RADIUS server.
- E . The networking settings on the RADIUS server are incorrect.
- F . The incorrect root certificate is selected in the supplicant.
Which of these WLAN architectures may require the use of an NMS server to manage and monitor the WLAN?
- A . Autonomous WLAN architecture
- B . Centralized WLAN architecture
- C . Distributed WLAN architecture
- D . All of the above
Which of the following provides the best protection against a man-in-the-middle attack?
- A . Strong encryption
- B . Firewall
- C . Strong password
- D . Fiber-optic cable
As the head of network security for your organization, you discover an unauthorized access point plugged into your network.
Upon investigation, the person who placed the rogue AP on your network is determined to be one of your own users, not an attacker. You wish to proceed with appropriate disciplinary measures but are not allowed to do so by the Human Resources department.
What is the most likely reason that the HR staff would not allow disciplinary measures to be taken?
- A . There is no written policy preventing users from adding their own APs to the network.
- B . The user who placed the AP is a member of management.
- C . The user who placed the AP is a member of the union.
- D . You are not the user’s direct supervisor and cannot discipline the user.
- E . No data was lost or altered as a result of the rogue device placement.
Which of the following is not a standard or amendment created by the IEEE? (Choose all that apply.)
- A . 802.11X
- B . 802.1x
- C . 802.3af
- D . 802.11N
- E . 802.11g
When using an encryption suite that implements an asymmetric algorithm, which of the following statements is true? (Choose all that apply.)
- A . Both the encrypting and decrypting parties share the same key.
- B . Asymmetric algorithms generally are faster than symmetric algorithms.
- C . Asymmetric algorithms generally are slower than symmetric algorithms.
- D . Public and private encryption keys must be generated.
