Practice Free CS0-003 Exam Online Questions
After conducting a cybersecurity risk assessment for a new software request, a Chief Information Security Officer (CISO) decided the risk score would be too high. The CISO refused the software request.
Which of the following risk management principles did the CISO select?
- A . Avoid
- B . Transfer
- C . Accept
- D . Mitigate
While reviewing system logs, a network administrator discovers the following entry:
![]()
Which of the following occurred?
- A . An attempt was made to access a remote workstation.
- B . The PsExec services failed to execute.
- C . A remote shell failed to open.
- D . A user was trying to download a password file from a remote system.
An analyst is reviewing a vulnerability report for a server environment with the following entries:

Which of the following systems should be prioritized for patching first?
- A . 10.101.27.98
- B . 54.73.225.17
- C . 54.74.110.26
- D . 54.74.110.228
During an incident, an analyst needs to acquire evidence for later investigation.
Which of the following must be collected first in a computer system, related to its volatility level?
- A . Disk contents
- B . Backup data
- C . Temporary files
- D . Running processes
When starting an investigation, which of the following must be done first?
- A . Notify law enforcement
- B . Secure the scene
- C . Seize all related evidence
- D . Interview the witnesses
A security analyst is reviewing a packet capture in Wireshark that contains an FTP session from a potentially compromised machine. The analyst sets the following display filter: ftp. The analyst can see there are several RETR requests with 226 Transfer complete responses, but the packet list pane is not showing the packets containing the file transfer itself.
Which of the following can the analyst perform to see the entire contents of the downloaded files?
- A . Change the display filter to f cp. accive. pore
- B . Change the display filter to tcg.port=20
- C . Change the display filter to f cp-daca and follow the TCP streams
- D . Navigate to the File menu and select FTP from the Export objects option
While reviewing a vulnerability assessment, an analyst notices the following issue is identified in the report:

this finding, which of the following would be most appropriate for the analyst to recommend to the network engineer?
- A . Reconfigure the device to support only connections leveraging TLSv1.2.
- B . Obtain a new self-signed certificate and select AES as the hashing algorithm.
- C . Replace the existing certificate with a certificate that uses only MD5 for signing.
- D . Use only signed certificates with cryptographically secure certificate sources.
Which of the following items should be included in a vulnerability scan report? (Choose two.)
- A . Lessons learned
- B . Service-level agreement
- C . Playbook
- D . Affected hosts
- E . Risk score
- F . Education plan
The steering committee for information security management annually reviews the security incident register for the organization to look for trends and systematic issues. The steering committee wants to rank the risks based on past incidents to improve the security program for next year.
Below is the incident register for the organization:
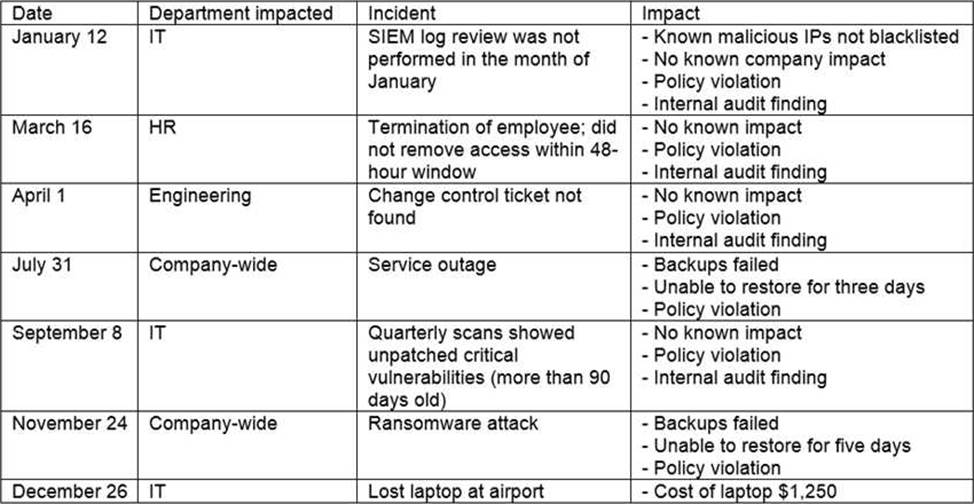
Which of the following should the organization consider investing in first due to the potential impact of availability?
- A . Hire a managed service provider to help with vulnerability management.
- B . Build a warm site in case of system outages.
- C . Invest in a failover and redundant system, as necessary.
- D . Hire additional staff for the IT department to assist with vulnerability management and log review.
A security analyst is writing a shell script to identify IP addresses from the same country.
Which of the following functions would help the analyst achieve the objective?
- A . function w() { info=$(ping -c 1 $1 | awk -F “/” ‘END{print $1}’) && echo “$1 | $info” }
- B . function x() { info=$(geoiplookup $1) && echo “$1 | $info” }
- C . function y() { info=$(dig -x $1 | grep PTR | tail -n 1 ) && echo “$1 | $info” }
- D . function z() { info=$(traceroute -m 40 $1 | awk ‘END{print $1}’) && echo “$1 | $info” }
