Practice Free AZ-500 Exam Online Questions
You are troubleshooting a security issue for an Azure Storage account You enable Azure Storage Analytics logs and archive It to a storage account.
What should you use to retrieve the diagnostics logs?
- A . Azure Storage Explorer
- B . SQL query editor in Azure
- C . Azure Monitor
- D . Azure Cosmos DB explorer
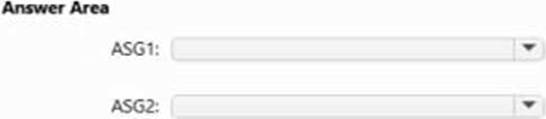
You have an Azure subscription that contains the virtual machines shown in the following table.
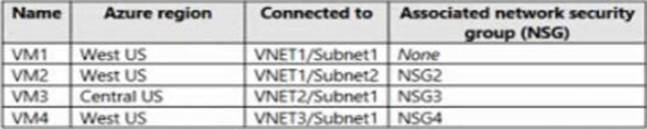
VNET1, VNET2, and VNET3 are peered with each other.
You perform the following actions:
* Create two application security groups named ASG1 and ASG2 in the West US region.
* Add the network interface of VM1 to ASG1.
You have an Azure subscription that uses Microsoft Sentinel.
You need to create a Microsoft Sentinel notebook that will use the Guided Investigation – Anomaly Lookup template.
What should you create first?
- A . an analytics rule
- B . a Log Analytics workspace
- C . an Azure Machine Learning workspace
- D . a hunting query
You have a hybrid configuration of Azure Active Directory (Azure AD). You have an Azure SQL Database instance that is configured to support Azure AD authentication.
Database developers must connect to the database instance and authenticate by using their on-premises Active Directory account.
You need to ensure that developers can connect to the instance by using Microsoft SQL Server Management
Studio. The solution must minimize authentication prompts.
Which authentication method should you recommend?
- A . Active Directory – Password
- B . Active Directory – Universal with MFA support
- C . SQL Server Authentication
- D . Active Directory – Integrated
D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sql-database/sql-database-aad-authentication-configure
Your company plans to create separate subscriptions for each department. Each subscription will be
associated to the same Azure Active Directory (Azure AD) tenant.
You need to configure each subscription to have the same role assignments.
What should you use?
- A . Azure Security Center
- B . Azure Policy
- C . Azure AD Privileged Identity Management (PIM)
- D . Azure Blueprints
D
Explanation:
Just as a blueprint allows an engineer or an architect to sketch a project’s design parameters, Azure Blueprints enables cloud architects and central information technology groups to define a repeatable set of Azure resources that implements and adheres to an organization’s standards, patterns, and requirements.
Blueprints are a declarative way to orchestrate the deployment of various resource templates and other artifacts such as:
Role Assignments
Policy Assignments
Azure Resource Manager templates
Resource Groups
Reference: https://docs.microsoft.com/en-us/azure/governance/blueprints/overview
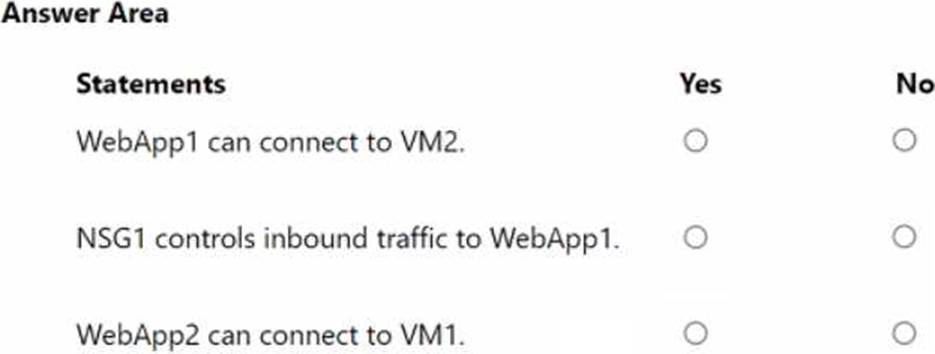
HOTSPOT
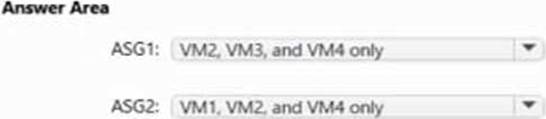
You have an Azure subscription that contains the virtual networks shown in the following table.
NSG1 and NSG2 both have default rules only.
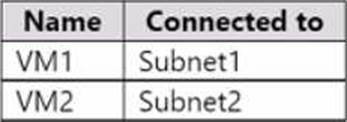
The subscription contains the virtual machines shown in the following table.
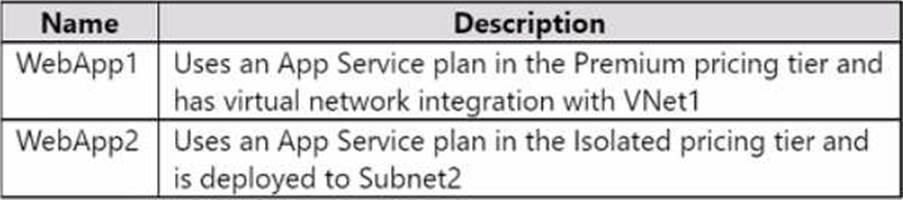
The subscription contains the web apps shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.

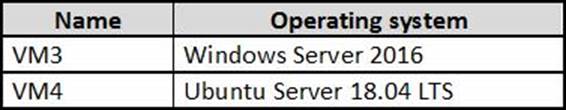
You have an Azure subscription that contains the virtual machines shown in the following table.
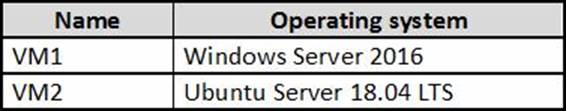
From Azure Security Center, you turn on Auto Provisioning.
You deploy the virtual machines shown in the following table.
On which virtual machines is the Log Analytics agent installed?
- A . VM3 only
- B . VM1 and VM3 only
- C . VM3 and VM4 only
- D . VM1, VM2, VM3, and VM4
D
Explanation:
When automatic provisioning is On, Security Center provisions the Log Analytics Agent on all supported Azure VMs and any new ones that are created.
Supported Operating systems include: Ubuntu 14.04 LTS (x86/x64), 16.04 LTS (x86/x64), and 18.04 LTS (x64) and Windows Server 2008 R2, 2012, 2012 R2, 2016, version 1709 and 1803
Reference: https://docs.microsoft.com/en-us/azure/security-center/security-center-enable-data-collection
You have an Azure subscription that contains a user named Adminl1 and a virtual machine named VM1. VM1 runs Windows Server 2019 and was deployed by using an Azure Resource Manager template. VM1 is the member of a backend pool of a public Azure Basic Load Balancer.
Admin1 reports that VM1 is listed as Unsupported on the Just in time VM access blade of Azure Security Center.
You need to ensure that Admin1 can enable just in time (JIT) VM access for VM1.
What should you do?
- A . Create and configure an additional public IP address for VM 1.
- B . Replace the Basic Load Balancer with an Azure Standard Load Balancer.
- C . Assign an Azure Active Directory Premium Plan 1 license to Admin1.
- D . Create and configure a network security group (NSG).
D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/security-center/security-center-just-in-time?tabs=jit-config-asc%2Cjit-request-asc
HOTSPOT
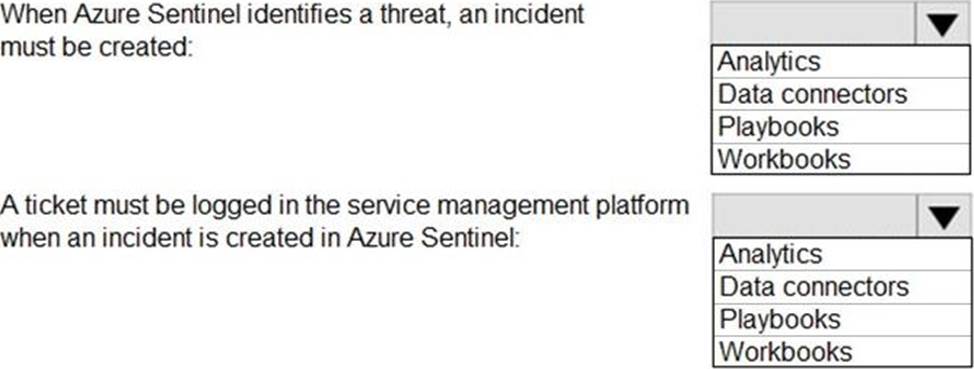
You have an Azure subscription that contains an Azure Sentinel workspace.
Azure Sentinel is configured to ingest logs from several Azure workloads. A third-party service management platform is used to manage incidents.
You need to identify which Azure Sentinel components to configure to meet the following requirements:
When Azure Sentinel identifies a threat, an incident must be created.
A ticket must be logged in the service management platform when an incident is created in Azure Sentinel.
Which component should you identify for each requirement? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
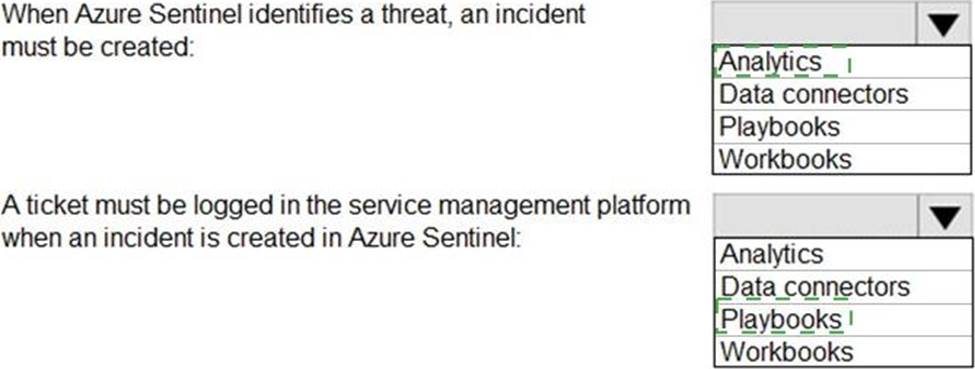
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/create-incidents-from-alerts
https://docs.microsoft.com/en-us/azure/sentinel/tutorial-respond-threats-playbook
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have accounts for the following cloud services:
• Alibaba Cloud
• Amazon Web Services (AWS)
• Google Cloud Platform (GCP)
What can you add to Defender for Cloud?
- A . AWS only
- B . Alibaba Cloud and AWS only
- C . Alibaba Good and GCP only
- D . AWS and GCP only
- E . Alibaba Cloud, AWS. and GCP
