Practice Free AZ-500 Exam Online Questions
You have a Azure subscription.
You enable Azure Active Directory (Azure AD) Privileged identify (PIM).
Your company’s security policy for administrator accounts has the following conditions:
* The accounts must use multi-factor authentication (MFA).
* The account must use 20-character complex passwords.
* The passwords must be changed every 180 days.
* The account must be managed by using PIM.
You receive alerts about administrator who have not changed their password during the last 90 days.
You need to minimize the number of generated alerts.
Which PIM alert should you modify?
- A . Roles don’t require multi-factor authentication for activation.
- B . Administrator aren’t using their privileged roles
- C . Roles are being assigned outside of Privileged identity Management
- D . Potential state accounts in a privileged role.
D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/privileged-identity-management/pim-how-to-configure-security-alerts?tabs=new
Note: The question is included in a number of questions that depicts the identical set-up. However, every question has a distinctive result. Establish if the solution satisfies the requirements.
Your company has an Active Directory forest with a single domain, named weylandindustries.com.
They also have an Azure Active Directory (Azure AD) tenant with the same name.
You have been tasked with integrating Active Directory and the Azure AD tenant. You intend to deploy Azure AD Connect.
Your strategy for the integration must make sure that password policies and user logon limitations affect user accounts that are synced to the Azure AD tenant, and that the amount of necessary servers are reduced.
Solution: You recommend the use of pass-through authentication and seamless SSO with password hash synchronization.
Does the solution meet the goal?
- A . Yes
- B . No
A
Explanation:
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/choose-ad-authn
HOTSPOT
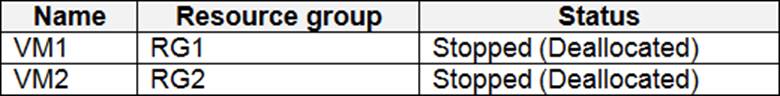
You have an Azure subscription that contains the virtual machines shown in the following table.
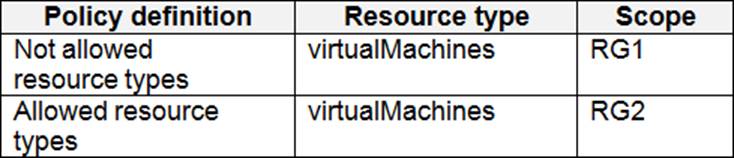
You create the Azure policies shown in the following table.
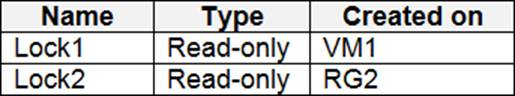
You create the resource locks shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
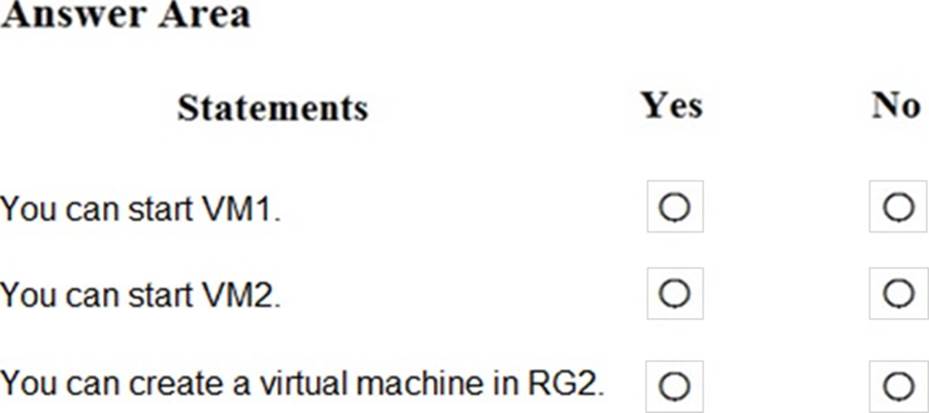
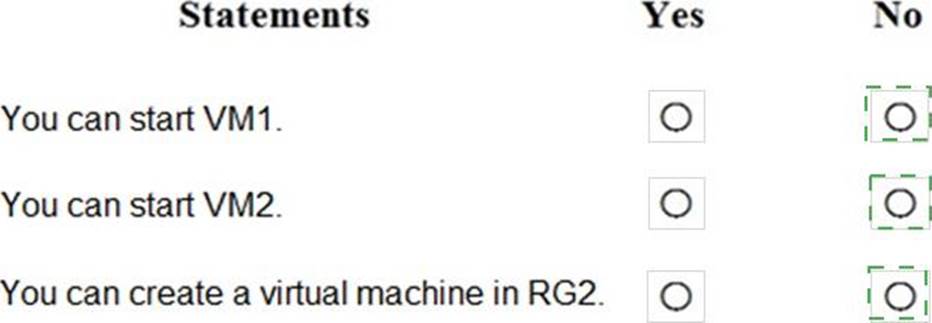
Explanation:
NO
NO
NO
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create an initiative and an assignment that is scoped to the Tenant Root Group management group.
Does this meet the goal?
- A . Yes
- B . No
A
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/governance/policy/overview
https://4sysops.com/archives/apply-governance-policy-to-multiple-azure-subscriptions-with-management-groups/
You have a web app hosted on an on-premises server that is accessed by using a URL of https://www.contoso.com. You plan to migrate the web app to Azure. You will continue to use https://www.contoso.com. You need to enable HTTPS for the Azure web app.
What should you do first?
- A . Export the public key from the on-premises server and save the key as a P7b file.
- B . Export the private key from the on-premises server and save the key as a PFX file that is encrypted by using TripleDES.
- C . Export the public key from the on-premises server and save the key as a CER file.
- D . Export the private key from the on-premises server and save the key as a PFX file that is encrypted by using AES256.
B
Explanation:
https://docs.microsoft.com/en-us/azure/app-service/configure-ssl-certificate#private-certificate-requirements
You have an on-premises network and an Azure subscription.
You have the Microsoft SQL Server instances shown in the following table.
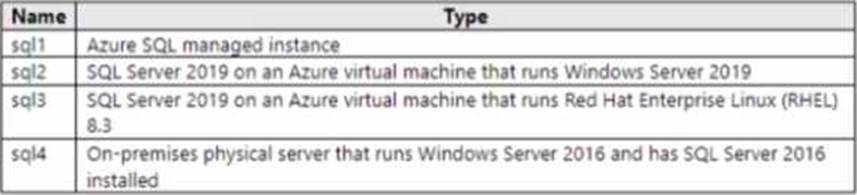
You plan to implement Microsoft Defender for SQL.
Which SQL Server instances will be protected by Microsoft Defender for SQL?
- A . sql1 and sql2 only
- B . sql1, sql2, andsql3 only
- C . sql1 sql2 and so.14 only
- D . sql1, sql2, sql3, and sql4
You have an on-premises network and an Azure subscription.
You have the Microsoft SQL Server instances shown in the following table.
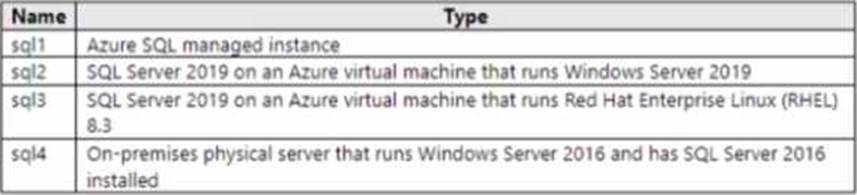
You plan to implement Microsoft Defender for SQL.
Which SQL Server instances will be protected by Microsoft Defender for SQL?
- A . sql1 and sql2 only
- B . sql1, sql2, andsql3 only
- C . sql1 sql2 and so.14 only
- D . sql1, sql2, sql3, and sql4
You are configuring and securing a network environment.
You deploy an Azure virtual machine named VM1 that is configured to analyze network traffic.
You need to ensure that all network traffic is routed through VM1.
What should you configure?
- A . a system route
- B . a network security group (NSG)
- C . a user-defined route
C
Explanation:
Although the use of system routes facilitates traffic automatically for your deployment, there are cases in which you want to control the routing of packets through a virtual appliance. You can do so by creating user defined routes that specify the next hop for packets flowing to a specific subnet to go to your virtual appliance instead, and enabling IP forwarding for the VM running as the virtual appliance.
Note: User Defined Routes
For most environments you will only need the system routes already defined by Azure. However, you may need to create a route table and add one or more routes in specific cases, such as:
Force tunneling to the Internet via your on-premises network.
Use of virtual appliances in your Azure environment.
In the scenarios above, you will have to create a route table and add user defined routes to it.
Reference: https://github.com/uglide/azure-content/blob/master/articles/virtual-network/virtual-networks-udr-overview.md
HOTSPOT
You have an Azure subscription that contains a user named User1. User1 is assigned the Reader role for the subscription.
You plan to create a custom role named Role1 and assign Role1 to User1.
You need to ensure that User1 can create and manage application security groups by using the Azure portal.
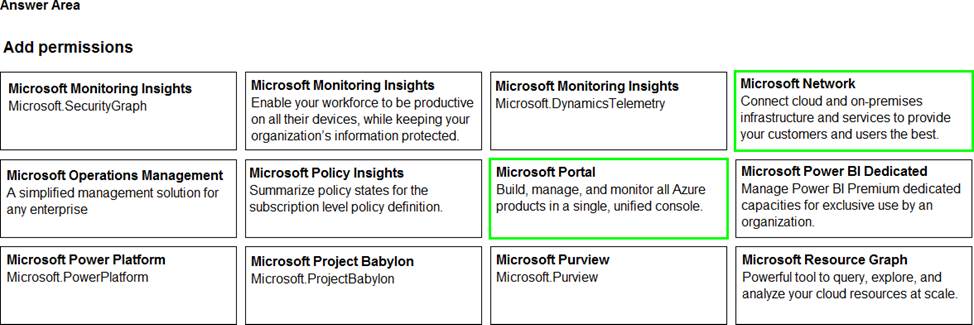
Which two permissions should you add to Role1? To answer, select the appropriate permission in the answer area. NOTE: Each correct selection is worth one point.
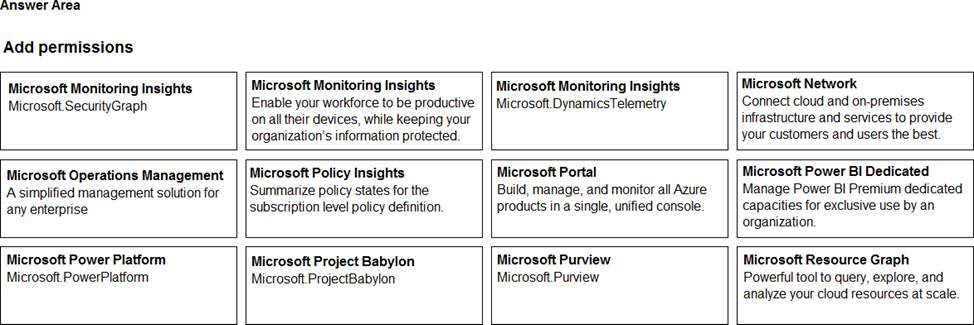
Explanation:
You have an Azure subscription named Sub1 that contains an Azure Log Analytics workspace named LAW1.
You have 100 on-premises servers that run Windows Server 2012 R2 and Windows Server 2016. The servers connect to LAW1. LAW1 is configured to collect security-related performance counters from the connected servers.
You need to configure alerts based on the data collected by LAW1.
The solution must meet the following requirements:
– Alert rules must support dimensions.
– The time it takes to generate an alert must be minimized.
– Alert notifications must be generated only once when the alert is generated and once when the alert is
– resolved.
Which signal type should you use when you create the alert rules?
- A . Log
- B . Log (Saved Query)
- C . Metric
- D . Activity Log
C
Explanation:
Metric alerts in Azure Monitor provide a way to get notified when one of your metrics cross a threshold. Metric alerts work on a range of multi-dimensional platform metrics, custom metrics, Application Insights standard and custom metrics.
Note: Signals are emitted by the target resource and can be of several types. Metric, Activity log, Application Insights, and Log.
Reference: https://docs.microsoft.com/en-us/azure/azure-monitor/platform/alerts-metric
