Practice Free AZ-500 Exam Online Questions
You have the Azure virtual machines shown in the following table.
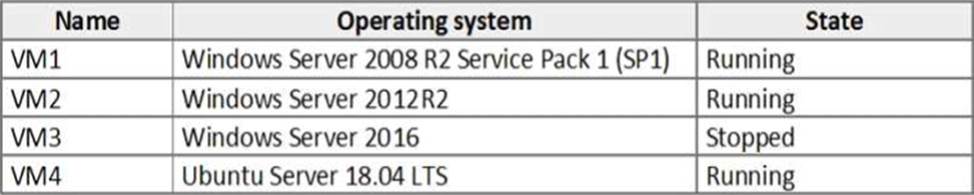
For which virtual machine can you enable Update Management?
- A . VM2 and VM3 only
- B . VM2, VM3, and VM4 only
- C . VM1, VM2, and VM4 only
- D . VM1, VM2, VM3, and VM4
- E . VM1, VM2, and VM3 only
C
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/automation/automation-update-management?toc=%2Fazure%2Fautomation%2Ftoc.json
HOTSPOT
You have an Azure subscription that contains an Azure key vault named Vault1.
On January 1, 2019, Vault1 stores the following secrets.
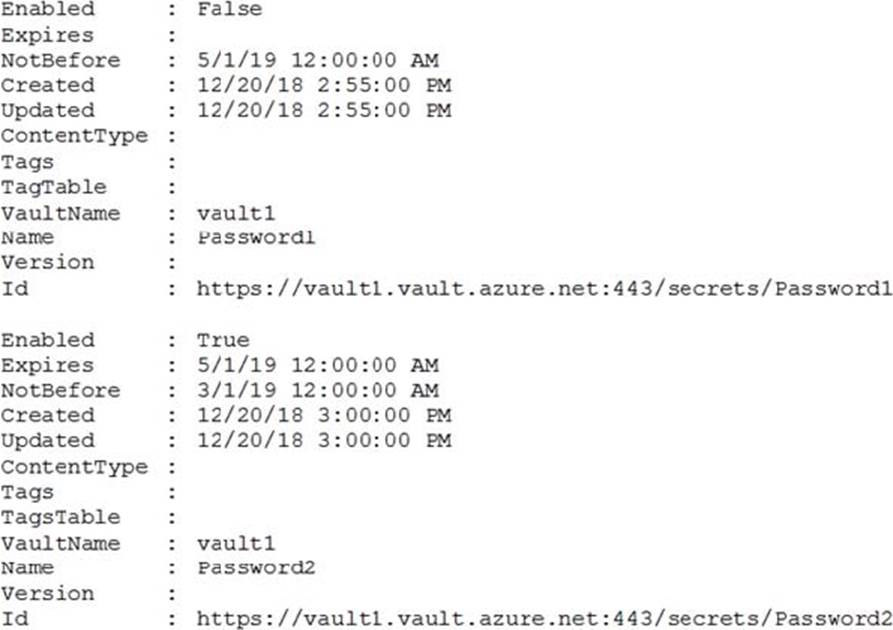
Which can each secret be used by an application? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
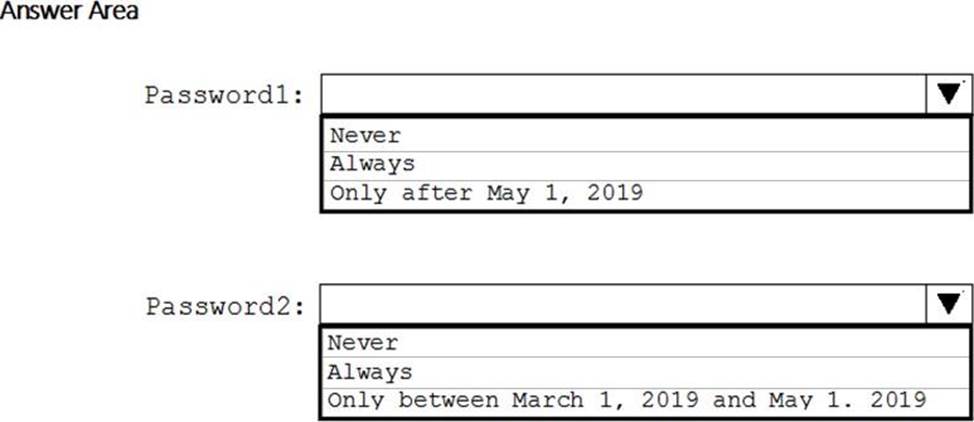
Explanation:
Box 1: Never
Password1 is disabled.
Box 2: Only between March 1, 2019 and May 1,
Password2:
![]()
Reference: https://docs.microsoft.com/en-us/powershell/module/azurerm.keyvault/set-azurekeyvaultsecretattribute
You have an Azure subscription named Subscription1 that contains a resource group named RG1 and the users shown in the following table.
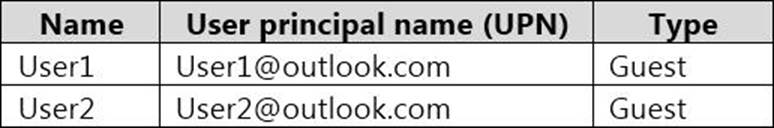
You perform the following tasks:
– Assign User1 the Network Contributor role for Subscription1.
– Assign User2 the Contributor role for RG1.
To Subscription1 and RG1, you assign the following policy definition: External accounts with write permissions should be removed from your subscription.
What is the Compliance State of the policy assignments?
- A . The Compliance State of both policy assignments is Non-compliant.
- B . The Compliance State of the policy assignment to Subscription1 is Compliant, and the Compliance State of the policy assignment to RG1 is Non-compliant.
- C . The Compliance State of the policy assignment to Subscription1 is Non-compliant, and the Compliance State of the policy assignment to RG1 is Compliant.
- D . The Compliance State of both policy assignments is Compliant.
DRAG DROP
You have an Azure subscription that contains 100 virtual machines. Azure Diagnostics is enabled on all the virtual machines.
You are planning the monitoring of Azure services in the subscription.
You need to retrieve the following details:
– Identify the user who deleted a virtual machine three weeks ago.
– Query the security events of a virtual machine that runs Windows Server 2016.
What should you use in Azure Monitor? To answer, drag the appropriate configuration settings to the correct details. Each configuration setting may be used once, more than once, or not at all.
You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
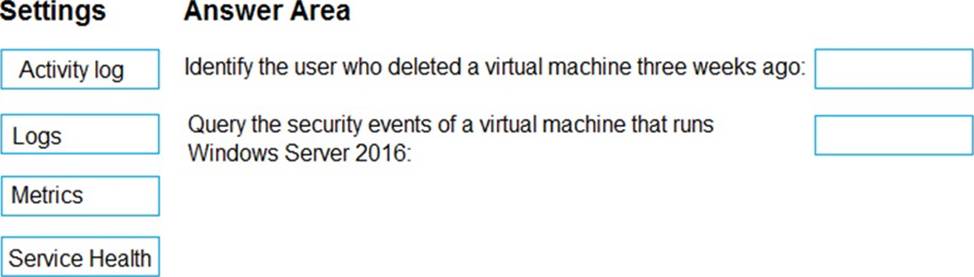
Explanation:
Box1: Activity log
Azure activity logs provide insight into the operations that were performed on resources in your subscription. Activity logs were previously known as “audit logs” or “operational logs,” because they report control-plane events for your subscriptions.
Activity logs help you determine the “what, who, and when” for write operations (that is, PUT, POST, or DELETE).
Box 2: Logs
Log Integration collects Azure diagnostics from your Windows virtual machines, Azure activity logs, Azure Security Center alerts, and Azure resource provider logs. This integration provides a unified dashboard for all your assets, whether they’re on-premises or in the cloud, so that you can aggregate, correlate, analyze, and alert for security events.
Reference: https://docs.microsoft.com/en-us/azure/security/azure-log-audit
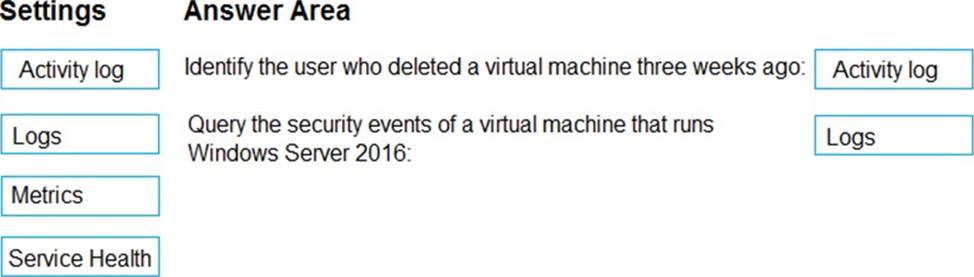
DRAG DROP
You are implementing conditional access policies.
You must evaluate the existing Azure Active Directory (Azure AD) risk events and risk levels to configure and implement the policies.
You need to identify the risk level of the following risk events:
– Users with leaked credentials
– Impossible travel to atypical locations
– Sign ins from IP addresses with suspicious activity
Which level should you identify for each risk event? To answer, drag the appropriate levels to the correct risk events. Each level may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
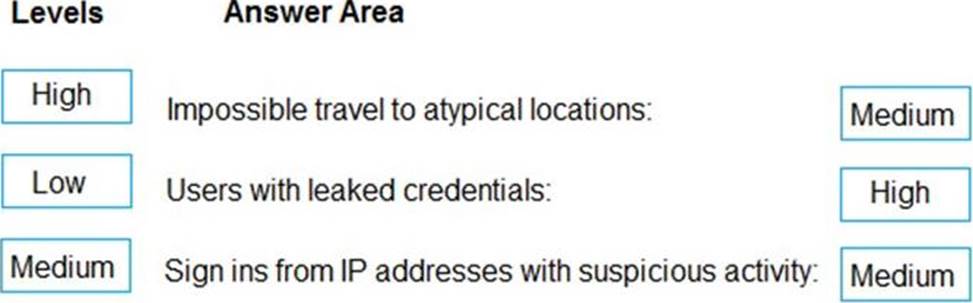
Explanation:
Medium
High
Medium
Refer https://docs.microsoft.com/en-us/azure/active-directory/reports-monitoring/concept-risk-events#sign-ins-from-ip-addresses-with-suspicious-activity
Topic 3, Fabrikam inc
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.
General Overview
Fabrikam, Inc. is a consulting company that has a main office in Montreal and branch offices in Seattle and New York. Fabrikam has IT, human resources (HR), and finance departments.
Existing Environment
Network Environment
Fabrikam has a Microsoft 365 subscription and an Azure subscription named subscription1.
The network contains an on-premises Active Directory domain named Fabrikam.com. The domain contains two organizational units (OUs) named OU1 and OU2. Azure AD Connect cloud sync syncs only OU1.
The Azure resources hierarchy is shown in the following exhibit.

The Azure Active Directory (Azure AD) tenant contains the users shown in the following table.
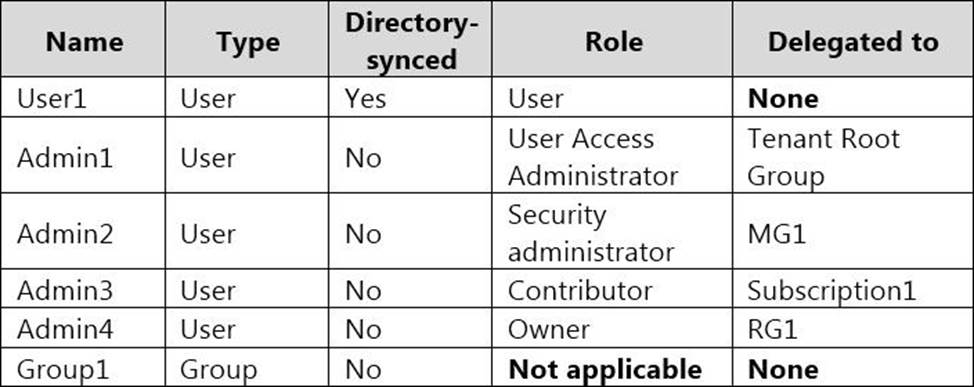
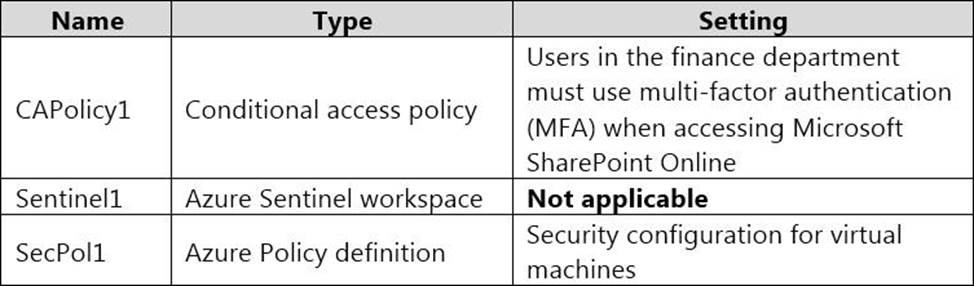
Azure AD contains the resources shown in the following table.
Subscription1 Resources
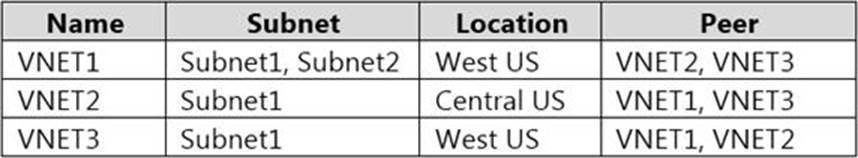
Subscription1 contains the virtual networks shown in the following table.
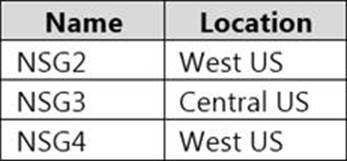
Subscription1 contains the network security groups (NSGs) shown in the following table.
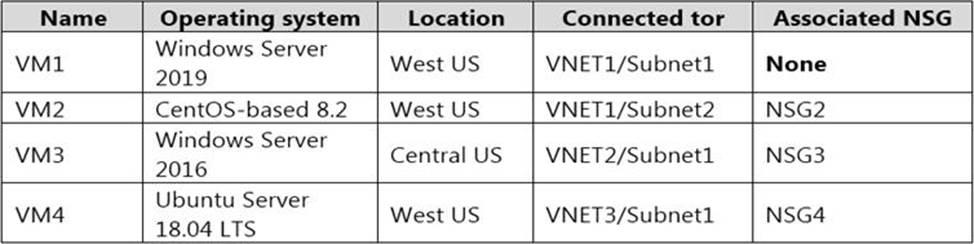
Subscription1 contains the virtual machines shown in the following table.
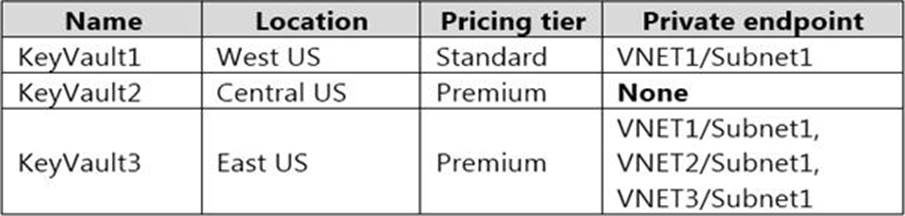
Subscription1 contains the Azure key vaults shown in the following table.
Subscription1 contains a storage account named storage1 in the West US Azure region.
Planned Changes and Requirements
Planned Changes
Fabrikam plans to implement the following changes:
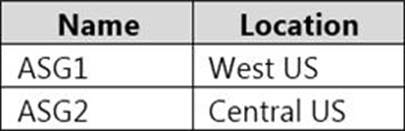
✑ Create two application security groups as shown in the following table.
✑ Associate the network interface of VM1 to ASG1.
✑ Deploy SecPol1 by using Azure Security Center.
✑ Deploy a third-party app named App1. A version of App1 exists for all available operating systems.
✑ Create a resource group named RG2.
✑ Sync OU2 to Azure AD.
✑ Add User1 to Group1.
Technical Requirements
Fabrikam identifies the following technical requirements:
✑ The finance department users must reauthenticate after three hours when they access SharePoint Online.
✑ Storage1 must be encrypted by using customer-managed keys and automatic key rotation.
✑ From Sentinel1, you must ensure that the following notebooks can be launched:
✑ VM1, VM2, and VM3 must be encrypted by using Azure Disk Encryption.
✑ Just in time (JIT) VM access for VM1, VM2, and VM3 must be enabled.
✑ App1 must use a secure connection string stored in KeyVault1.
✑ KeyVault1 traffic must NOT travel over the internet.
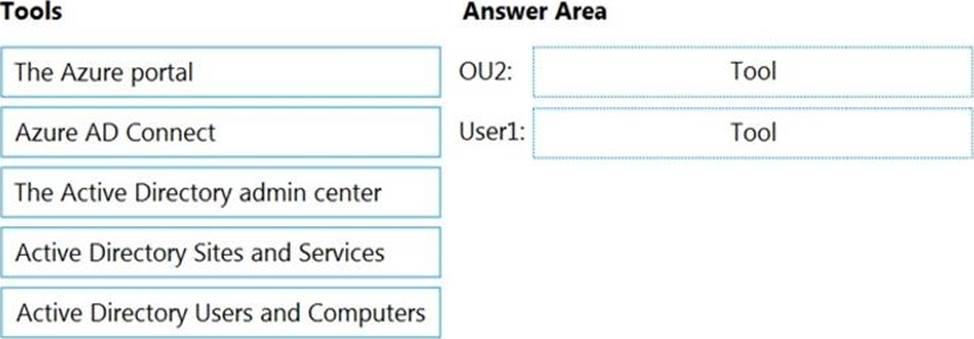
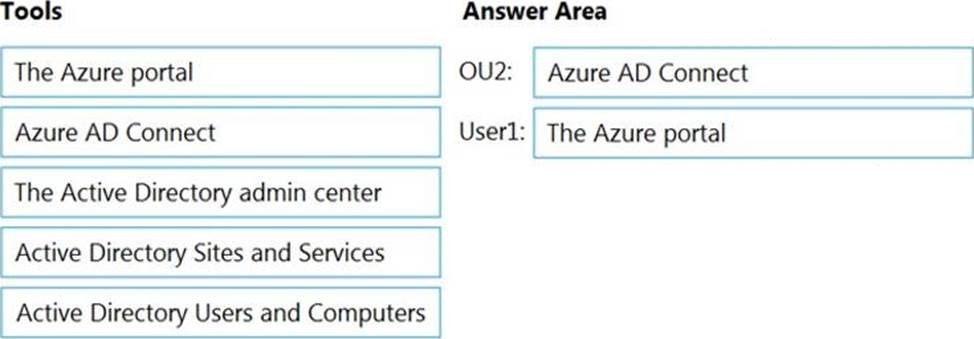
DRAG DROP
You need to perform the planned changes for OU2 and User1.
Which tools should you use? To answer, drag the appropriate tools to the correct resources. Each tool may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
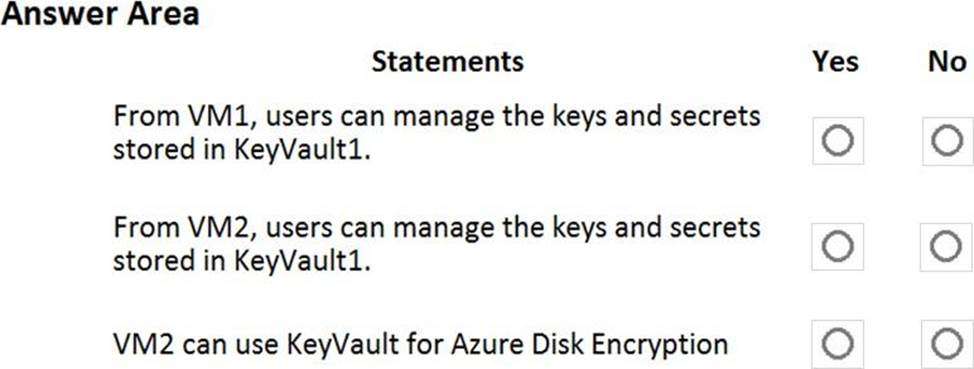
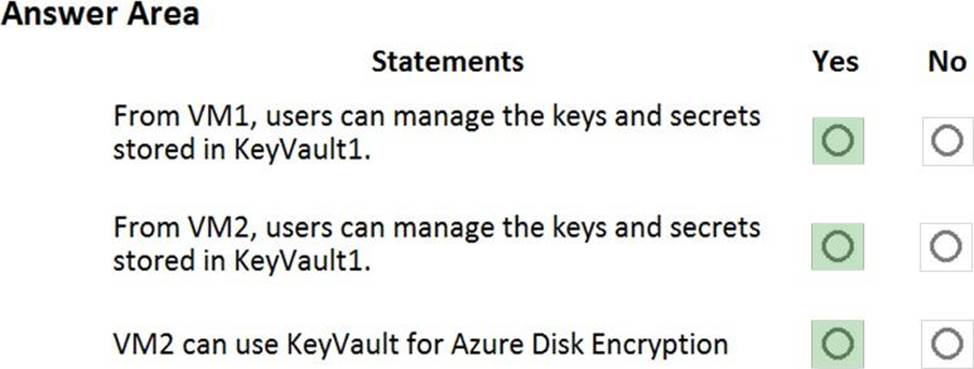
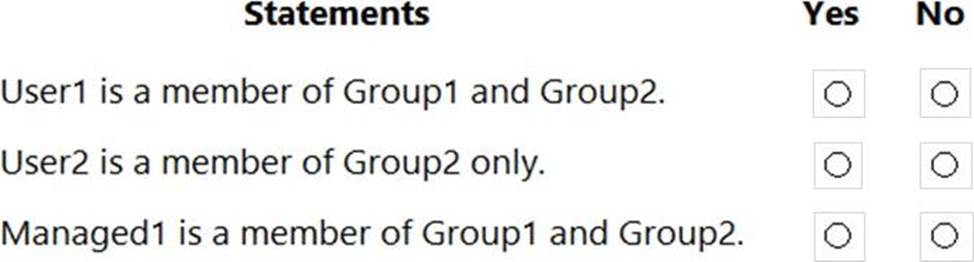
HOTSPOT
You have an Azure subscription that contains an Azure key vault named KeyVault1 and the virtual machines shown in the following table.
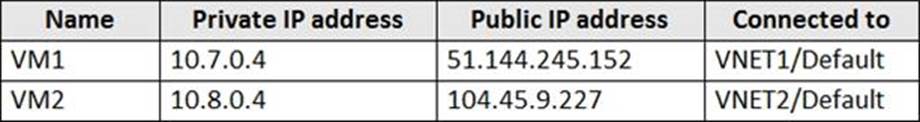
You set the Key Vault access policy to Enable access to Azure Disk Encryption for volume encryption.
KeyVault1 is configured as shown in the following exhibit.
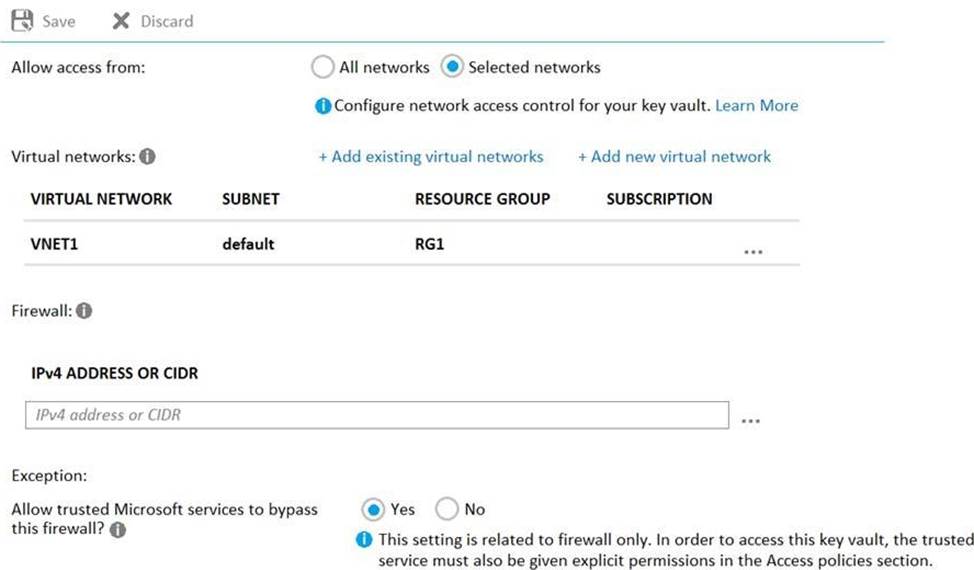
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
HOTSPOT
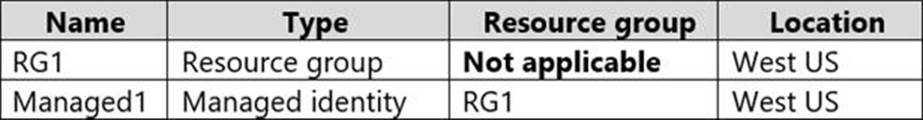
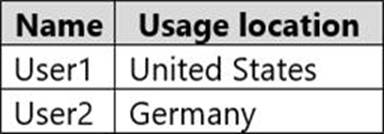
You have an Azure subscription that contains the resources shown in the following table.
The subscription is linked to an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.
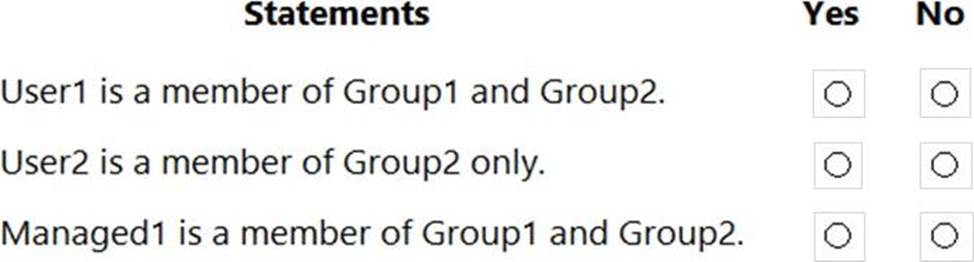
You create the groups shown in the following table.
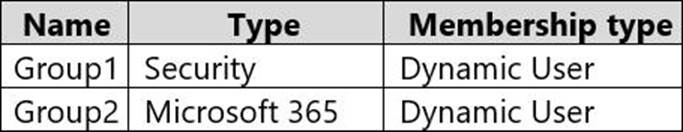
The membership rules for Group1 and Group2 are configured as shown in the following exhibit.
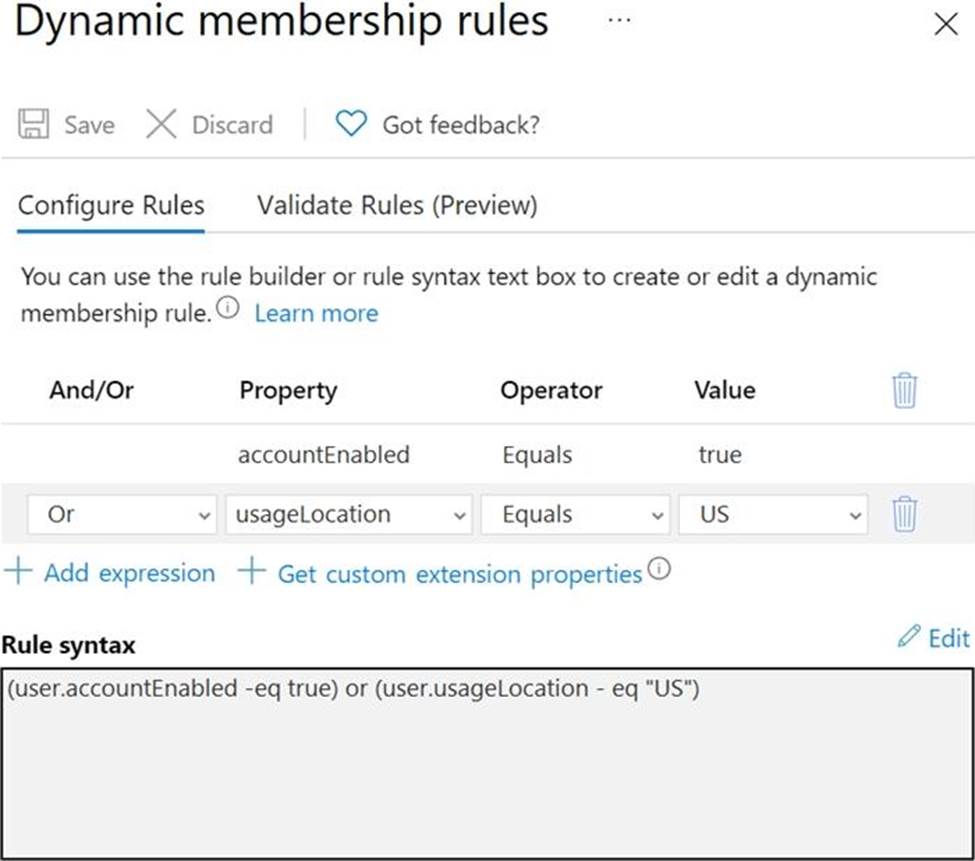
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
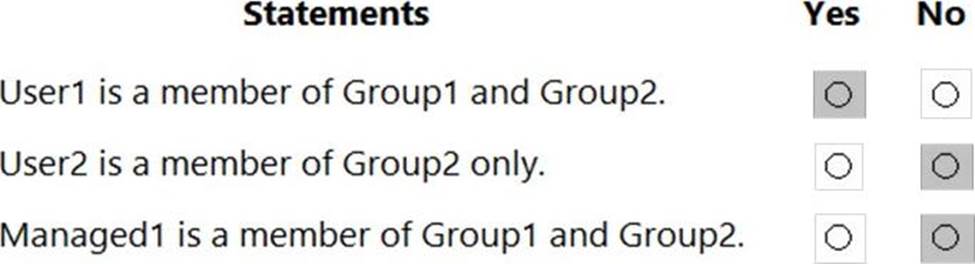
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/enterprise-users/groups-dynamic-membership
HOTSPOT
You have an Azure subscription that contains the resources shown in the following table.
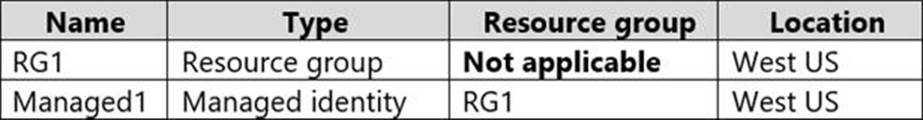
The subscription is linked to an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.
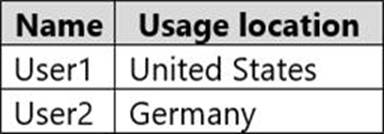
You create the groups shown in the following table.
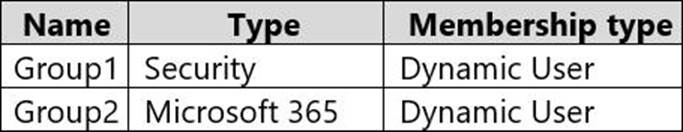
The membership rules for Group1 and Group2 are configured as shown in the following exhibit.
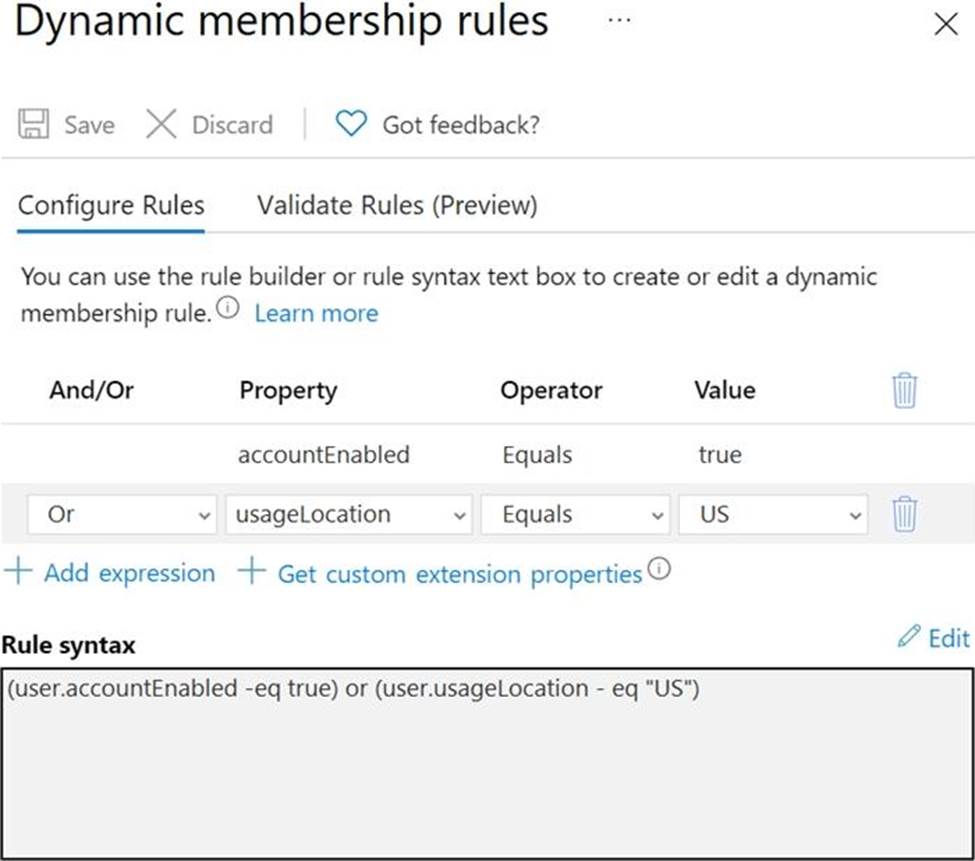
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
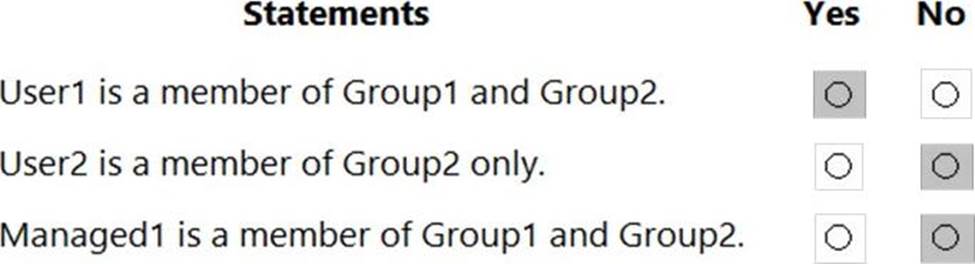
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/enterprise-users/groups-dynamic-membership
You have an Azure subscription that contains the resources shown in the following table.
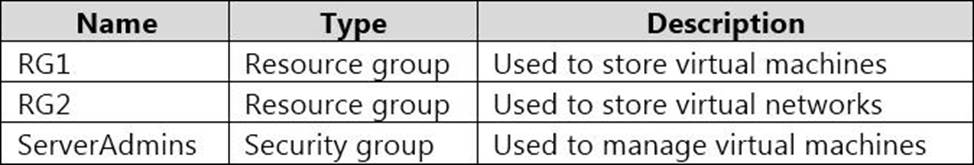
You need to ensure that ServerAdmins can perform the following tasks:
– Create virtual machine to the existing virtual network in RG2 only.
– The solution must use the principle of least privilege.
Which two role-based access control (RBAC) roles should you assign to ServerAdmins? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the Contributor role for the subscription
- B . the Network Contributor role for RG2
- C . A custom RBAC role for the subscription
- D . a custom RBAC role for RG2
- E . the Network Contributor role for RG1.
- F . the Virtual Machine Contributor role for RG1.
