Practice Free AZ-500 Exam Online Questions
HOTSPOT
You have an Azure key vault.
You need to delegate administrative access to the key vault to meet the following requirements:
– Provide a user named User1 with the ability to set advanced access policies for the key vault.
– Provide a user named User2 with the ability to add and delete certificates in the key vault.
– Use the principle of least privilege.
What should you use to assign access to each user? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
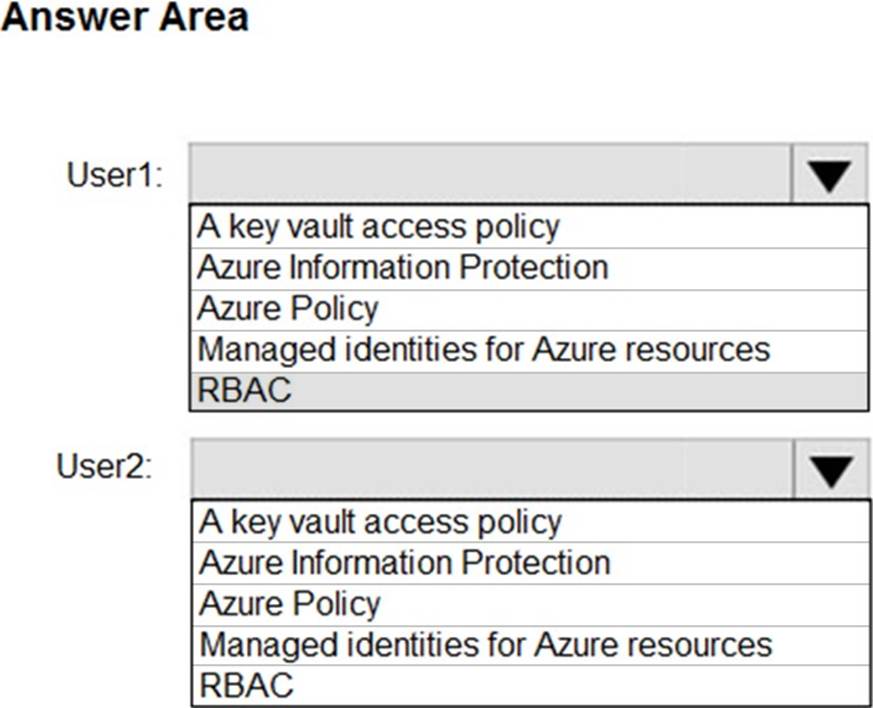
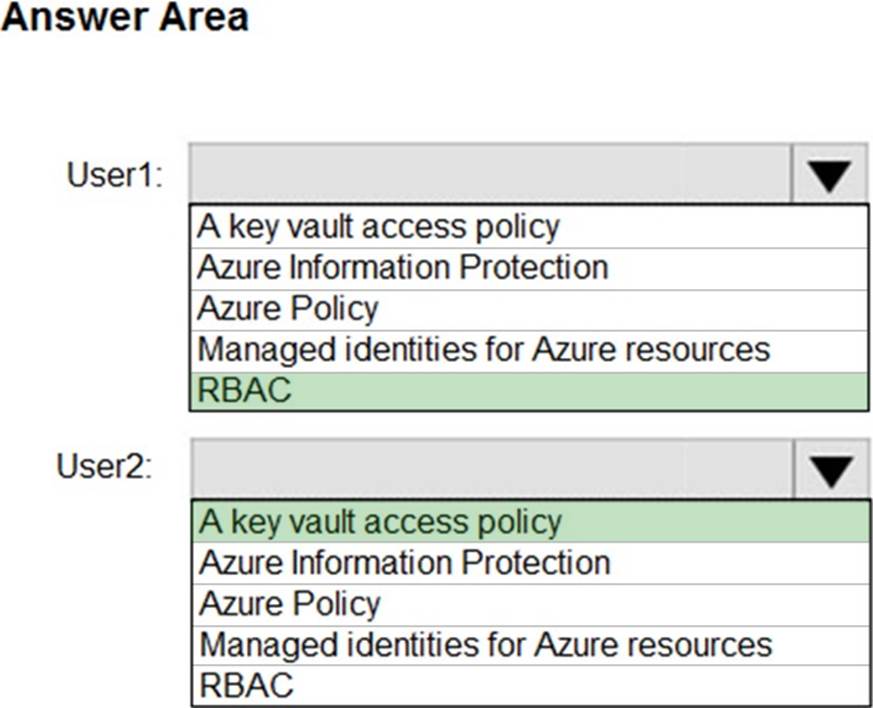
Explanation:
User1: RBAC
RBAC is used as the Key Vault access control mechanism for the management plane.
It would allow a user with the proper identity to:
✑ set Key Vault access policies
✑ create, read, update, and delete key vaults
✑ set Key Vault tags
Note: Role-based access control (RBAC) is a system that provides fine-grained access management of Azure resources. Using RBAC, you can segregate duties within your team and grant only the amount of access to users that they need to perform their jobs.
User2: A key vault access policy
A key vault access policy is the access control mechanism to get access to the key vault data plane. Key Vault access policies grant permissions separately to keys, secrets, and certificates.
References: https://docs.microsoft.com/en-us/azure/key-vault/key-vault-secure-your-key-vault
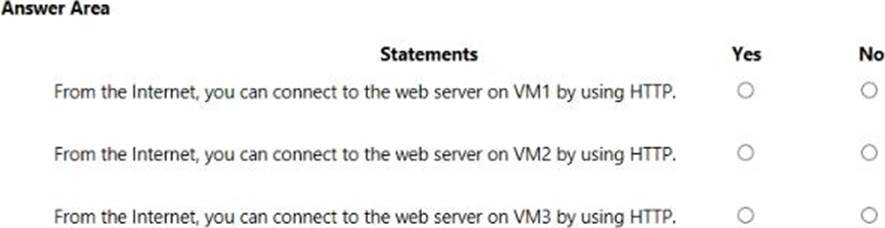
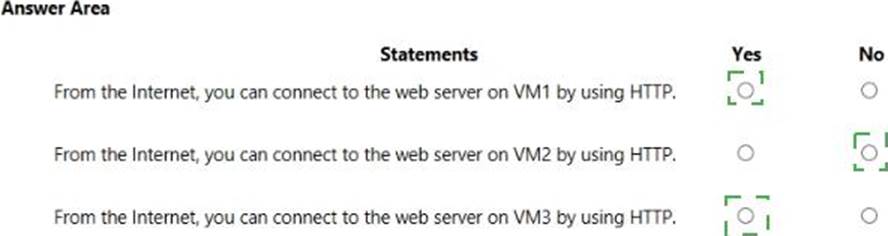
HOTSPOT
You are evaluating the security of VM1, VM2, and VM3 in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
You have Azure Resource Manager templates that you use to deploy Azure virtual machines.
You need to disable unused Windows features automatically as instances of the virtual machines are provisioned.
What should you use?
- A . device compliance policies in Microsoft Intune
- B . Azure Automation State Configuration
- C . application security groups
- D . Azure Advisor
B
Explanation:
You can use Azure Automation State Configuration to manage Azure VMs (both Classic and Resource Manager), on-premises VMs, Linux machines, AWS VMs, and on-premises physical machines.
Note: Azure Automation State Configuration provides a DSC pull server similar to the Windows Feature DSC Service so that target nodes automatically receive configurations, conform to the desired state, and report back on their compliance. The built-in pull server in Azure Automation eliminates the need to set up and maintain your own pull server. Azure Automation can target virtual or physical Windows or Linux machines, in the cloud or on-premises.
Reference: https://docs.microsoft.com/en-us/azure/automation/automation-dsc-getting-started
DRAG DROP
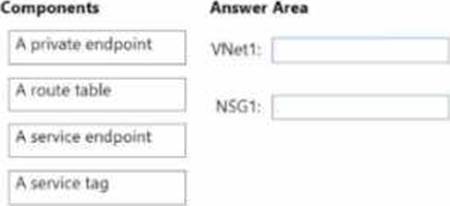
You have an Azure subscription that contains the resources shown in the following table.
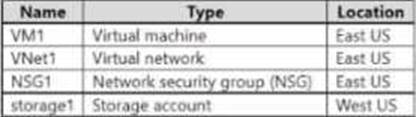
You need to configure network connectivity to meet the following requirements:
• Communication from VM1 to storage’ must traverse an optimized Microsoft backbone network.
• All the outbound traffic from VM1 to the internet must be denied.
• The solution must minimize costs and administrative effort
What should you configure for VNetl and NSG1? To answer, drag the appropriate components to the correct resources. Each component may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
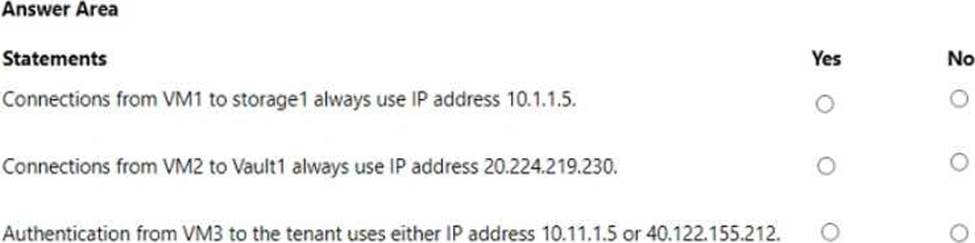
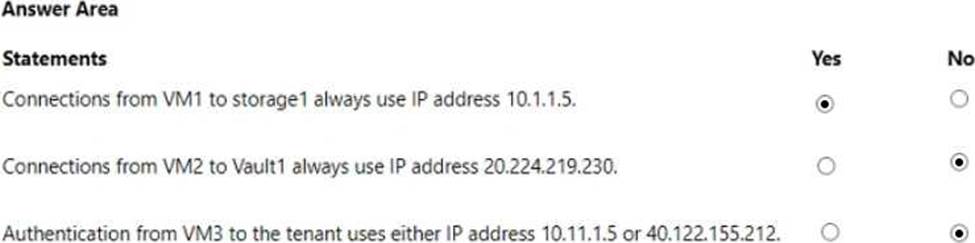
HOTSPOT
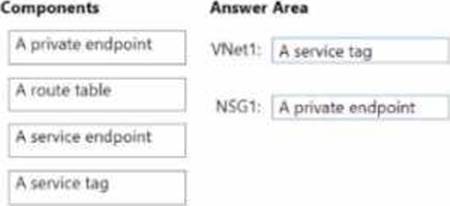
You have an Azure subscription that is linked to an Azure AD tenant and contains the virtual machines shown in the following table.
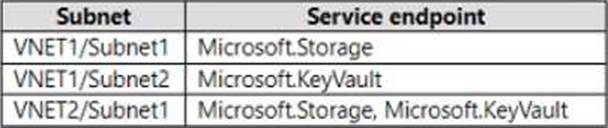
The subnets of the virtual networks have the service endpoints shown in the following table.
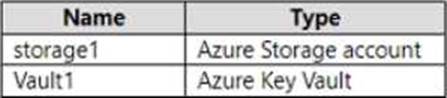
You create the resources shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains a virtual network named VNet1 VNet1 contains a single subnet. The subscription contains a virtual machine named VM1 that is connected to VNet1.
You plan to deploy an Azure SQL managed instance named SQL1.
You need to ensure that VM1 can access SQL1.
Which three components should you create? Each correct answer presents pan of the solution. NOTE: Each correct selection is worth one point.
- A . a virtual network gateway
- B . a network security group (NSG)
- C . a route table
- D . a subnet
- E . a network security perimeter
You plan to deploy an app that will modify the properties of Azure Active Directory (Azure AD) users by using Microsoft Graph. You need to ensure that the app can access Azure AD.
What should you configure first?
- A . a custom role-based access control (RBAC) role
- B . an external identity
- C . an Azure AD Application Proxy
- D . an app registration
D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-how-applications-are-added
HOTSPOT
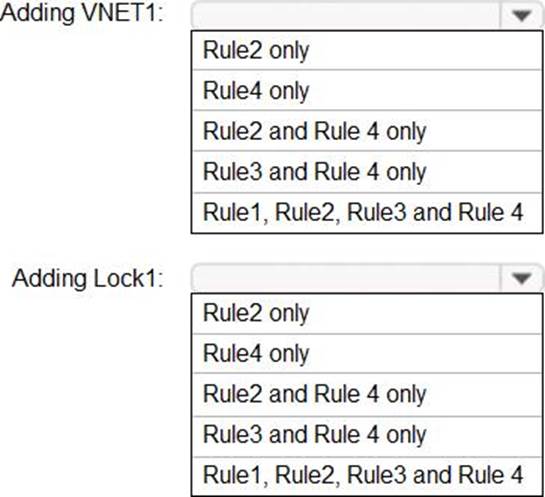
You have an Azure subscription that contains a user named Admin1 and a resource group named RG1.
In Azure Monitor, you create the alert rules shown in the following table.
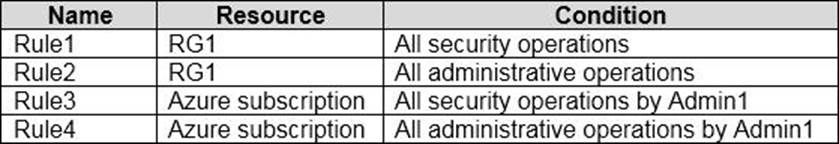
Admin1 performs the following actions on RG1:
– Adds a virtual network named VNET1
– Adds a Delete lock named Lock1
Which rules will trigger an alert as a result of the actions of Admin1? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
HOTSPOT
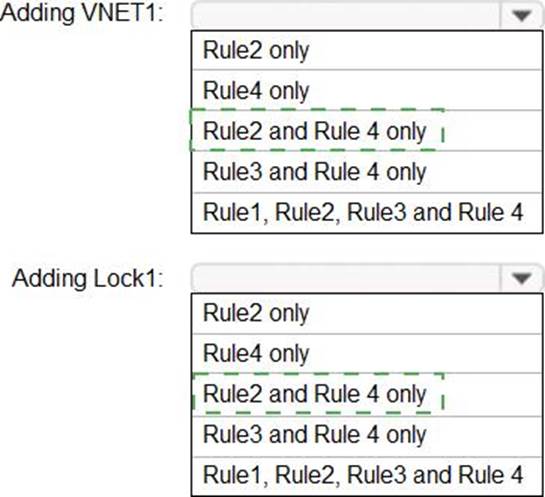
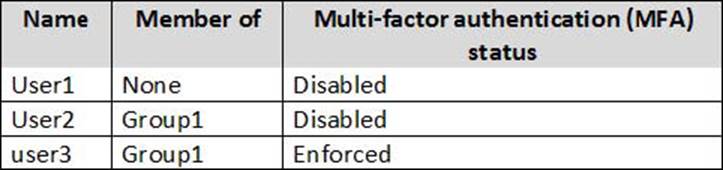
You have an Azure Active Directory (Azure AD) tenant named contoso.com that contains the users shown in the following table.
Azure AD Privileged Identity Management (PIM) is enabled for the tenant.
In PIM, the Password Administrator role has the following settings:
✑ Maximum activation duration (hours): 2
✑ Send email notifying admins of activation: Disable
✑ Require incident/request ticket number during activation: Disable
✑ Require Azure Multi-Factor Authentication for activation: Enable
✑ Require approval to activate this role: Enable
✑ Selected approver: Group1
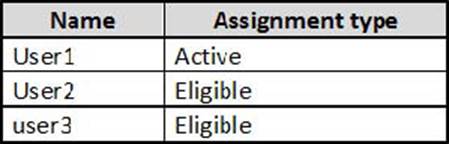
You assign users the Password Administrator role as shown in the following table.
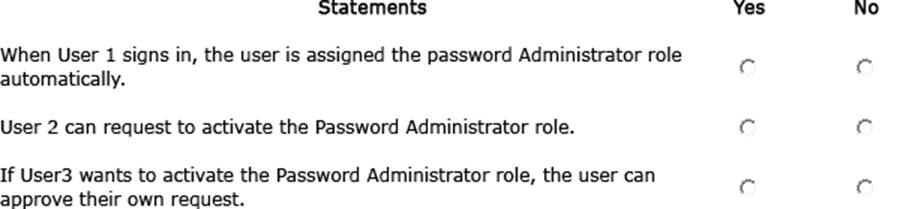
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
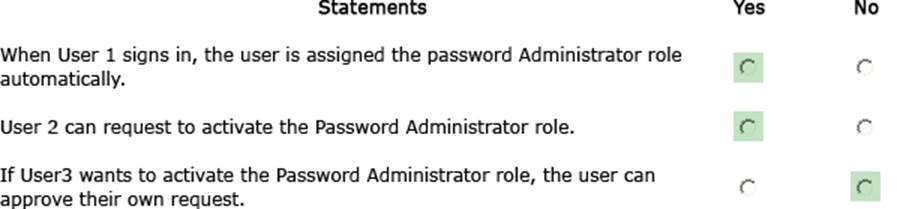
Explanation:
YES (Already active)
YES (The user will be prompted for MFA regardless the MFA Status of the user)
NO (Even the user is included in the group, a user can’t approve itself)
https://docs.microsoft.com/es-es/azure/active-directory/privileged-identity-management/pim-deployment-plan (Require approval section)
You have an Azure subscription that contains 100 virtual machines and has Azure Security Cent,-.
Standard tier enabled.
You plan to perform a vulnerability scan of each virtual machine.
You need to deploy the vulnerability scanner extension to the virtual machines by using an Azure Resource Manager template.
Which two values should you specify in the code to automate the deployment of the extension to the virtual machines? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the user assigned managed identity
- B . the Key Vault managed storage account Key
- C . the Azure Active Directory (Azure AD) ID
- D . the system-assigned managed identity
- E . the primary shared key
- F . the workspace ID
AC
Explanation:
https://docs.microsoft.com/en-us/azure/azure-arc/servers/onboard-service-principal
