Practice Free 220-1102 Exam Online Questions
An administrator responded to an incident where an employee copied financial data to a portable hard drive and then left the company with the data. The administrator documented the movement of the evidence.
Which of the following concepts did the administrator demonstrate?
- A . Preserving chain of custody
- B . Implementing data protection policies
- C . Informing law enforcement
- D . Creating a summary of the incident
A
Explanation:
Preserving chain of custody is a concept that refers to the documentation and tracking of who handled, accessed, modified, or transferred a piece of evidence, when, where, why, and how. Preserving chain of custody can help establish the authenticity, integrity, and reliability of the evidence, as well as prevent tampering, alteration, or loss of the evidence. An administrator who documented the movement of the evidence demonstrated the concept of preserving chain of custody. Implementing data protection policies, informing law enforcement, and creating a summary of the incident are not concepts that describe the action of documenting the movement of the evidence.
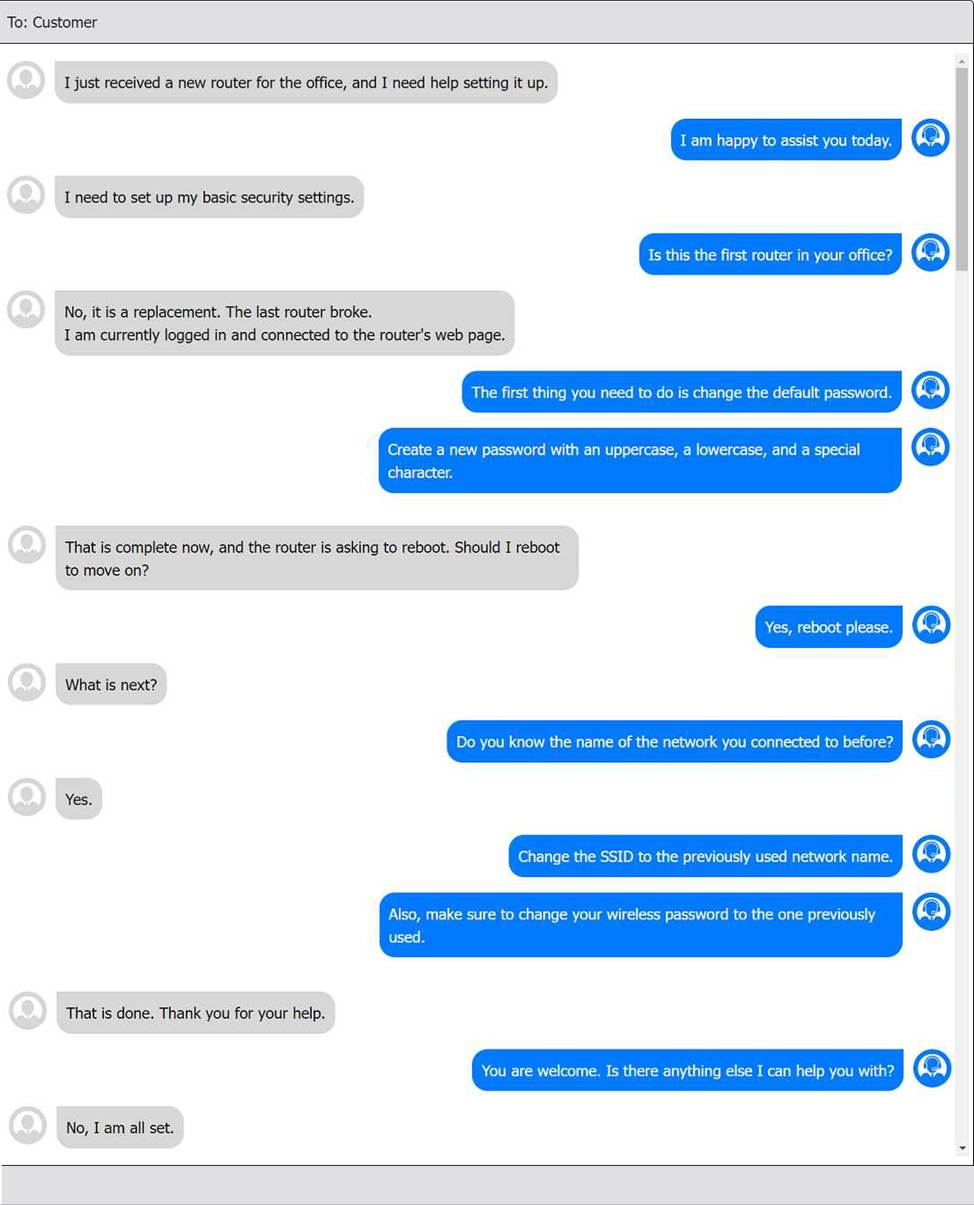
SIMULATION
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Antivirus software indicates that a workstation is infected with ransomware that cannot be quarantined.
Which of the following should be performed first to prevent further damage to the host and other systems?
- A . Turn off the machine.
- B . Run a full antivirus scan.
- C . Remove the LAN card.
- D . Install a different endpoint solution.
A
Explanation:
Turning off the machine is the first and most urgent step to prevent further damage to the host and other systems. Ransomware can encrypt files, steal data, and spread to other devices on the network if the infected machine remains online. Turning off the machine will stop the ransomware process and isolate the machine from the network12. The other options are either ineffective or risky. Running a full antivirus scan may not detect or remove the ransomware, especially if it is a new or unknown variant. Removing the LAN card may disconnect the machine from the network, but it will not stop the ransomware from encrypting or deleting files on the local drive. Installing a different endpoint solution may not be possible or helpful if the ransomware has already compromised the system or blocked the installation.
Reference: 1 3 steps to prevent and recover from ransomware(https://www.microsoft.com/en-us/security/blog/2021/09/07/3-steps-to-prevent-and-recover-from-ransomware/)2 #StopRansomware Guide | CISA(https://www.cisa.gov/stopransomware/ransomware-guide).
Which of the following features allows a technician to configure policies in a Windows 10 Professional desktop?
- A . gpedit
- B . gpmc
- C . gpresult
- D . gpupdate
A
Explanation:
The feature that allows a technician to configure policies in a Windows 10 Professional desktop is gpedit. Gpedit is a command that opens the Local Group Policy Editor, which is a utility that allows users to view and modify local group policies on their Windows PC. Local group policies are a set of rules and settings that control the behavior and configuration of the system and its users. Local group policies can be used to configure policies such as security, network, software installation and user rights. Gpmc is a command that opens the Group Policy Management Console, which is a utility that allows users to view and modify domain-based group policies on a Windows Server. Domain-based group policies are a set of rules and settings that control the behavior and configuration of the computers and users in a domain. Domain-based group policies are not available on a Windows 10 Professional desktop. Gpresult is a command that displays the result of applying group policies on a Windows PC. Gpresult can be used to troubleshoot or verify group policy settings but not to configure them. Gpupdate is a command that updates or refreshes the group policy settings on a Windows PC. Gpupdate can be used to apply new or changed group policy settings but not to configure them. References: CompTIA A+ Core 2 (220-1002) Certification Exam Objectives Version 4.0, Domain 1.6
A company is looking lot a solution that provides a backup for all data on the system while providing the lowest impact to the network.
Which of the following backup types will the company MOST likely select?
- A . Off-site
- B . Synthetic
- C . Full
- D . Differential
B
Explanation:
A synthetic backup is a backup type that provides a backup for all data on the system while providing the lowest impact to the network. It combines a full backup with one or more incremental backups to create a single backup set, without requiring access to the original data source. Off-site is a backup location, not a backup type. Full and differential are backup types, but they have a higher impact on the network than synthetic.
Verified References: https://www.comptia.org/blog/what-is-a-synthetic-backup https://www.comptia.org/certifications/a
A help desk technician needs to remotely access and control a customer’s Windows PC by using a secure session that allows the technician the same control as the customer.
Which of the following tools provides this type of access?
- A . FTP
- B . RDP
- C . SSH
- D . VNC
B
Explanation:
RDP stands for Remote Desktop Protocol, which is a proprietary protocol developed by Microsoft that allows a user to remotely access and control another computer over a network. RDP provides a secure session that encrypts the data between the client and the host, and allows the user to see and interact with the desktop and applications of the remote computer as if they were sitting in front of it. RDP also supports features such as audio, video, clipboard, printer, and file sharing, as well as multiple monitor support and session recording. To use RDP, the host computer must have Remote Desktop enabled and configured, and the client computer must have a Remote Desktop client software installed. The client can connect to the host by entering its IP address, hostname, or domain name, and providing the login credentials of a user account on the host. RDP is commonly used for remote administration, technical support, and remote work scenarios
A change advisory board authorized a setting change so a technician is permitted to Implement the change. The technician successfully implemented the change .
Which of the following should be done next?
- A . Document the date and time of change
- B . Document the purpose of the change.
- C . Document the risk level.
- D . Document the findings of the sandbox test,
A
Explanation:
The correct answer is A) Document the date and time of change. After implementing a change, the technician should document the date and time of change in the change log or record. This helps to track the change history, monitor the change performance, and identify any issues or incidents related to the change. Documenting the date and time of change is also a good practice for auditing and compliance purposes.
Documenting the purpose of the change (B) and the risk level © are steps that should be done before implementing the change, not after. These are important information that help to justify, prioritize, and plan the change. The purpose of the change should explain why the change is needed and what benefits it will bring to the organization. The risk level should assess the potential impact and probability of the change causing any problems or disruptions to the business.
Documenting the findings of the sandbox test (D) is also a step that should be done before implementing the change, not after. A sandbox test is a way of testing the change in an isolated environment that mimics the production environment. This helps to verify that the change works as expected and does not cause any errors or conflicts with other systems or processes. The findings of the sandbox test should be documented and reviewed by the change advisory board (CAB) before approving the change for implementation.
Reference: What is a Change Advisory Board? (Overview, Roles, and Responsibilities) Best Practices in Change Management
10 Top change management best practices
In an organization with a standardized set of installed software, a developer submits a request to have new software installed. The company does not currently have a license for this software, but the developer already downloaded the installation file and is requesting that the technician install it. The developer states that the management team approved the business use of this software.
Which of the following is the best action for the technician to take?
- A . Contact the software vendor to obtain the license for the user, and assist the user with installation once the license is purchased.
- B . Run a scan on the downloaded installation file to confirm that it is free of malicious software, install the software, and document the software installation process.
- C . Indicate to the developer that formal approval is needed; then, the IT team should investigate the software and the impact it will have on the organization before installing the software.
- D . Install the software and run a full system scan with antivirus software to confirm that the operating system is free of malicious software.
C
Explanation:
Installing new software on an organization’s system or device can have various implications, such as compatibility, security, performance, licensing, and compliance issues. Therefore, it is important to follow the best practices for software installation, such as doing research on the software, checking the system requirements, scanning the installation file for malware, and obtaining the proper license345. The technician should not install the software without formal approval from the management team, as this could violate the organization’s policies or regulations. The technician should also not install the software without investigating the software and its impact on the organization, as this could introduce potential risks or problems to the system or device. The technician should indicate to the developer that formal approval is needed, and then work with the IT team to evaluate the software and its suitability for the organization before installing it
A technician is finalizing a new workstation for a user. The user’s PC will be connected to the internet but will not require the same private address each time.
Which of the following protocols will the technician MOST likely utilize?
- A . DHCP
- B . SMTP
- C . DNS
- D . RDP
A
Explanation:
DHCP stands for Dynamic Host Configuration Protocol and it is used to assign IP addresses and other network configuration parameters to devices on a network automatically. This is useful for devices that do not require the same private address each time they connect to the internet.
The following error is displayed on a user’s computer screen:
No operating system found
Which of the following is the first troubleshooting step a technician should complete?
- A . Disconnect external storage
- B . Flash the BIOS
- C . Replace the SATA cable
- D . Turn on the device in safe mode
A
Explanation:
Detailed
The first step is to disconnect external storage (Option A). Sometimes, the system may be attempting to boot from an external drive or USB device instead of the internal hard drive. By removing the external storage, the system will attempt to boot from the correct drive.
Flashing the BIOS (Option B) is more complex and typically unnecessary for this issue. Replacing the SATA cable (Option C) may help if there’s a hardware issue, but it’s not the first troubleshooting step.
Turning on the device in safe mode (Option D) would not work if no operating system is detected.
CompTIA A+ Core 2
Reference: 5.1 – Apply troubleshooting methodologies, including steps for resolving boot issues.
