Practice Free 220-1102 Exam Online Questions
A company discovered that numerous computers from multiple geographic locations are sending a very high number of connection requests which is causing the company’s web server to become unavailable to the general public.
Which of the following attacks is occurring?
- A . Zero day
- B . SOL injection
- C . Cross-site scripting
- D . Distributed denial of service
D
Explanation:
The company is experiencing a distributed denial of service (DDoS) attack. A DDoS attack is a type of cyber attack in which multiple compromised systems are used to target a single system, causing a denial of service for users of the targeted system.
A technician suspects a rootkit has been installed and needs to be removed.
Which of the following would BEST resolve the issue?
- A . Application updates
- B . Anti-malware software
- C . OS reinstallation
- D . File restore
C
Explanation:
If a rootkit has caused a deep infection, then the only way to remove the rootkit is to reinstall the operating system. This is because rootkits are designed to be difficult to detect and remove, and they can hide in the operating system’s kernel, making it difficult to remove them without reinstalling the operating system https://www.minitool.com/backup-tips/how-to-get-rid-of-rootkit-windows-10.html
A technician needs to formal a USB drive to transfer 20GB of data from a Linux computer to a Windows computer.
Which of the following filesystems will the technician MOST likely use?
- A . FAT32
- B . ext4
- C . NTFS
- D . exFAT
D
Explanation:
A technician sees a file that is requesting payment to a cryptocurrency address.
Which of the following should the technician do first?
- A . Quarantine the computer.
- B . Disable System Restore.
- C . Update the antivirus software definitions.
- D . Boot to safe mode.
A
Explanation:
Quarantining the computer means isolating it from the network and other devices to prevent the spread of malware or ransomware. Ransomware is a type of malware that encrypts the files on a computer and demands payment (usually in cryptocurrency) to restore them. If a technician sees a file that is requesting payment to a cryptocurrency address, it is likely that the computer has been infected by ransomware. Quarantining the computer should be the first step to contain the infection and prevent further damage. Disabling System Restore, updating the antivirus software definitions, and booting to safe mode are not steps that should be done before quarantining the computer.
An application user received an email indicating the version of the application currently in use will no longer be sold. Users with this version of the application will no longer receive patches or updates either.
Which of the following indicates a vendor no longer supports a product?
- A . AUP
- B . EULA
- C . EOL
- D . UAC
C
Explanation:
EOL (end-of-life) is a term that indicates a vendor no longer supports a product. It means that the product will no longer be sold, updated or patched by the vendor, and that the users should migrate to a newer version or alternative product. AUP (acceptable use policy), EULA (end-user license agreement) and UAC (user account control) are not terms that indicate a vendor no longer supports a product.
Verified References: https://www.comptia.org/blog/what-is-end-of-life https://www.comptia.org/certifications/a
A technician is working to resolve a Wi-Fi network issue at a doctor’s office that is located next to an apartment complex. The technician discovers that employees and patients are not the only people on the network.
Which of the following should the technician do to BEST minimize this issue?
- A . Disable unused ports.
- B . Remove the guest network
- C . Add a password to the guest network
- D . Change the network channel.
C
Explanation:
The question suggests that unauthorized users from the neighboring apartment complex may be accessing the network. By adding a password to the guest network, the technician can restrict access to only those who have been given the password. This should help to minimize unauthorized access from individuals in the apartment complex.
While changing the network channel might help with interference issues (common in environments with many Wi-Fi networks), it wouldn’t necessarily help prevent unauthorized access. Disabling unused ports and removing the guest network can be too restrictive and might hinder legitimate usage for guests or certain devices.
Which of the following macOS features provides the user with a high-level view of all open windows?
- A . Mission Control
- B . Finder
- C . Multiple Desktops
- D . Spotlight
A
Explanation:
Mission Control is the macOS feature that provides the user with a high-level view of all open windows. Mission Control allows the user to see and switch between multiple desktops, full-screen apps, and windows in a single screen. Mission Control can be accessed by swiping up with three or four fingers on the trackpad, pressing F3 on the keyboard, or moving the cursor to a hot corner
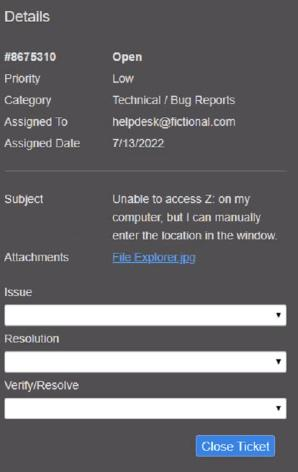
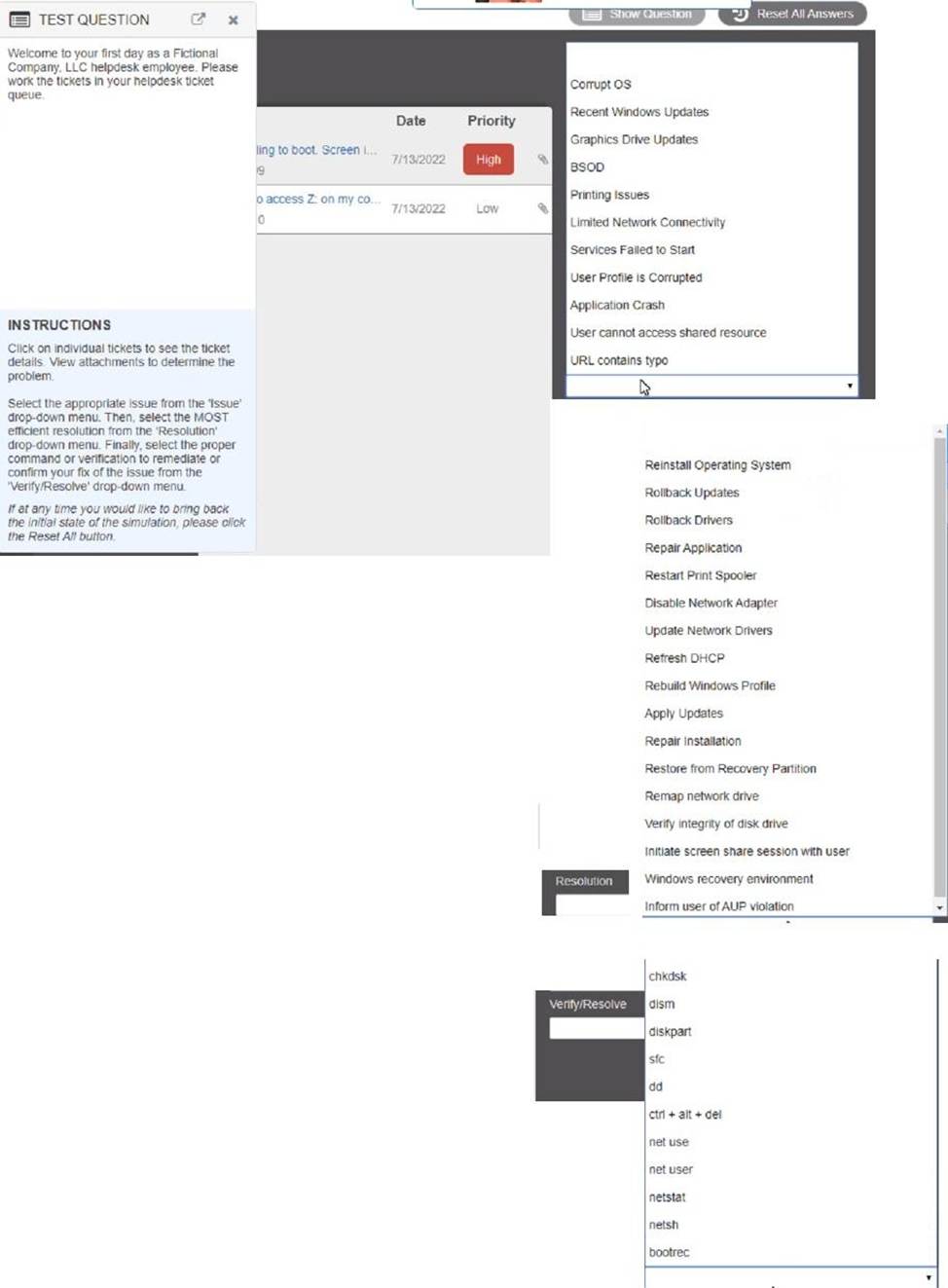
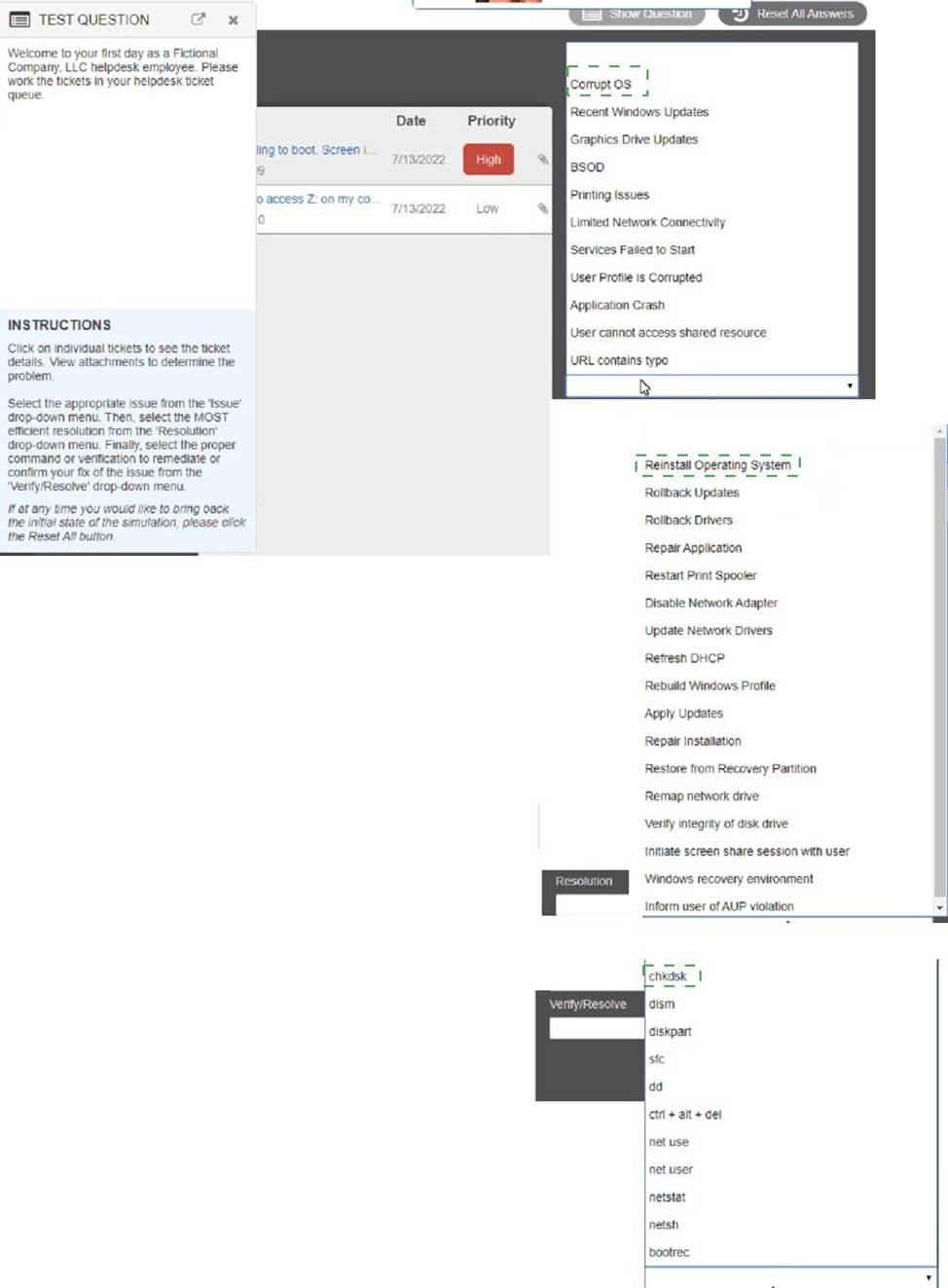
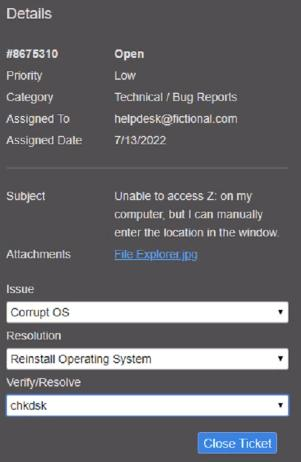
HOTSPOT
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
Click on individual tickers to see the ticket details. View attachments to determine the problem.
Select the appropriate issue from the ‘issue’ drop-down menu. Then, select the MOST efficient resolution from the ‘Resolution’ drop-down menu. Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
Explanation:
Graphical user interface, text, application
Description automatically generated
Which of the following best describes a rollback plan?
- A . A developer configures a process to return to the starting state upon completion.
- B . A user asks to remove an unneeded fileshare.
- C . An administrator applies new settings to a computer after the previous settings failed.
- D . A technician reverts the system to a previous state following a failed upgrade.
D
Explanation:
A rollback plan describes the process of reverting a system to its previous state after a failed upgrade or change. This ensures system stability and functionality by restoring known good configurations and is a crucial part of change management to minimize disruptions in case of unsuccessful updates.
Which of the following threats will the use of a privacy screen on a computer help prevent?
- A . Impersonation
- B . Shoulder surfing
- C . Whaling
- D . Tailgating
B
Explanation:
Shoulder surfing is a threat that involves someone looking over another person’s shoulder to observe their screen, keyboard, or other sensitive information. Shoulder surfing can be used to steal passwords, personal identification numbers (PINs), credit card numbers, or other confidential data. The use of a privacy screen on a computer can help prevent shoulder surfing by limiting the viewing angle of the screen and making it harder for someone to see the screen from the side or behind. Impersonation, whaling, and tailgating are not threats that can be prevented by using a privacy screen on a computer.
