Practice Free 200-301 Exam Online Questions
What are two advantages of implementing a controller-based architecture instead of a traditional network architecture? (Choose two.)
- A . It allows for seamless connectivity to virtual machines.
- B . It supports complex and high-scale IP addressing schemes.
- C . It enables configuration task automation.
- D . It provides increased scalability and management options.
- E . It increases security against denial-of-service attacks.
Refer to the exhibit.
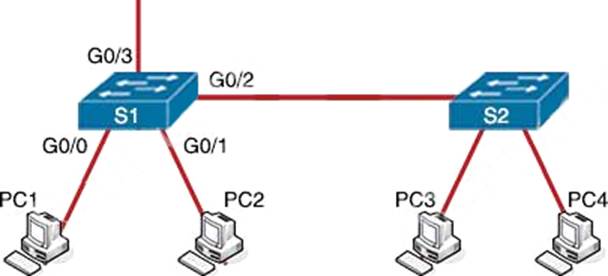
PC1 is trying to ping PC3 for the first time and sends out an ARP to S1.
Which action is taken by S1?
- A . It forwards it out G0/3 only
- B . It is flooded out every port except G0/0.
- C . It drops the frame.
- D . It forwards it out interface G0/2 only.
How does QoS optimize voice traffic?
- A . reducing bandwidth usage
- B . by reducing packet loss
- C . by differentiating voice and video traffic
- D . by increasing jitter
How does WPA3 improve security?
- A . It uses SAE for authentication.
- B . It uses a 4-way handshake for authentication.
- C . It uses RC4 for encryption.
- D . It uses TKIP for encryption.
What is the purpose of using First Hop Redundancy Protocol on a specific subnet?
- A . ensures a loop-free physical topology
- B . filters traffic based on destination IP addressing
- C . sends the default route to the hosts on a network
- D . forwards multicast hello messages between routers
Where is the interface between the control plane and data plane within the software-defined
architecture?
- A . control layer and the infrastructure layer
- B . application layer and the infrastructure layer
- C . control layer and the application layer
- D . application layer and the management layer
Exhibit.
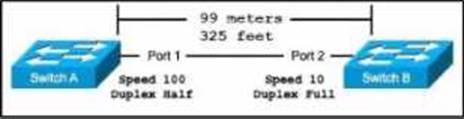
The switches are connected via a Cat5 Ethernet cable that was successfully tested. The Interfaces are configured as access ports and are both in a ‘down" status.
What is the cause of this issue?
- A . The switches are configured with incompatible duplex settings.
- B . The distance between the two switches is not supported by Cut5.
- C . The speed settings on the switches are mismatched.
- D . The portfast command is missing from the configuration.
A Cisco IP phone receive untagged data traffic from an attached PC.
Which action is taken by the phone?
- A . It allows the traffic to pass through unchanged
- B . It drops the traffic
- C . It tags the traffic with the default VLAN
- D . It tags the traffic with the native VLAN
A
Explanation:
https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst2960x/software/15-0_2_EX/vlan/configuration_guide/b_vlan_152ex_2960-x_cg/b_vlan_152ex_2960-x_cg_chapter_0110.pdf
Untagged traffic from the device attached to the Cisco IP Phone passes through the phone unchanged, regardless of the trust state of the access port on the phone.
Which type of security program is violated when a group of employees enters a building using the ID badge of only one person?
- A . intrusion detection
- B . user awareness
- C . physical access control
- D . network authorization
Which state does the switch port move to when PortFast is enabled?
- A . forwarding
- B . listening
- C . blocking
- D . learning
