Practice Free 200-301 Exam Online Questions
Which EtherChannel mode must be configured when using LAG on a WLC?
- A . on
- B . active
- C . auto
- D . passive
Refer to the exhibit.
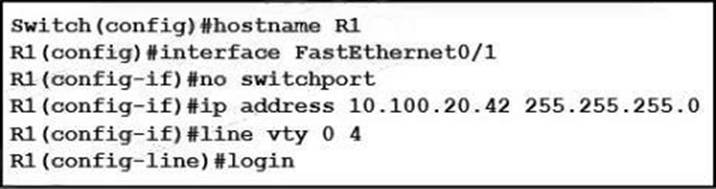
An engineer booted a new switch and applied this configuration via the console port.
Which additional configuration must be applied to allow administrators to authenticate directly to enable privilege mode via Telnet using a local username and password?
- A . R1(config)#username admin privilege 15 secret p@ss1234
R1(config-if)#line vty 0 4
R1(config-line)#login local - B . R1(config)#username admin secret p@ss1234
R1(config-if)#line vty 0 4
R1(config-line)#login local
R1(config)#enable secret p@ss1234 - C . R1(config)#username admin
R1(config-if)#line vty 0 4
R1(config-line)#password p@ss1234
R1(config-line)#transport input telnet - D . R1(config)#username admin
R1(config-if)#line vty 0 4
R1(config-line)#password p@ss1234
What is the difference in data transmission delivery and reliability between TCP and UDP?
- A . TCP transmits data at a higher rate and ensures packet delivery. UDP retransmits lost data to ensure applications receive the data on the remote end.
- B . UDP sets up a connection between both devices before transmitting data. TCP uses the three-way handshake to transmit data with a reliable connection.
- C . UDP is used for multicast and broadcast communication. TCP is used for unicast communication and transmits data at a higher rate with error checking.
- D . TCP requires the connection to be established before transmitting data. UDP transmits data at a higher rate without ensuring packet delivery.
What are two differences between WPA2 and WPA3 wireless security? (Choose two.)
- A . WPA3 um AES for stronger protection than WPA2 which uses SAE
- B . WPA2 uses 1 M-bit key encryption and WPA3 requires 256-brt key encryption
- C . WPA3 uses AES for stronger protection than WPA2 which uses TKIP WPA3 uses
- D . SAE tor stronger protection than WPA2 which uses AES
- E . WPA2 uses 12B-M key encryption and WPA3 supports 128 bit and 192 bit key encryption
Refer to the exhibit.
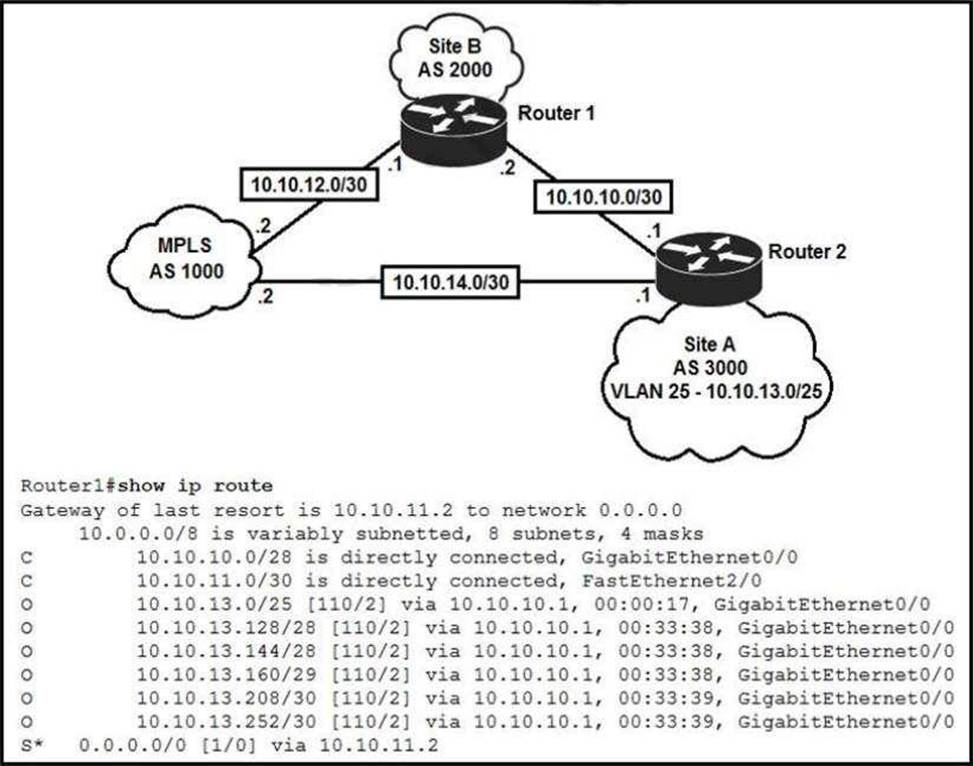
An engineer is bringing up a new circuit to the MPLS provider on the Gi0/1 interface of Router1 The new circuit uses eBGP and teams the route to VLAN25 from the BGP path.
What s the expected behavior for the traffic flow for route 10.10.13.0/25?
- A . Traffic to 10.10.13.0.25 is load balanced out of multiple interfaces
- B . Route 10.10.13.0/25 is updated in the routing table as being learned from interface Gi0/1.
- C . Traffic to 10.10.13.0/25 is asymmeteical
- D . Route 10.10.13.0/25 learned via the Gi0/0 interface remains in the routing table
What is a reason to implement LAG on a Cisco WLC?
- A . Increase the available throughput on the link.
- B . Increase security by encrypting management frames
- C . Allow for stateful failover between WLCs
- D . Enable the connected switch ports to use different Layer 2 configurations
A
Explanation:
Link Aggregation Group (LAG) is a feature that allows you to bundle multiple physical Ethernet links into a single logical link, and is used to increase the available throughput on the link. LAG is supported on the Cisco Wireless LAN Controller (WLC) and the connected switch ports [1], and can be used to provide greater bandwidth and increased redundancy. It also enables the connected switch ports to use different Layer 2 configurations, such as Spanning Tree Protocol (STP) and Hot Standby Router Protocol (HSRP).
Which solution is appropriate when mitigating password attacks where the attacker was able to sniff the clear-text password of the system administrator?
- A . next-generation firewall to keep stateful packet inspection
- B . multifactor authentication using two separate authentication sources
- C . ACL to restrict incoming Telnet sessions "admin" accounts
- D . IPS with a btock list of known attack vectors
Which solution is appropriate when mitigating password attacks where the attacker was able to sniff the clear-text password of the system administrator?
- A . next-generation firewall to keep stateful packet inspection
- B . multifactor authentication using two separate authentication sources
- C . ACL to restrict incoming Telnet sessions "admin" accounts
- D . IPS with a btock list of known attack vectors
A network architect is deciding whether to implement Cisco autonomous access points or lightweight access points.
Which fact about firmware updates must the architect consider? Unlike lightweight access points, which require
- A . Unlike lightweight access points, which require redundant WLCs to support firmware upgrades, autonomous access points require only one WLC.
- B . Unlike autonomous access points, lightweight access points store a complete copy of the current firmware for backup.
- C . Unlike lightweight access points, autonomous access points can recover automatically from a corrupt firmware update.
- D . Unlike autonomous access points, lightweight access points require a WLC to implement remote firmware updates.
Refer to the exhibit.
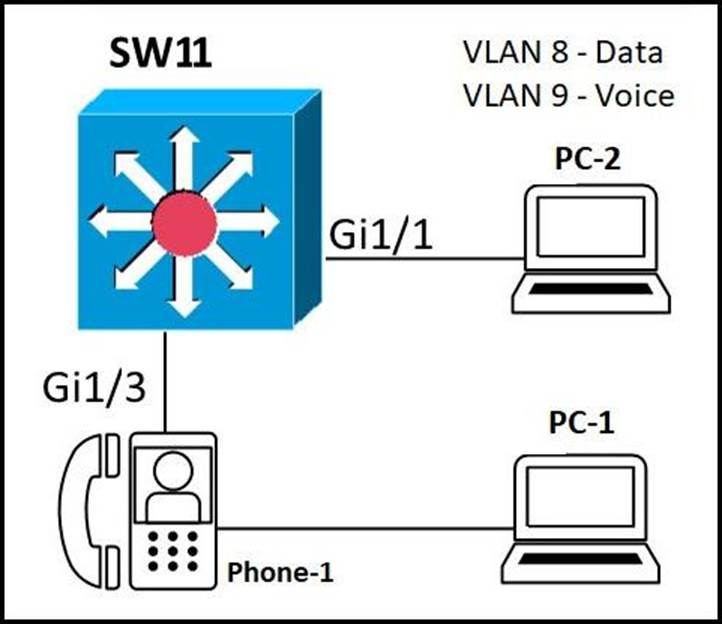
An administrator must configure interfaces Gi1/1 and Gi1/3 on switch SW11 PC-1 and PC-2 must be placed in the Data VLAN and Phone-1 must be placed in the Voice VLAN.
Which configuration meets these requirements?
- A . interface gigabitethernet1/1
switchport mode access
switchport access vlan 8
!
interface gigabitethernet1/3
switchport mode access
switchport voice vlan 8
switchport access vlan 9 - B . interface gigabitethernet1/1
switchport mode access
switchport access vlan 9
!
interface gigabitethernet1/3
switchport mode trunk
switchport voice vlan 8
switchport access vlan 9 - C . interface gigabitethernet1/1
switchport mode access
switchport access vlan 8
!
interface gigabitethernet1/3
switchport mode access
switchport access vlan 8
switchport voice vlan 9 - D . interface gigabitethernet1/1
switchport mode access
switchport access vlan 8
!
interface gigabitethernet1/3
switchport mode trunk
switchport voice vlan 8
switchport access vlan 9
