Practice Free 200-301 Exam Online Questions
Refer to the exhibit.
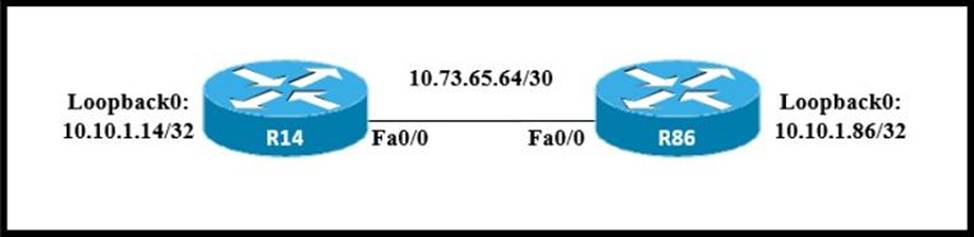
All interfaces are configured with duplex auto and ip ospf network broadcast.
Which configuration allows routers R14 and R86 to form an OSPFv2 adjacency and act as a central point for exchanging OSPF information between routers?
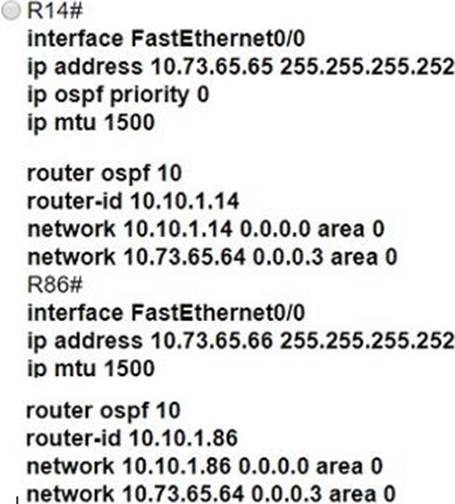
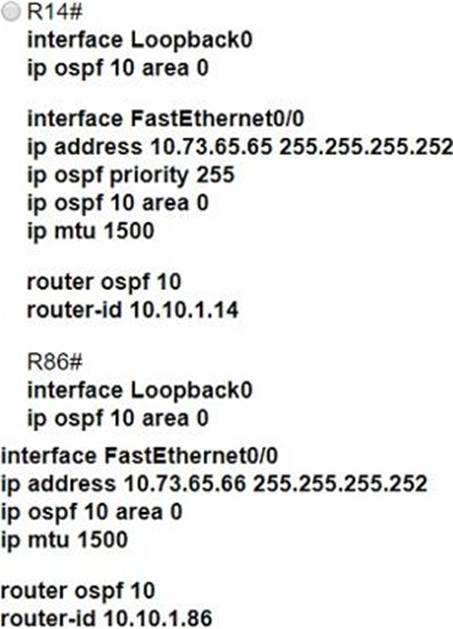
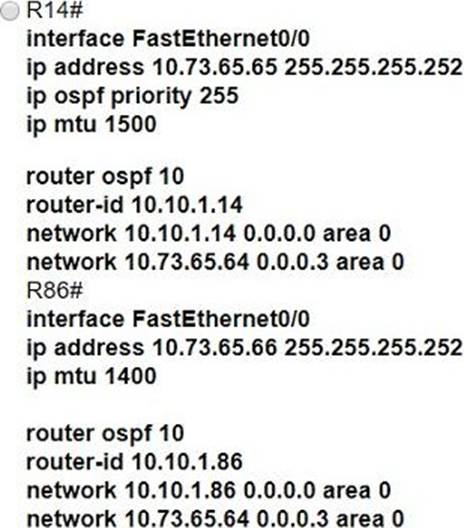
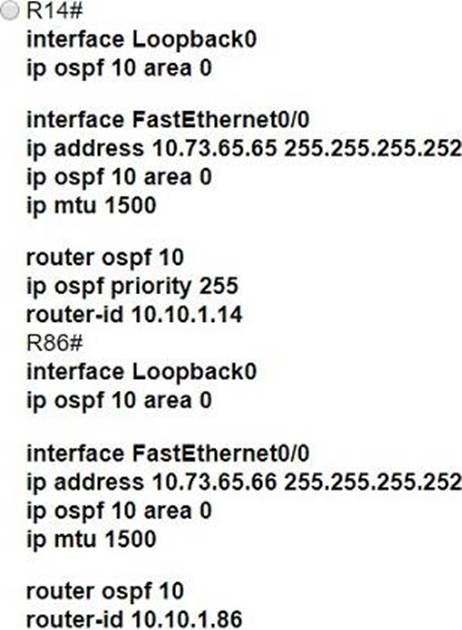
- A . Option A
- B . Option B
- C . Option C
- D . option D
How does IPsec provide secure networking for applications within an organization?
- A . It takes advantage of FTP to secure file transfers between nodes on the network.
- B . It provides GRE tunnels to transmit traffic securely between network nodes.
- C . It enables sets of security associations between peers.
- D . It leverages TFTP providing secure file transfers among peers on the network.
C
Explanation:
IPsec (Internet Protocol Security) is a protocol suite that provides secure communication over Internet Protocol (IP) networks. It achieves this by authenticating and encrypting each IP packet within a communication session. One of the key concepts in IPsec is the establishment of security associations (SAs) between peers. Security associations are the combination of algorithms and keys used to secure communication between two devices. They define the security parameters for the communication, including the encryption algorithm, integrity algorithm, and keying information. By establishing these security associations, IPsec ensures confidentiality, integrity, and authenticity of the data being transmitted between network nodes.
What is a requirement when configuring or removing LAG on a WLC?
- A . The Incoming and outgoing ports for traffic flow must be specified If LAG Is enabled.
- B . The controller must be rebooted after enabling or reconfiguring LAG.
- C . The management interface must be reassigned if LAG disabled.
- D . Multiple untagged interfaces on the same port must be supported.
Which command enables HTTP access to the Cisco WLC?
- A . config network secureweb enable
- B . config certificate generate web admin
- C . config network webmode enable
- D . config network telnet enable
What are two examples of multifactor authentication? (Choose two.)
- A . single sign-on
- B . unique user knowledge
- C . passwords that expire
- D . soft tokens
- E . shared password responsibility
Which protocol uses the SSL?
- A . HTTP
- B . SSH
- C . HTTPS
- D . Telnet
Refer to the exhibit.
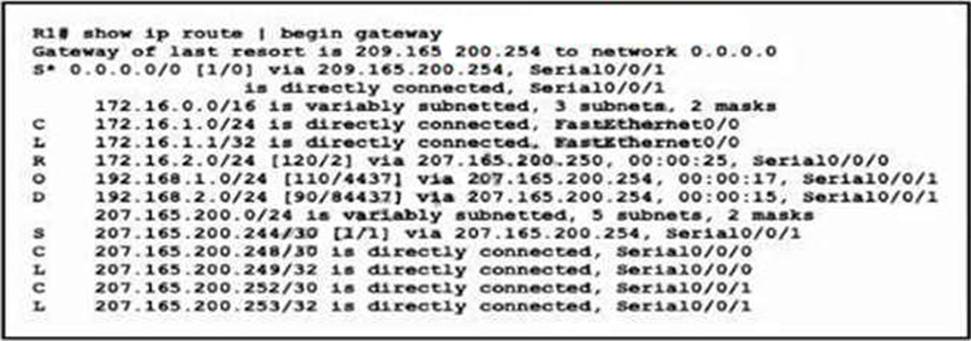
Which network prefix was learned via EIGRP?
- A . 172.16.0.0/16
- B . 192.168.2.0/24
- C . 207.165.200.0/24
- D . 192.168.1.0/24
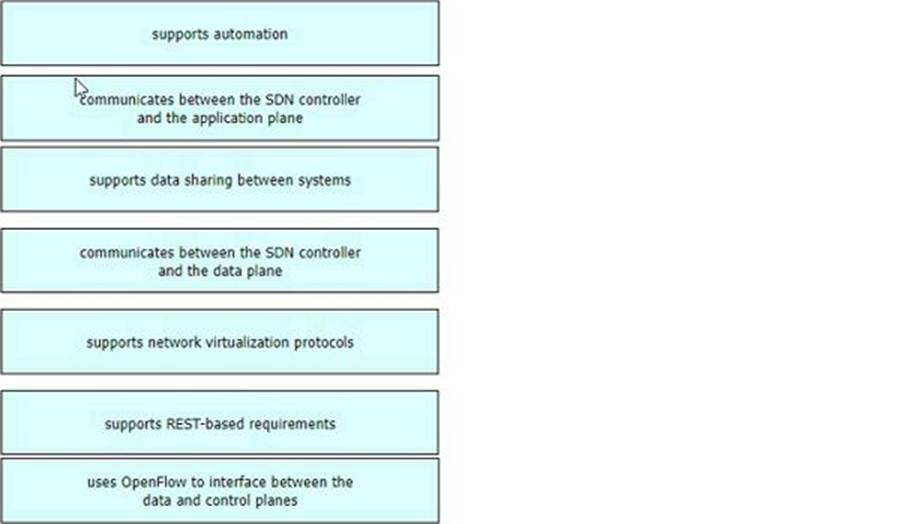
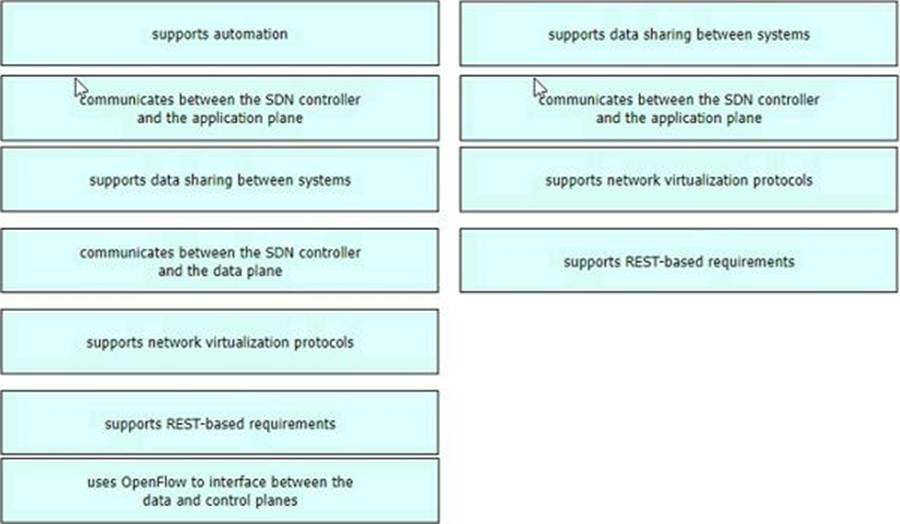
DRAG DROP
Drag and drop the characteristics of northbound APIs from the left onto any position on the right. Not all characteristics are used.
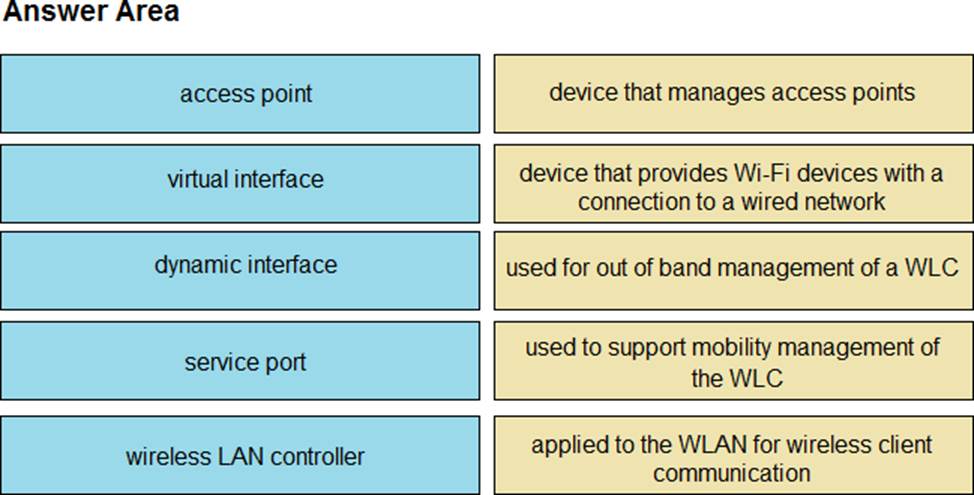
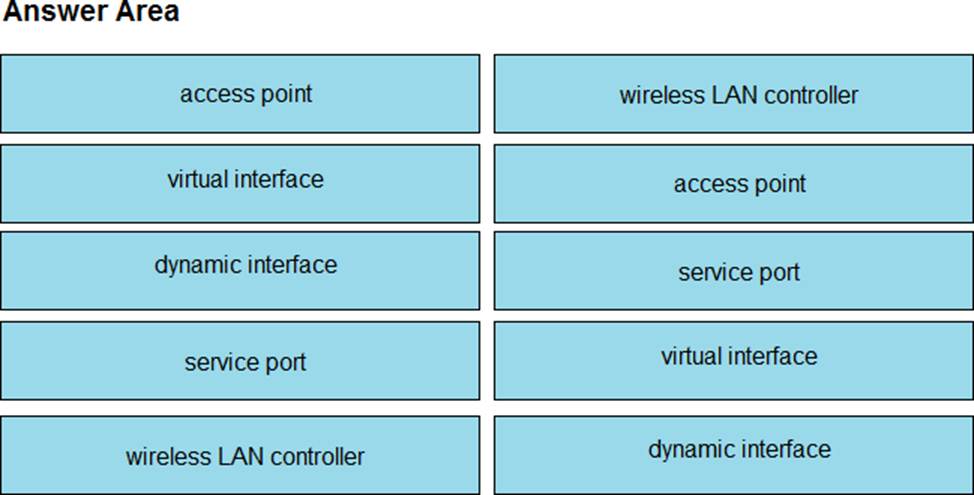
DRAG DROP
Drag and drop the WLAN components from the left onto the correct descriptions on the right.
Which field within the access-request packet is encrypted by RADIUS?
- A . authorized services
- B . authenticator
- C . username
- D . password
