Practice Free 200-301 Exam Online Questions
What is a difference between local AP mode and FiexConnet AP mode?
- A . Local AP mode creates two CAPWAP tunnels per AP to the WLC
- B . FiexConnect AP mode fails to function if the AP loses connectivity with the WLC
- C . FlexConnect AP mode bridges the traffic from the AP to the WLC when local switching is configured
- D . Local AP mode causes the AP to behave as if it were an autonomous AP
What does physical access control regulate?
- A . access to spec fie networks based on business function
- B . access to servers to prevent malicious activity
- C . access 😮 computer networks and file systems
- D . access to networking equipment and facilities
Which function is performed by the collapsed core layer in a two-tier architecture?
- A . enforcing routing policies
- B . marking interesting traffic for data polices
- C . attaching users to the edge of the network
- D . applying security policies
Which is a fact related to FTP?
- A . It uses block numbers to identify and mitigate data-transfer errors
- B . It always operates without user authentication
- C . It relies on the well-known UDP port 69.
- D . It uses two separate connections for control and data traffic
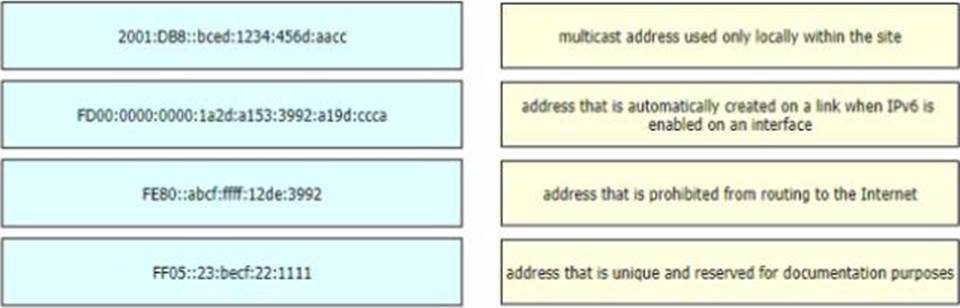
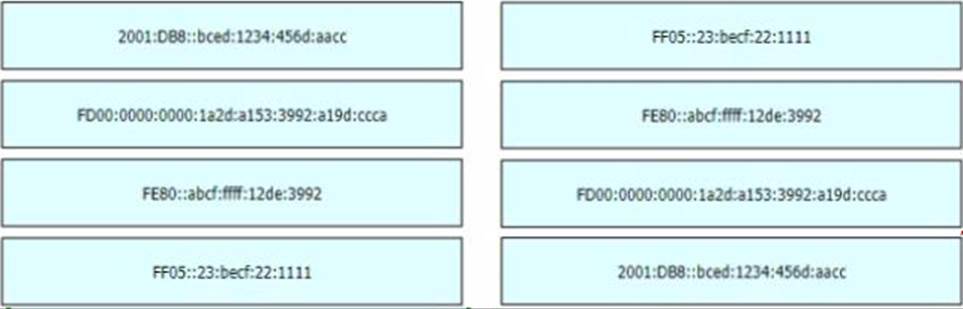
DRAG DROP
Drag and drop the IPv6 address types from the left onto their description on the right.
Refer to the exhibit.
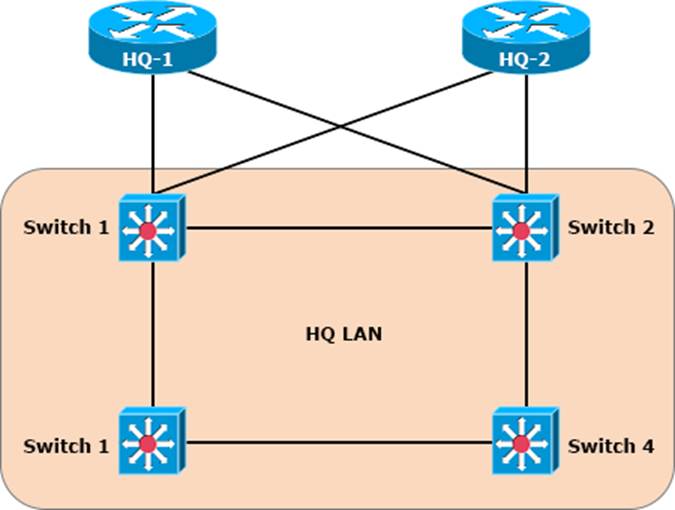
After the election process what is the root bridge in the HQ LAN?
Switch1: 0C.E0.38.57.24.22
Switch2: 0C.0E.15.22.1A.61
Switch3: 0C.0E.15.1D.3C.9A
Switch4: 0C.E0.19.A1.4D.16
- A . Switch 1
- B . Switch 2
- C . Switch 3
- D . Switch 4
C
Explanation:
The root bridge is determined by the lowest bridge ID, which consists of the priority value and the MAC address. Because the priority values of all of the switches are not avalable, the MAC address is used to determine the root bridge. Because S3 has the lowest MAC address, S3 becomes the root bridge.
How does authentication differ from authorization?
- A . Authentication verifies the identity of a person accessing a network, and authorization determines what resource a user can access.
- B . Authentication is used to record what resource a user accesses, and authorization is used to determine what resources a user can access
- C . Authentication is used to determine what resources a user is allowed to access, and authorization is used to track what equipment is allowed access to the network
- D . Authentication is used to verify a person’s identity, and authorization is used to create syslog messages for logins.
What is the difference between 1000BASE-LX/LH and 1000BASE-ZX interfaces?
- A . 1000BASE-ZX is supported on links up to 1000km, and 1000BASE-LX/LH operates over links up to 70 km.
- B . 1000BASE-LX/LH interoperates with multimode and single-mode fiber, and 10008ASE-ZX needs a conditioning patch cable with a multimode.
- C . 1000BASE-LX/LH is supported on links up to 10km, and 1000BASE-ZX operates over links up to 70 km
- D . 1000BASE-ZX interoperates with dual-rate 100M/1G 10Km SFP over multimode fiber, and 1000BASE-LX/LH supports only single-rate.
What is the main difference between traditional networks and controller-based networking?
- A . Controller-based networks increase TCO for the company, and traditional networks require less investment.
- B . Controller-based networks provide a framework for Innovation, and traditional networks create efficiency.
- C . Controller-based networks are open for application requests, and traditional networks operate manually.
- D . Controller-based networks are a closed ecosystem, and traditional networks take advantage of programmability.
When should an engineer implement a collapsed-core architecture?
- A . for small networks with minimal need for growth
- B . the access and distribution layers must be on the same device
- C . for large networks that are connected to multiple remote sites
- D . only when using VSS technology
