Practice Free 200-301 Exam Online Questions
What is a characteristics of a collapsed-core network topology?
- A . It allows the core and distribution layers to run as a single combined layer.
- B . It enables the core and access layers to connect to one logical distribution device over an EtherChannel.
- C . It enables all workstations in a SOHO environment to connect on a single switch with internet access.
- D . It allows wireless devices to connect directly to the core layer, which enables faster data transmission.
Which protocol is used in Software Defined Access (SDA) to provide a tunnel between two edge nodes in different fabrics?
- A . Generic Router Encapsulation (GRE)
- B . Virtual Local Area Network (VLAN)
- C . Virtual Extensible LAN (VXLAN)
- D . Point-to-Point Protocol
Refer to the exhibit.

R1 has taken the DROTHER role in the OSPF DR/BDR election process.
Which configuration must an engineer implement so that R1 is elected as the DR?
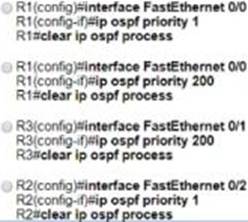
- A . Option A
- B . Option B
- C . Option C
- D . Option D
What is a characteristic of private IPv4 addressing?
- A . traverse the Internet when an outbound ACL is applied
- B . issued by IANA in conjunction with an autonomous system number
- C . composed of up to 65.536 available addresses
- D . used without tracking or registration
What is the purpose of traffic shaping?
- A . to mitigate delays over slow links
- B . to provide fair queuing for buffered flows
- C . to limit the bandwidth that a flow can use to
- D . be a marking mechanism that identifies different flows
C
Explanation:
Traffic shaping retains excess packets in a queue and then schedules the excess for later transmission over increments of time.
What is the purpose of an SSID?
- A . It provides network security
- B . It differentiates traffic entering access posits
- C . It identities an individual access point on a WLAN
- D . It identifies a WLAN
D
Explanation:
“In IEEE 802.11 wireless local area networking standards (including Wi-Fi), a service set is a group of wireless network devices which share a service set identifier (SSID) …
A service set forms a logical network of nodes operating with shared link-layer networking parameters; they form one logical network segment.“
Which command prevents passwords from being stored in the configuration as plain text on a router or switch?
- A . enable secret
- B . service password-encryption
- C . username Cisco password encrypt
- D . enable password
When a WPA2-PSK WLAN is configured in the wireless LAN Controller, what is the minimum number of characters that in ASCll format?
- A . 6
- B . 8
- C . 12
- D . 18
DRAG DROP
Drag and drop the threat-mitigation techniques from the left onto the types of threat or attack they mitigate on the right.
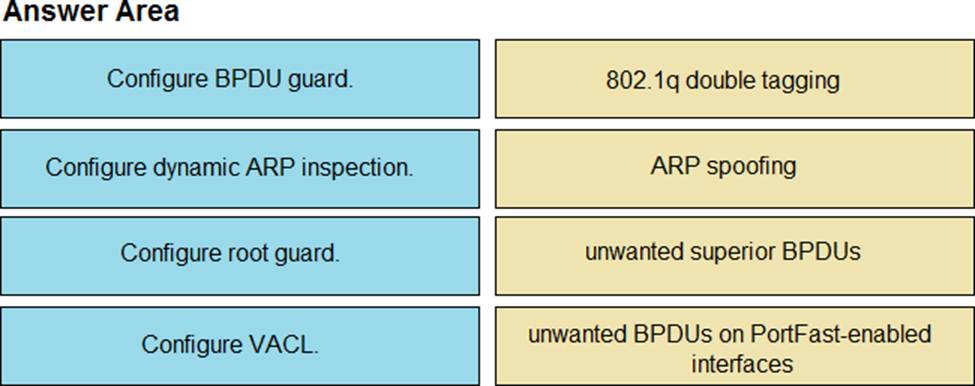
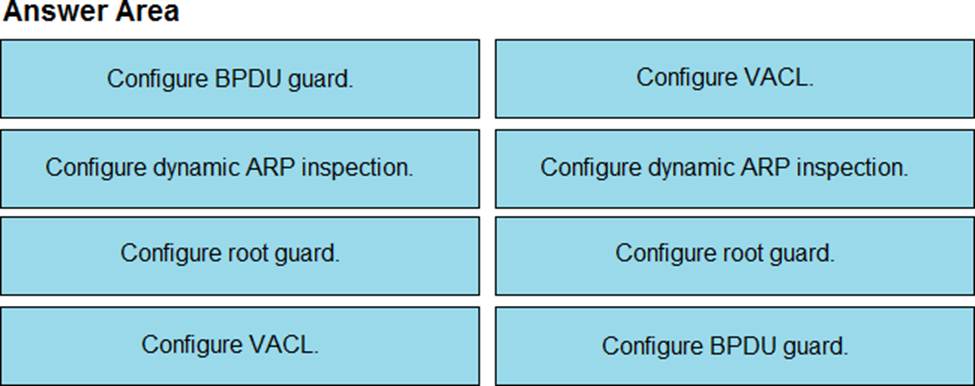
Explanation:
Double-Tagging attack:
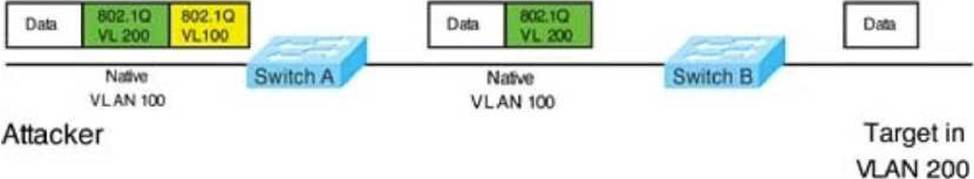
In this attack, the attacking computer generates frames with two 802.1Q tags. The first tag matches the native VLAN of the trunk port (VLAN 10 in this case), and the second matches the VLAN of a host it wants to attack (VLAN 20).
When the packet from the attacker reaches Switch A, Switch A only sees the first VLAN 10 and it matches with its native VLAN 10 so this VLAN tag is removed. Switch A forwards the frame out all links with the same native VLAN 10. Switch B receives the frame with an tag of VLAN 20 so it removes this tag and forwards out to the Victim computer.
Note: This attack only works if the trunk (between two switches) has the same native VLAN as the attacker.
To mitigate this type of attack, you can use VLAN access control lists (VACLs, which applies to all traffic within a VLAN. We can use VACL to drop attacker traffic to specific victims/servers) or implement Private VLANs.
ARP attack (like ARP poisoning/spoofing) is a type of attack in which a malicious actor sends falsified ARP messages over a local area network as ARP allows a gratuitous reply from a host even if an ARP request was not received. This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network. This is an attack based on ARP which is at Layer 2. Dynamic ARP inspection (DAI) is a security feature that validates ARP packets in a network which can be used to mitigate this type of attack.
Refer to the exhibit.
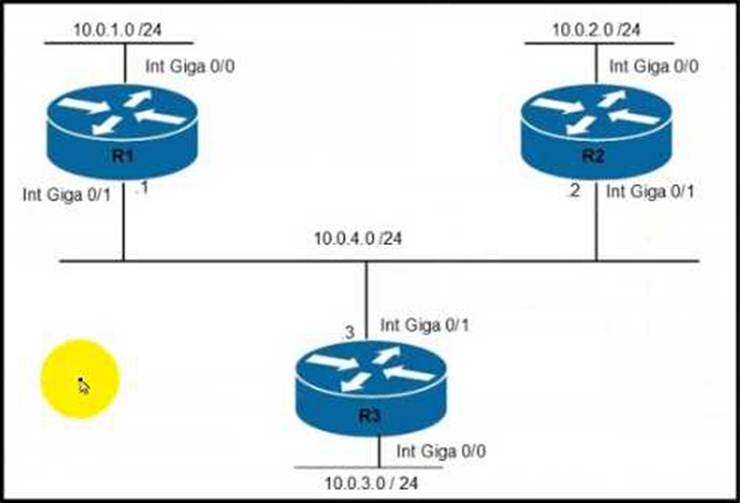
Router R1 must be configured to reach the 10.0.3.0/24 network from the 10.0.1.0/24 segment.
Which command must be used to configure the route?
- A . ip route 10.0.3.0 0.255255.255 10.0.4.2
- B . route add 10.0.3.0 mask 255.255.255.0 10.0.4.3
- C . Ip route 10.0.3.0 255.255.255.0 10.0.4.3
- D . route add 10.0.3.0 0.255.255.255 10.0.4.2
