Practice Free PCCSE Exam Online Questions
What are two alarm types that are registered after alarms are enabled? (Choose two.)
- A . Onboarded Cloud Accounts status
- B . Resource status
- C . Compute resources
- D . External integrations status
Which three actions are required in order to use the automated method within Azure Cloud to streamline the process of using remediation in the identity and access management (IAM) module?
(Choose three.)
- A . Install boto3 & requests library.
- B . Configure IAM Azure remediation script.
- C . Integrate with Azure Service Bus.
- D . Configure IAM AWS remediation script.
- E . Install azure.servicebus & requests library.
Which three actions are required in order to use the automated method within Azure Cloud to streamline the process of using remediation in the identity and access management (IAM) module?
(Choose three.)
- A . Install boto3 & requests library.
- B . Configure IAM Azure remediation script.
- C . Integrate with Azure Service Bus.
- D . Configure IAM AWS remediation script.
- E . Install azure.servicebus & requests library.
Which action must be taken to enable a user to interact programmatically with the Prisma Cloud APIs and for a nonhuman entity to be enabled for the access keys?
- A . Create a role with System Admin and generate access keys.
- B . Create a user with a role that has minimal access.
- C . Create a role with Account Group Read Only and assign it to the user.
- D . Create a role and assign it to the Service Account.
Anomaly policy uses which two logs to identify unusual network and user activity? (Choose two.)
- A . Network flow
- B . Audit
- C . Traffic
- D . Users
What is the purpose of Incident Explorer in Prisma Cloud Compute under the "Monitor" section?
- A . To sort through large amounts of audit data manually in order to identify developing attacks
- B . To store large amounts of forensic data on the host where Console runs to enable a more rapid and effective response to incidents
- C . To correlate individual events to identify potential attacks and provide a sequence of process, file system, and network events for a comprehensive view of an incident
- D . To identify and suppress all audit events generated by the defender *
A customer wants to turn on Auto Remediation.
Which policy type has the built-in CLI command for remediation?
- A . Anomaly
- B . Audit Event
- C . Network
- D . Config
On which cloud service providers can new API release information for Prisma Cloud be received?
- A . AWS. Azure. GCP. Oracle, IBM
- B . AWS. Azure. GCP, IBM, Alibaba
- C . AWS. Azure. GCP. Oracle, Alibaba
- D . AWS. Azure. GCP, IBM
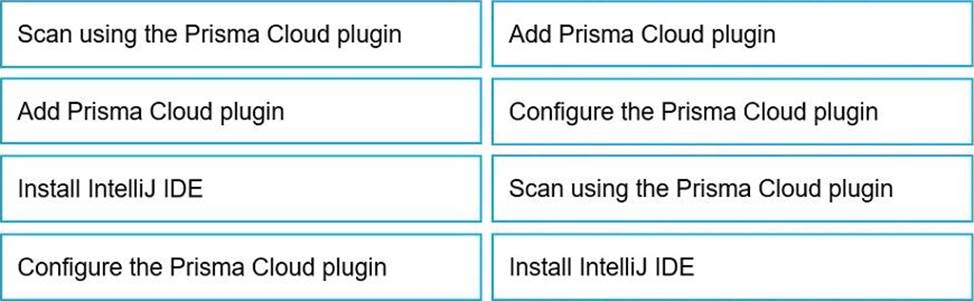
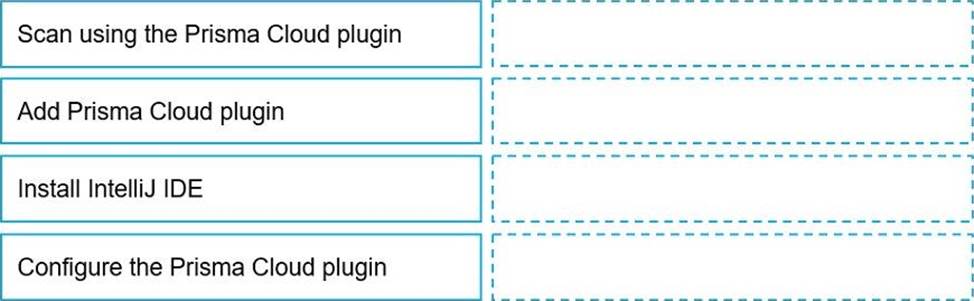
DRAG DROP
Put the steps involved to configure and scan using the IntelliJ plugin in the correct order.
Console is running in a Kubernetes cluster, and you need to deploy Defenders on nodes within this cluster.
Which option shows the steps to deploy the Defenders in Kubernetes using the default Console service name?
- A . From the deployment page in Console, choose pod name for Console identifier, generate DaemonSet file, and apply the DaemonSet to twistlock namespace.
- B . From the deployment page configure the cloud credential in Console and allow cloud discovery to auto-protect the Kubernetes nodes.
- C . From the deployment page in Console, choose twistlock-console for Console identifier, generate DaemonSet file, and apply DaemonSet to the twistlock namespace.
- D . From the deployment page in Console, choose twistlock-console for Console identifier, and run
the curl | bash script on the master Kubernetes node.