Practice Free NSE6_FML-7.2 Exam Online Questions
Refer to the exhibit which displays a list of IBE users on a FortiMail device.

Which statement describes the pre-registered status of the IBE user [email protected]?
- A . The user has received an IBE notification email, but has not accessed the HTTPS URL or attachment yet.
- B . The user was registered by an administrator in anticipation of IBE participation.
- C . The user account has been de-activated, and the user must register again the next time they receive an IBE email.
- D . The user has completed the IBE registration process, but has not yet accessed their IBE email.
What are two disadvantages of configuring the dictionary and DLP scan rule aggressiveness too high?
(Choose two.)
- A . High aggressiveness scan settings do not support executable file types.
- B . It is more resource intensive
- C . More false positives could be detected.
- D . FortiMail requires more disk space for the additional rules.
Which two features are available when you enable HA centralized monitoring on FortiMail? (Choose two.)
- A . Policy configuration changes of all cluster members from the primary device.
- B . Mail statistics of all cluster members on the primary device.
- C . Cross-device log searches across all cluster members from the primary device.
- D . Firmware update of all cluster members from the primary device
In which two places can the maximum email size be overridden on FortiMail? (Choose two.)
- A . IP Policy configuration
- B . Protected Domain configuration
- C . Resource Profile configuration
- D . Session Profile configuration
Refer to the exhibit which shows a detailed history log view.
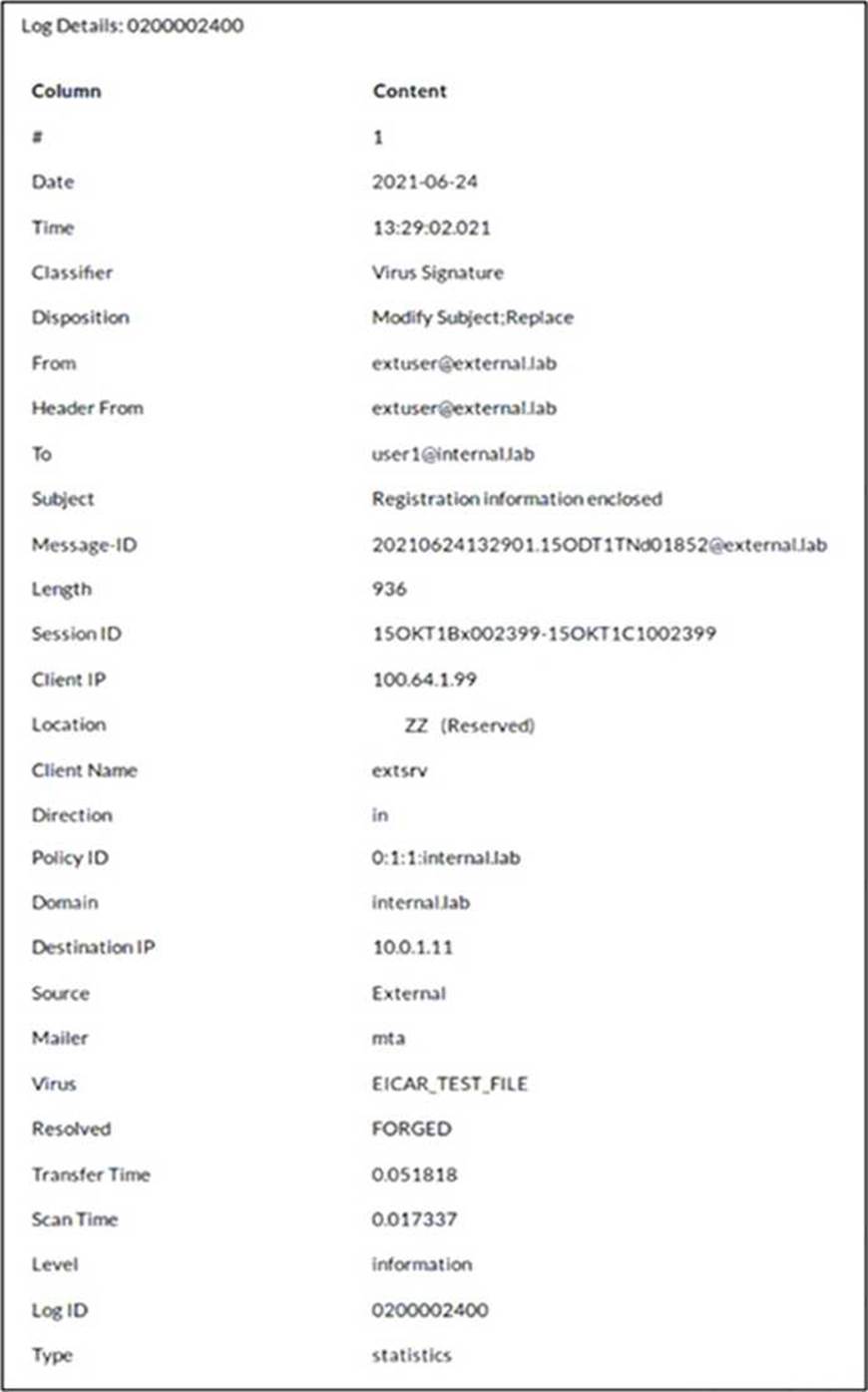
Which two actions did FortiMail take on this email message? (Choose two.)
- A . FortJMail replaced the virus content with a message
- B . FortiMail modified the subject of the email message.
- C . FortiMail forwarded the email to User 1 without scanning.
- D . FortiMail sent the email message to User 1’s personal quarantine.
While reviewing logs, an administrator discovers that an incoming email was processed using policy IDs 0:4:9:INTERNAL.
Which two statements describe what this policy ID means? (Choose two.)
- A . Access control policy number 9 was used.
- B . The FortiMail configuration is missing an access delivery rule.
- C . The email was processed using IP-based policy ID 4.
- D . FortiMail is applying the default behavior for relaying inbound email.
In which FortiMail configuration object can you assign an outbound session profile?
- A . Outbound recipient policy
- B . Inbound recipient policy
- C . IP policy
- D . Access delivery rule
Which statement about how impersonation analysis identifies spoofed email addresses is correct?
- A . It uses behavior analysis to detect spoofed addresses.
- B . It uses DMARC validation to detect spoofed addresses.
- C . It maps the display name to the correct recipient email address
- D . It uses SPF validation to detect spoofed addresses.
Refer to the exhibit which displays a history log entry.

Why does the last field show SYSTEM in the Policy ID column?
- A . The email was dropped by a system blocklist.
- B . It is an inbound email.
- C . The email matched a system-level authentication policy.
- D . The email did not match a recipient-based policy.
Refer to the exhibits, which display a topology diagram (Topology) and two FortiMail device configurations (FML1 Configuration and FML2 Configuration).
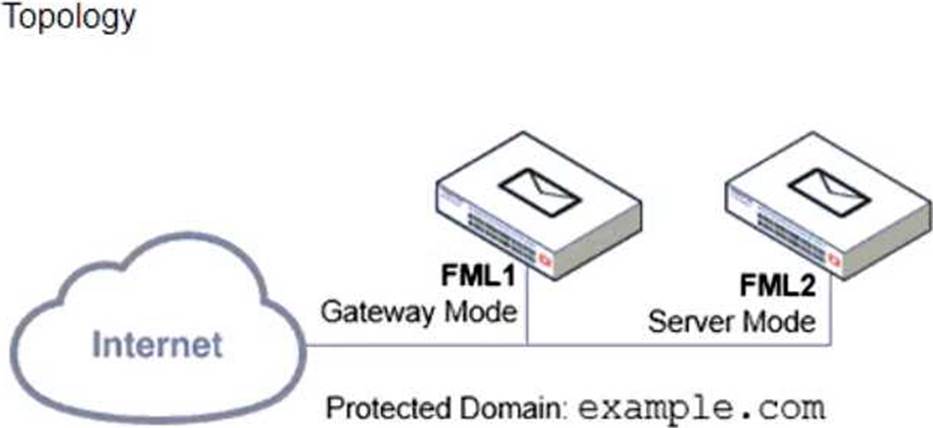
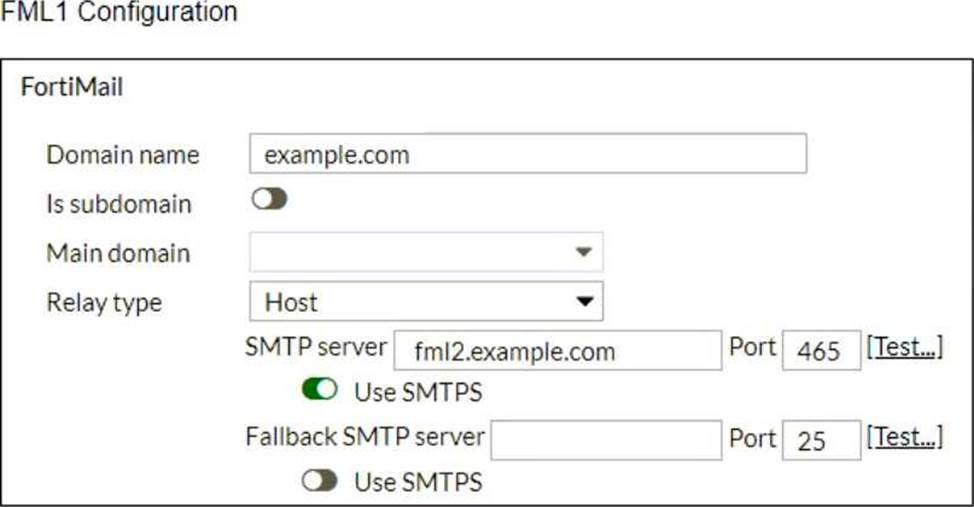
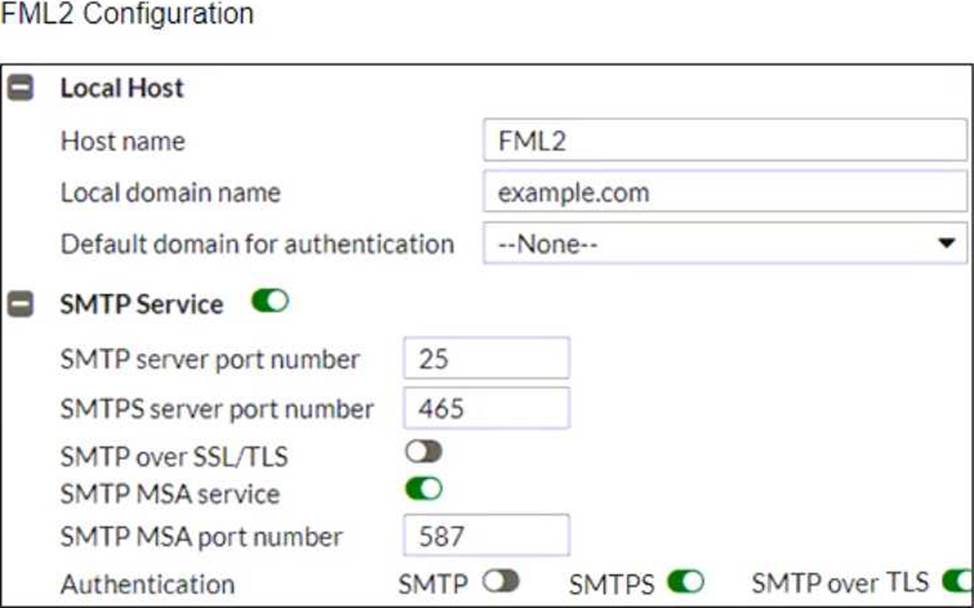
What is the expected outcome of SMTP sessions sourced from FML1 and destined for FML2?
- A . FML1 will fail to establish any connection with FML2.
- B . FML1 will attempt to establish an SMTPS session with FML2. but fail and revert to standard SMTP.
- C . FML1 will send the STARTTLS command in the SMTP session, which will be rejected by FML2.
- D . FML1 will successfully establish an SMTPS session with FML2.
